Hack Every Api Kiterunner Hacker Tools
Thebinarybot S Guide To Api Hacking Hack every api! kiterunner hacker tools. 👨💻🛠️ in this week's episode of hacker tools, we will take a look at kiterunner.00:00 introduction00:15 why do we need api. A curated collection of 60 open source tools for api security testing, penetration testing, and vulnerability research. organized by api type and functionality.

Guide ёяул How To Hack Api In 60 Minutes Or Api Threats Simulation With Kiterunner is a powerful tool to help you uncover all secret routes apis hold. mastering this will allow you to find vulnerabilities on endpoints unknown to others!. Arjun hacker tools,002 intercept http traffic with burp proxy,002 caido hacker tools,007 fuzzing for beginners!. By collating a dataset of swagger specifications and condensing it into our own schema, kiterunner can use this dataset to bruteforce api endpoints by sending the correct http method, headers, path, parameters, and values for each request it sends. Welcome to the less traveled path of api penetration testing, where each day is a new adventure and every api holds secrets waiting to be uncovered. if you’re like me, constantly poking around in the digital shadows for those elusive vulnerabilities, you’ve come to the right place.
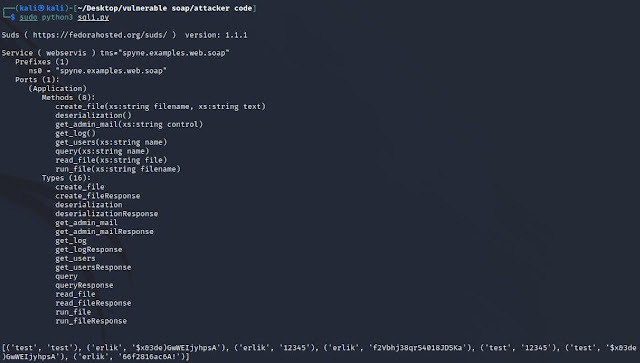
тшг Kitploit Hacker Tools On Twitter Erlik Vulnerable Soap Service By collating a dataset of swagger specifications and condensing it into our own schema, kiterunner can use this dataset to bruteforce api endpoints by sending the correct http method, headers, path, parameters, and values for each request it sends. Welcome to the less traveled path of api penetration testing, where each day is a new adventure and every api holds secrets waiting to be uncovered. if you’re like me, constantly poking around in the digital shadows for those elusive vulnerabilities, you’ve come to the right place. Kiterunner is a contextual content discovery tool for modern web applications and apis, excelling in route endpoint bruteforcing. Kiterunner is a robust tool designed for effective content discovery and api endpoint bruteforcing. its ability to perform rapid content discovery and negotiate routes in modern web applications makes it a key tool to add to your arsenal. Download our api hacking cheat sheet (pdf) now, keep it at your fingertips, and use it to identify hidden vulnerabilities, map exposed endpoints, and secure your apis before attackers strike. Pentesting apis involves a structured approach to uncovering vulnerabilities. this guide encapsulates a comprehensive methodology, emphasizing practical techniques and tools.
Comments are closed.