Gpg Getting Started 1 2

Gpg Getting Started 1 2 When getting started using gnupg it is important to realize that you need not securely communicate with every one of your correspondents. start with a small circle of people, perhaps just yourself and one or two others who also want to exercise their right to privacy. Gpg getting started 1 2 the world is full of signing and encryption methods. there is one, that is especially useful in open source software. gpg can be used to sign mails, git commits, container image encryption and much more. let's set it up!.
Tutorial Gpg 1 This guide provides a comprehensive overview for setting up gpg on windows (using the gpg4win ui tool), macos, and linux with modern ecc encryption, managing keys, and securely encrypting decrypting files while following best practices for encryption security. Gnupg, also known as gpg, can be used to encrypt files for confidentiality or sign files for integrity and authenticity. this article explores the minimum commands needed to encrypt a file or check a signature. Master the gpg command in linux with our comprehensive guide. learn to encrypt, decrypt, sign files, manage gpg keys, and integrate with tools like git. perfect for devops and sysadmins. It’s easy to get started with gpg, and you can be on your way with using it in a matter of minutes. in this tutorial, i’ll show you how to encrypt and decrypt files with gpg. this is a simple tutorial, and you may try all of it to practice on your linux system as well.

Getting Started With Gpg Gnupg Master the gpg command in linux with our comprehensive guide. learn to encrypt, decrypt, sign files, manage gpg keys, and integrate with tools like git. perfect for devops and sysadmins. It’s easy to get started with gpg, and you can be on your way with using it in a matter of minutes. in this tutorial, i’ll show you how to encrypt and decrypt files with gpg. this is a simple tutorial, and you may try all of it to practice on your linux system as well. This chapter is a quick start guide that covers the core functionality of gnupg. this includes keypair creation, exchanging and verifying keys, encrypting and decrypting documents, and authenticating documents with digital signatures. The guide describes how to generate gpg2 (gnupg 2) key pair, sign and verify commits on linux and macos platforms using git. install gnupg 2. generate your gpg key. enter a pass phrase twice. the default key ring path on linux is home $user .gnupg pubring.kbx and macos is users $user .gnupg pubring.kbx. This exploration highlights the versatility of gpg in handling various tasks — from key generation to data encryption and decryption, all essential for secure digital communication and file management. This reference guide is to help new users of the gnu privacy guard (gpg or gnup) 1 command line tool. its originally intended audience was the students and teaching assistants of northeastern university's khoury college of computer and information science's cy2550 course 2, aka foundations of cybersecurity.
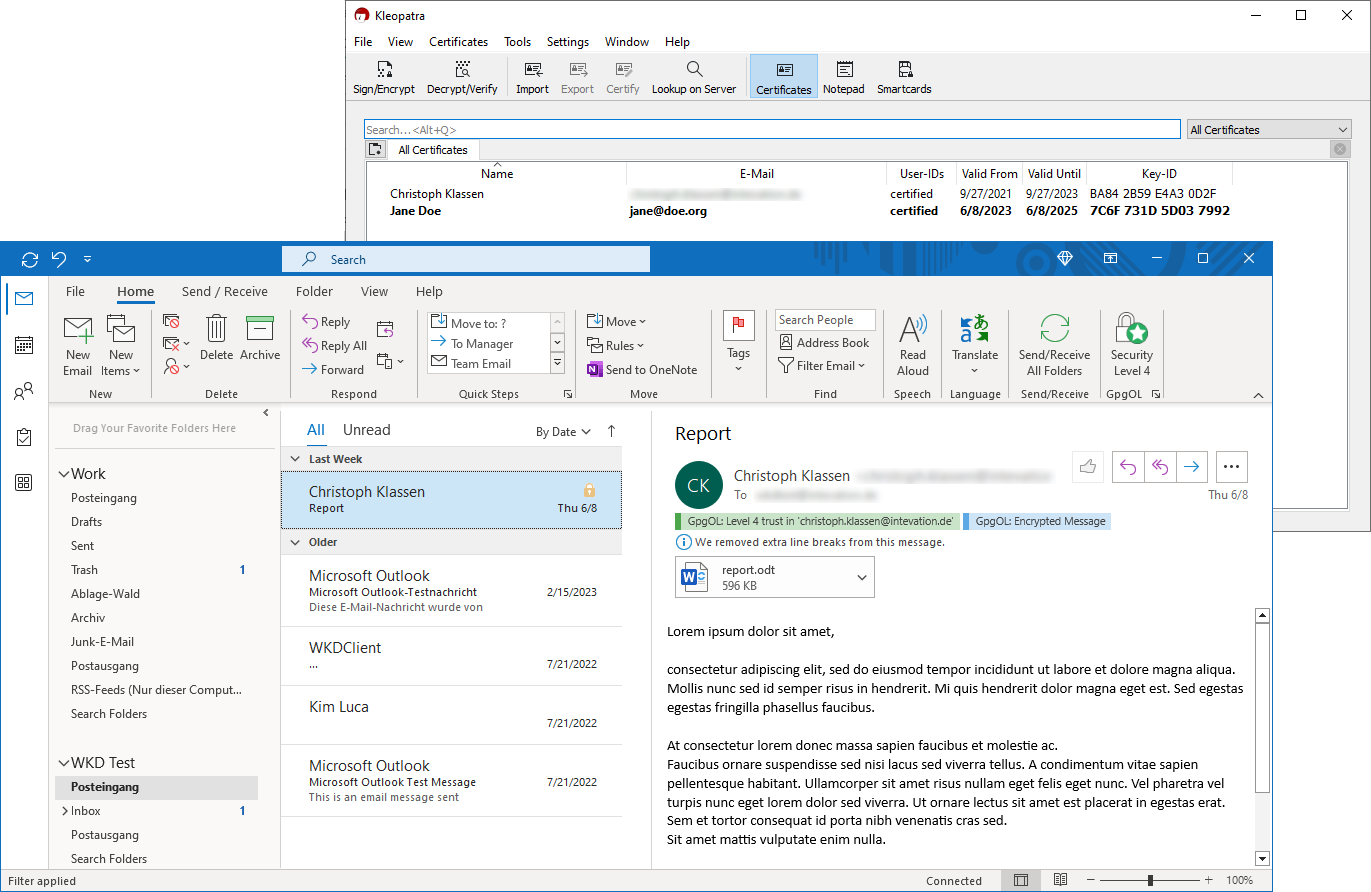
Gpg4win Secure Email And File Encryption With Gnupg For Windows This chapter is a quick start guide that covers the core functionality of gnupg. this includes keypair creation, exchanging and verifying keys, encrypting and decrypting documents, and authenticating documents with digital signatures. The guide describes how to generate gpg2 (gnupg 2) key pair, sign and verify commits on linux and macos platforms using git. install gnupg 2. generate your gpg key. enter a pass phrase twice. the default key ring path on linux is home $user .gnupg pubring.kbx and macos is users $user .gnupg pubring.kbx. This exploration highlights the versatility of gpg in handling various tasks — from key generation to data encryption and decryption, all essential for secure digital communication and file management. This reference guide is to help new users of the gnu privacy guard (gpg or gnup) 1 command line tool. its originally intended audience was the students and teaching assistants of northeastern university's khoury college of computer and information science's cy2550 course 2, aka foundations of cybersecurity.

Gpg Man Linux Command Library This exploration highlights the versatility of gpg in handling various tasks — from key generation to data encryption and decryption, all essential for secure digital communication and file management. This reference guide is to help new users of the gnu privacy guard (gpg or gnup) 1 command line tool. its originally intended audience was the students and teaching assistants of northeastern university's khoury college of computer and information science's cy2550 course 2, aka foundations of cybersecurity.
Comments are closed.