Hackers Guide To Uart Root Shells
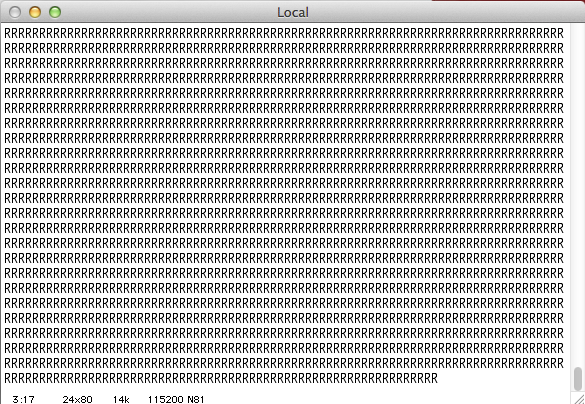
Uart Root Shell On Commercial Devices Threatdown By Malwarebytes This entry in the hardware hacking 101 series will explain what you need to know about uart serial communication, and walk through the process of finding and connecting to the uart port on a router. The uart is a hardware serial bus; it’s easy to access and very interesting to look at. depending on the device and how it was hardened by its manufacturer, the uart can reveal a lot of useful information or even an unprotected, interactive root shell.

Uart Root Shell On Commercial Devices Malwarebytes Labs The best breakdown and walk through tutorial on identifying uart pins on a hardware device, decoding digital signals to identify the baud rate, and more can be seen in the flashback team’s “ hacker’s guide to uart root shells ”. For some time, i’ve been thinking about why i haven’t written about what i’ve been researching, so i decided to start this blog showing how to access a router’s shell through a uart communication interface. If you’re lucky you can get full shell access over uart. in the first part of a teardown of a d link dcs 932l internet enabled security camera, i looked at extracting firmware from flash memory. In this post, we will review the process of accessing and dumping the firmware of a device through an alternative serial interface called uart (universal asynchronous receiver transmitter).
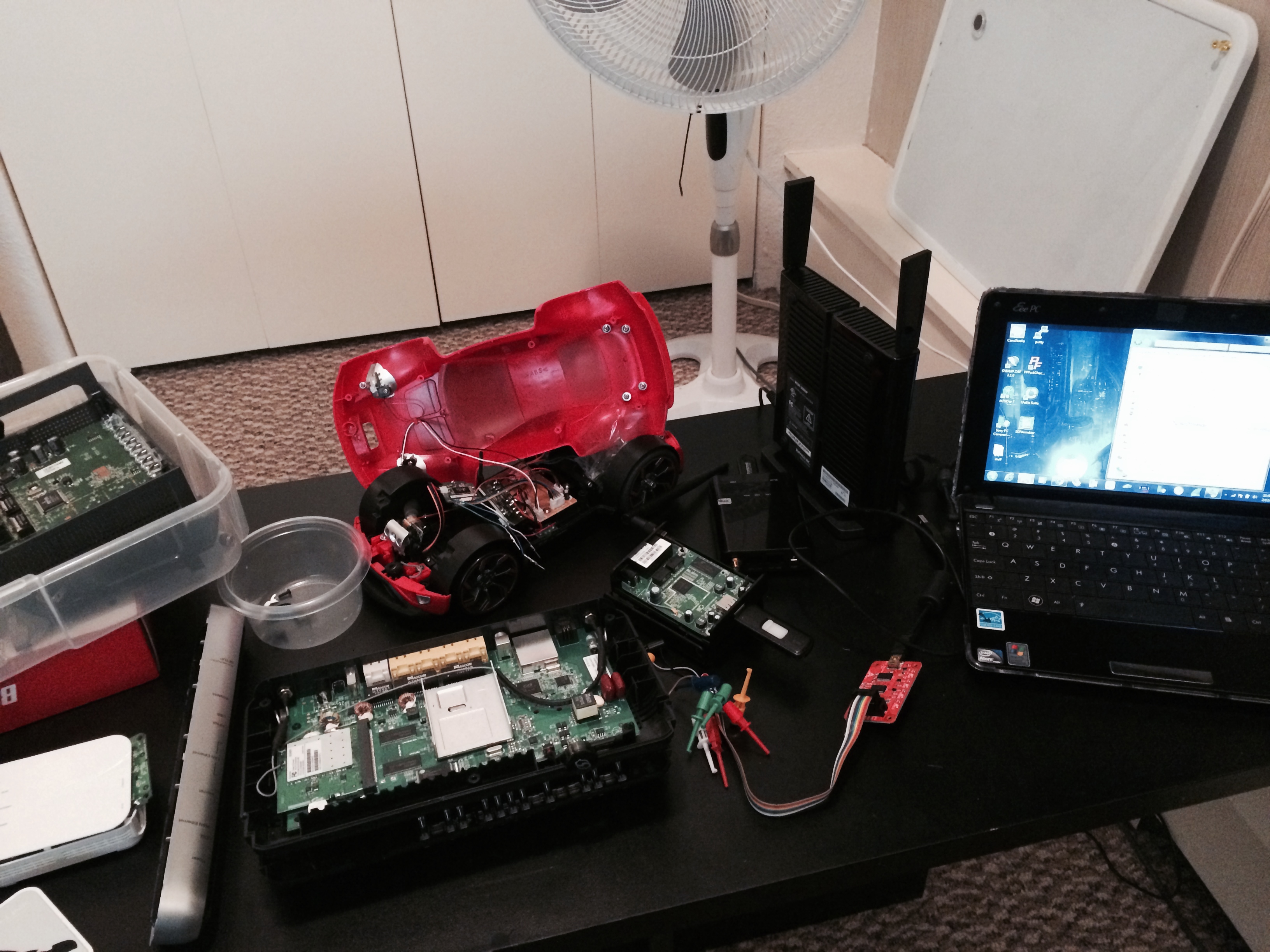
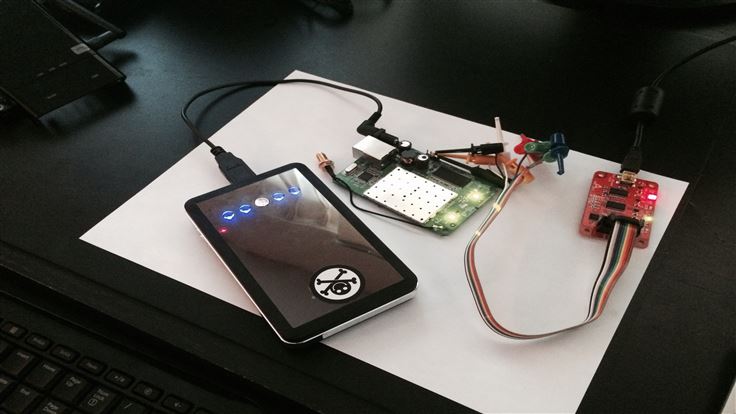
Uart Root Shell On Commercial Devices Malwarebytes Labs If you’re lucky you can get full shell access over uart. in the first part of a teardown of a d link dcs 932l internet enabled security camera, i looked at extracting firmware from flash memory. In this post, we will review the process of accessing and dumping the firmware of a device through an alternative serial interface called uart (universal asynchronous receiver transmitter). Many production devices leave serial debugging ports enabled, allowing attackers to gain root shells and full system control. this article explores uart exploitation, key commands, and mitigation strategies. Unlike many iot devices where uart pins must be identified through testing and reverse engineering, the oker g955v1 made things easy. the uart interface was clearly labeled on an unpopulated 4 pin header on the main pcb:. Next up in our series on getting started with hardware hacking, we dive into uart connections and even grab a shell on our raspberry pi device. In this article, we dive into the world of iot device hacking, with a specific focus: gaining a shell on a target device. this kind of access can open the door to understanding how the device works internally, uncovering misconfigurations, and learning more about embedded linux systems.
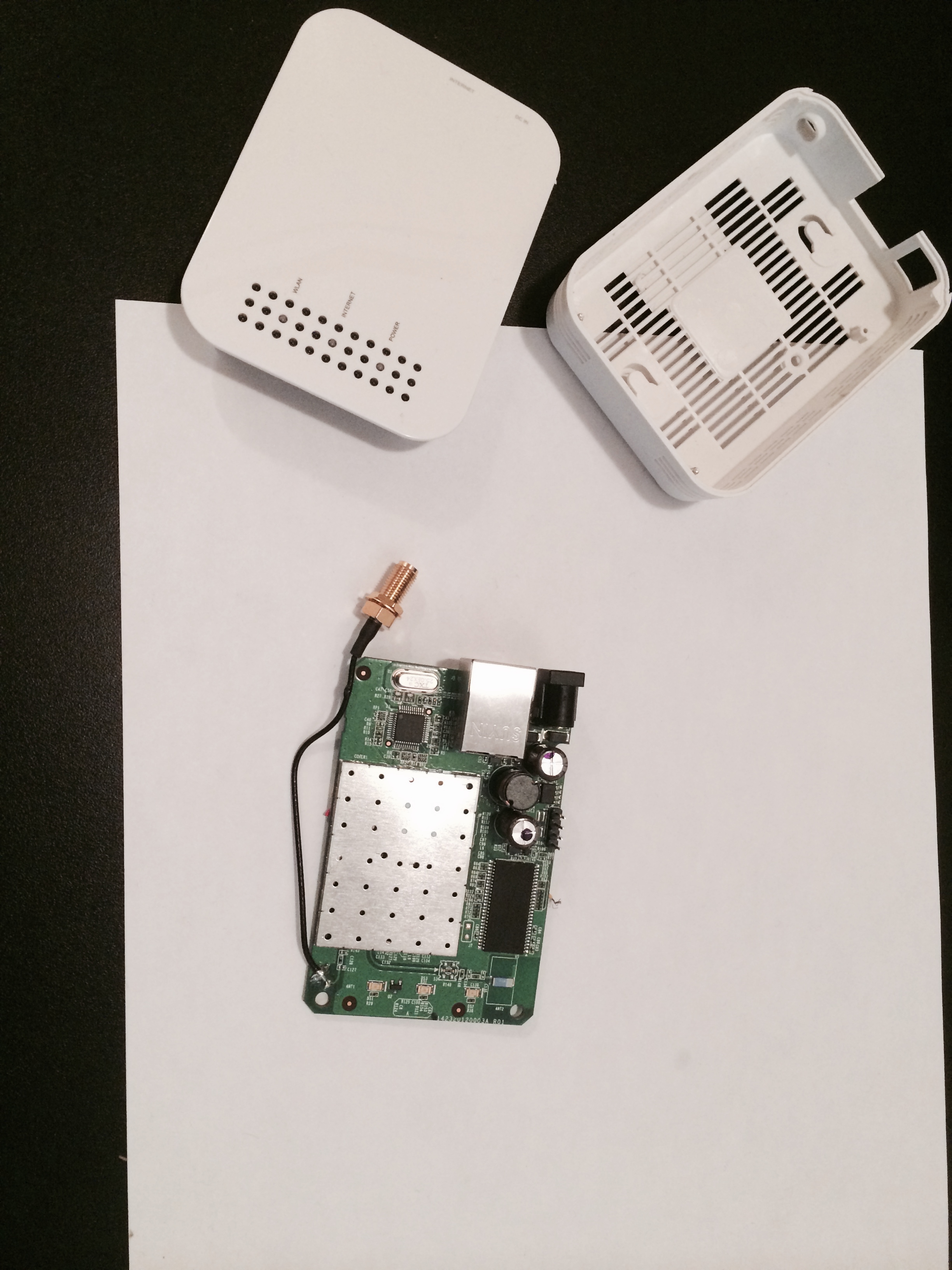
Uart Root Shell On Commercial Devices Malwarebytes Labs Many production devices leave serial debugging ports enabled, allowing attackers to gain root shells and full system control. this article explores uart exploitation, key commands, and mitigation strategies. Unlike many iot devices where uart pins must be identified through testing and reverse engineering, the oker g955v1 made things easy. the uart interface was clearly labeled on an unpopulated 4 pin header on the main pcb:. Next up in our series on getting started with hardware hacking, we dive into uart connections and even grab a shell on our raspberry pi device. In this article, we dive into the world of iot device hacking, with a specific focus: gaining a shell on a target device. this kind of access can open the door to understanding how the device works internally, uncovering misconfigurations, and learning more about embedded linux systems.
Uart Root Shell On Commercial Devices Malwarebytes Labs Next up in our series on getting started with hardware hacking, we dive into uart connections and even grab a shell on our raspberry pi device. In this article, we dive into the world of iot device hacking, with a specific focus: gaining a shell on a target device. this kind of access can open the door to understanding how the device works internally, uncovering misconfigurations, and learning more about embedded linux systems.
Comments are closed.