Hackerone Gitlab Server Exploit Using Path Traversal Install Setup Gitlab Server On Kali
How To Install Gitlab On Your Own Server Lotogo A path traversal issue in gitlab package registry api allow an attacker to write any file at any location writable to user git in a gitlab server. ### steps to reproduce 1. An unauthenticated malicious user can use a path traversal vulnerability to read arbitrary files on the server when an attachment exists in a public project nested within at least five groups.
How To Install Gitlab On Your Own Server Routekop A vulnerability has been discovered in gitlab that could allow an attacker to read arbitrary files on the server. the vulnerability, which has been assigned the cve identifier cve 2023 2825, affects gitlab community and enterprise edition version 16.0.0. An unauthenticated malicious user can use a path traversal vulnerability to read arbitrary files on the server when an attachment exists in a public project nested within at least five groups. An issue has been discovered in gitlab ce ee affecting only version 16.0.0. an unauthenticated malicious user can use a path traversal vulnerability to read arbitrary files on the server when an attachment exists in a public project nested within at least five groups. With this bug, a stranger on the internet can poke around and grab files straight off your machine, gaining knowledge about how your server runs, potentially picking up passwords, keys, and setting the stage for deeper attacks! this is a classic path traversal vulnerability.

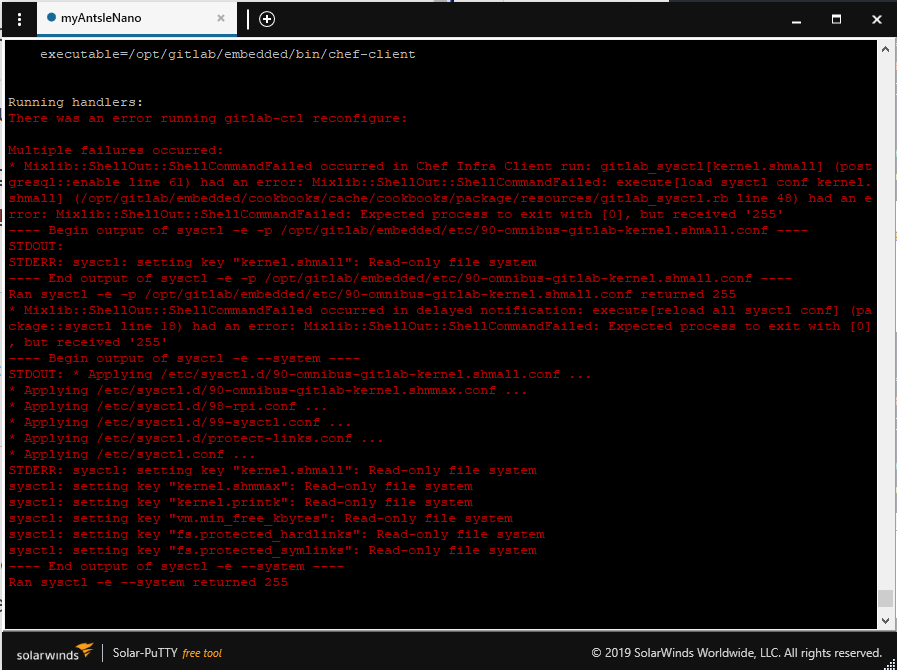
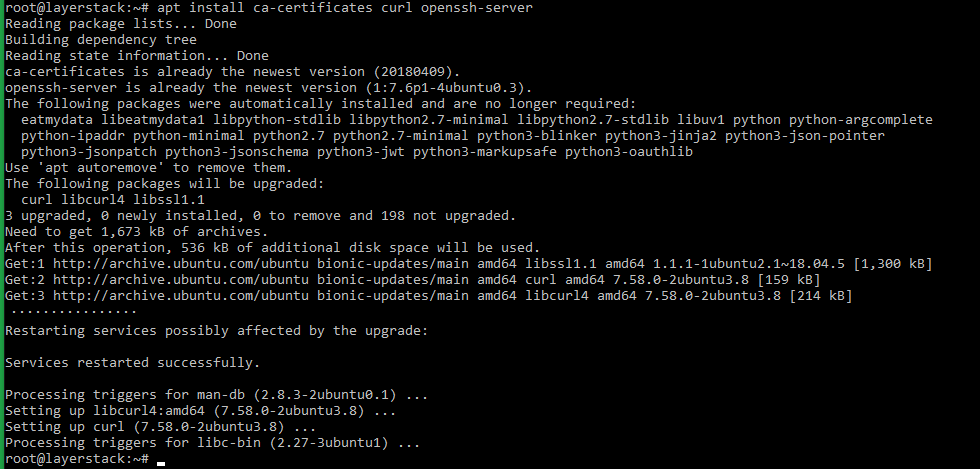
Install Gitlab Container Registry And Configure Https Cert An issue has been discovered in gitlab ce ee affecting only version 16.0.0. an unauthenticated malicious user can use a path traversal vulnerability to read arbitrary files on the server when an attachment exists in a public project nested within at least five groups. With this bug, a stranger on the internet can poke around and grab files straight off your machine, gaining knowledge about how your server runs, potentially picking up passwords, keys, and setting the stage for deeper attacks! this is a classic path traversal vulnerability. We will guide you through the steps to exploit this gitlab cve, highlighting its impact and the necessity of timely patching. cve 2023 2825, as described by gitlab’s advisory, is a path traversal issue that can be taken advantage of by an unauthenticated malicious user. An arbitrary path traversal vulnerability has been recently reported in the gitlab community edition (ce) and enterprise edition (ee) affecting version 16.0.0. it is because of improper limitation of a pathname to a restricted directory. In this write up we’ll break down how the vulnerability worked why it happened and how you can hunt for similar bugs. a path traversal issue in gitlab’s package registry api allowed an attacker to write arbitrary files anywhere writable by the git user on the gitlab server. ### vulnerable gitlab link : hub.docker layers gitlab gitlab ce 12.8.1 ce.0 images sha256 01325161649a28155d8857e4f47462d2bf9406d612c11b8929d2482b.

Gitlab Vulnerability Exploit Detected Darktrace Blog We will guide you through the steps to exploit this gitlab cve, highlighting its impact and the necessity of timely patching. cve 2023 2825, as described by gitlab’s advisory, is a path traversal issue that can be taken advantage of by an unauthenticated malicious user. An arbitrary path traversal vulnerability has been recently reported in the gitlab community edition (ce) and enterprise edition (ee) affecting version 16.0.0. it is because of improper limitation of a pathname to a restricted directory. In this write up we’ll break down how the vulnerability worked why it happened and how you can hunt for similar bugs. a path traversal issue in gitlab’s package registry api allowed an attacker to write arbitrary files anywhere writable by the git user on the gitlab server. ### vulnerable gitlab link : hub.docker layers gitlab gitlab ce 12.8.1 ce.0 images sha256 01325161649a28155d8857e4f47462d2bf9406d612c11b8929d2482b.
Comments are closed.