Hacking And Penetration Testing A Beginners Guide Pptx

Hacking And Penetration Testing A Beginners Guide Pptx The document provides a comprehensive overview of hacking, cyber security, and penetration testing, highlighting the significance of vulnerability assessment in protecting systems from cyber crimes. The document provides an overview of ethical hacking and penetration testing, including definitions, types of hackers, and the importance of these practices in enhancing cybersecurity.
The Basics Of Hackingand Penetration Testing Learn about the definition of a penetration tester, the importance of penetration testing, origins of penetration testing, goals of a penetration tester, overview of pen testing evolution, types of hackers, cybercrime examples, and legal issues in ethical hacking. Once a pen tester is in possession of the necessary permissions to conduct their activities, the actual testing can take place. there are a myriad of ways to proceed with testing at this point, and each is valid in its own way. Most penetration testers with years of experience rarely use vulnerability scanners – they rely more on their knowledge and experience – business knowledge is also a key factor. Aim of this presentation to introduce basic application penetration testing techniques. it is not as difficult to get into as you might think – hopefully we will bust some myths. we will mainly use owasp projects, which will enable you to setup a safe home training lab. expectations.
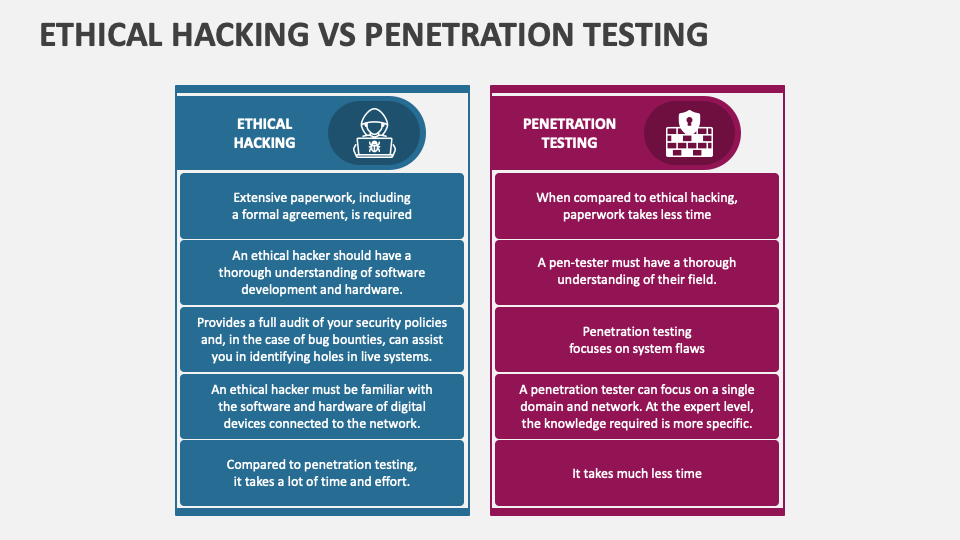
Ethical Hacking Vs Penetration Testing Powerpoint And Google Slides Most penetration testers with years of experience rarely use vulnerability scanners – they rely more on their knowledge and experience – business knowledge is also a key factor. Aim of this presentation to introduce basic application penetration testing techniques. it is not as difficult to get into as you might think – hopefully we will bust some myths. we will mainly use owasp projects, which will enable you to setup a safe home training lab. expectations. It is a ready made powerpoint template in tabular format that exhibits your real world observations and meaning for each of the ethical hacking and penetration testing concepts. This document provides an overview of penetration testing, describing its purpose, types (black box and white box testing), and essential steps involved in the process. it covers common types of cyber attacks and vulnerabilities, as well as tools and techniques used by penetration testers. Introduction to basics of ethical hacking and penetration testing download as a pptx, pdf or view online for free. The document discusses the dual nature of hacking, highlighting both negative and positive aspects. it explores ethical hacking as a means to protect computer networks and argues that some hacking motivations can be justified for the greater good.

The Basics Of Hacking And Penetration Testing Tools Pdf It is a ready made powerpoint template in tabular format that exhibits your real world observations and meaning for each of the ethical hacking and penetration testing concepts. This document provides an overview of penetration testing, describing its purpose, types (black box and white box testing), and essential steps involved in the process. it covers common types of cyber attacks and vulnerabilities, as well as tools and techniques used by penetration testers. Introduction to basics of ethical hacking and penetration testing download as a pptx, pdf or view online for free. The document discusses the dual nature of hacking, highlighting both negative and positive aspects. it explores ethical hacking as a means to protect computer networks and argues that some hacking motivations can be justified for the greater good.
Comments are closed.