Hacking An Automotive Ecu
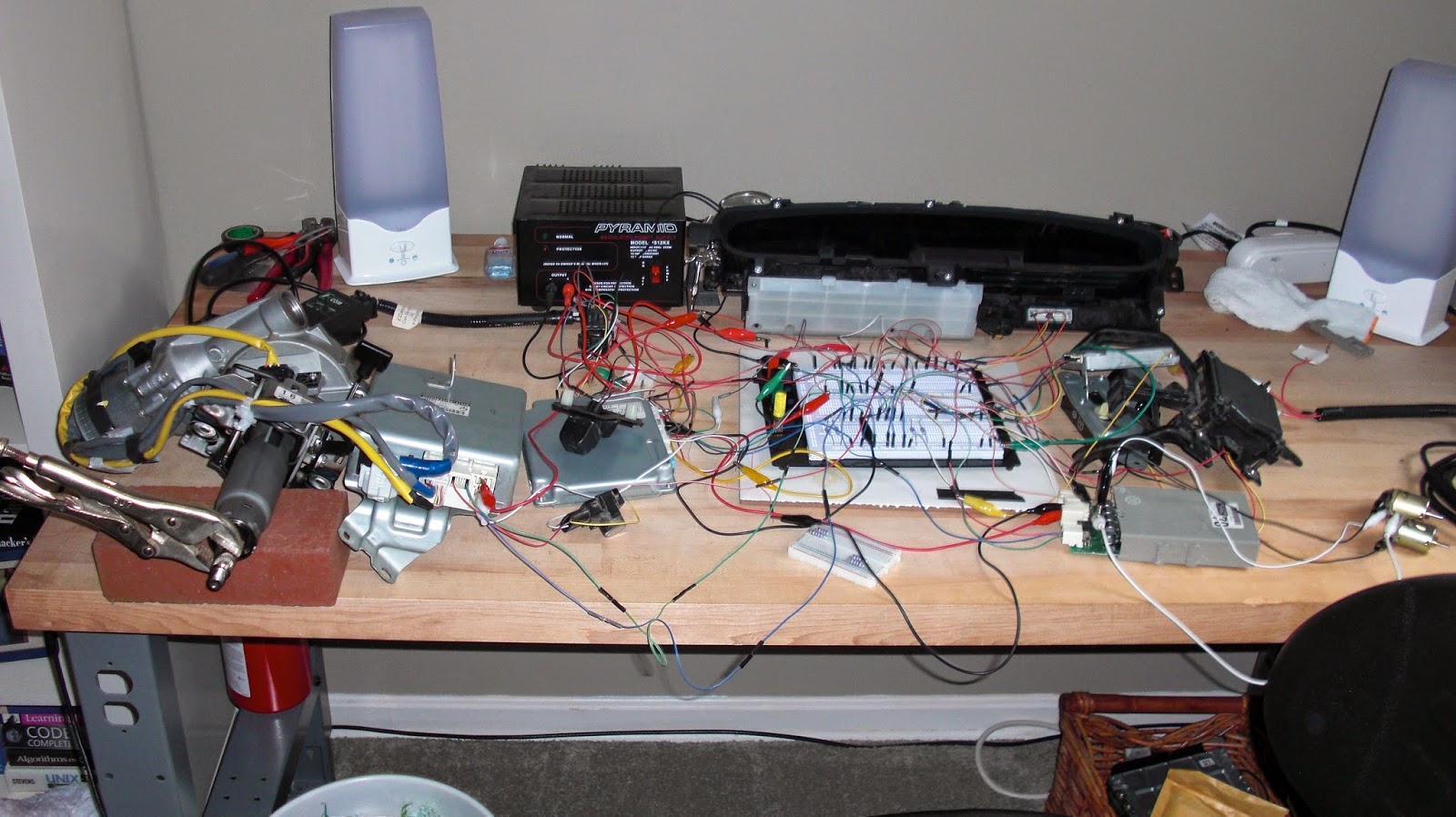
Car Hacking 2 The Content Ioactive The first step in attacking the ecu or any embedded system in a vehicle is to analyze the target circuit board. i touched upon circuit board analysis in chapter 7, but in this chapter, i’ll go into more detail about how electronics and chips work. i’ll introduce you to techniques that can be applied to any embedded system in the vehicle. Automotive hacking is the exploitation of vulnerabilities within the software, hardware, and communication systems of automobiles. modern automobiles contain hundreds of on board computers processing everything from vehicle controls to the infotainment system.
What Is An Ecu Car Electronic Control Units From Functions To Problems There are several methods through which hackers can exploit vulnerabilities within a car’s ecu. one common approach is to gain physical access to the vehicle and connect a malicious device to the ecu’s diagnostic port. Growing standardization in ecu components and software development undertaken by groups like autosar has increased the level of protection against such threats, but still much remains to be done to completely secure them against hacking. In the end, depending on how ambitious the researcher happens to be, we even discuss how to hook up these ecus and other equipment on a go cart in order to test attacks against a moving vehicle, still for less than a tenth of a cost of an automobile. At hardwear.io this year i spoke about extracting the flash memory from an automotive ecu. the talk is called "bam bam! you can do it!" and it's about the process i went through and the.
Top 21 Automotive Udemy Courses To Improve Skills And Get Job In In the end, depending on how ambitious the researcher happens to be, we even discuss how to hook up these ecus and other equipment on a go cart in order to test attacks against a moving vehicle, still for less than a tenth of a cost of an automobile. At hardwear.io this year i spoke about extracting the flash memory from an automotive ecu. the talk is called "bam bam! you can do it!" and it's about the process i went through and the. Many can datasets do not—to our knowledge—account for the defenses that automotive manufacturers have begun to incorporate into can buses and ecus. in our spoofing attacks, we encountered such defenses and crafted attacks capable of eluding them. A service with potential vulnerabilities is implemented on the ecu and attacks to exploit such vulnerabilities are demonstrated. the tricore architecture is analyzed to find what types of attacks are possible, what the desired targets are and how attacks could be performed over the can network. A rust based cross platform ecu diagnostics and car hacking application, utilizing the passthru protocol. We propose a novel authentication system called shadowauth that overcomes the aforementioned challenges by offering backwardcompatible packet authentication to ecus without requiring ecu firmware source code.
Comments are closed.