Gnupg Command Line Example

Gnupg Pdf Command Line Interface Key Cryptography Normally, gnupg will calculate when this is required and do it automatically unless no auto check trustdb is set. this command can be used to force a trust database check at any time. the processing is identical to that of update trustdb but it skips keys with a not yet defined "ownertrust". Comprehensive command line reference for gnupg operations including key management, encryption, and signing.

Gnupg Cheatsheet Pdf Cyberspace Cryptography Gnupg is an encryption module that uses openpgp at its core. pgp stands for pretty good privacy. it is an encryption program that provides authentication and cryptographic privacy for data communication. One page guide to gnupg: usage, examples, and more. gnupg is a complete and free implementation of the openpgp standard. A simple cheat sheet for gnupg commands to help you generate, export, and manage keys with ease. perfect for occasional users. stay secure!. First, we need to create a pgp key pair using gnupg. we'll use the full key generation command for more control over options. 1. key type selection: 2. key size: 3. expiration: 4. user id information: 5. passphrase: choose a secure passphrase when prompted (you'll need this later!).
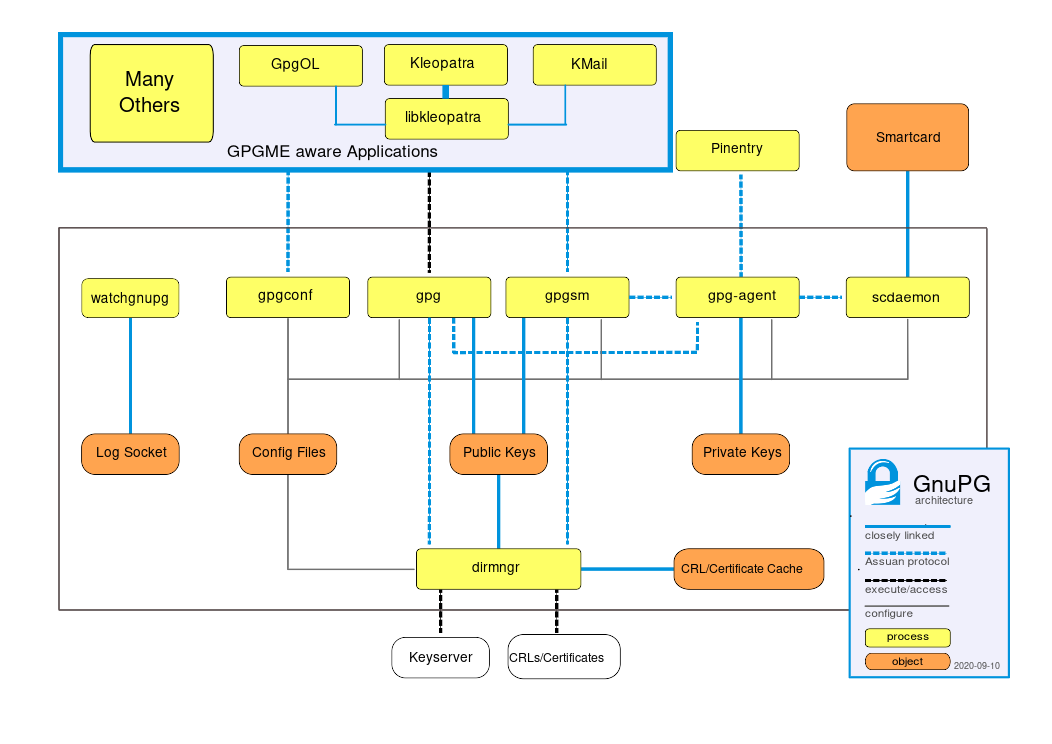
Component Interaction Using The Gnu Privacy Guard A simple cheat sheet for gnupg commands to help you generate, export, and manage keys with ease. perfect for occasional users. stay secure!. First, we need to create a pgp key pair using gnupg. we'll use the full key generation command for more control over options. 1. key type selection: 2. key size: 3. expiration: 4. user id information: 5. passphrase: choose a secure passphrase when prompted (you'll need this later!). This article details how gpg operates, why it is vital for securing communications, and provides practical command line examples. it also covers common parameters, advanced usage, troubleshooting, security considerations, and related tools. Useful for updating a key with the latest signatures, user ids, etc. calling this with no arguments will refresh the entire keyring. This guide explains how to encrypt and decrypt files using gnupg from commandline in linux and unix like operating systems. Today, we are going to see how to encrypt and decrypt files from command line in linux using a free utility named gnu privacy guard (shortly gpg or gnupg). there are, of course, plethora of methods, and applications are available to encrypt and decrypt files in linux.
Comments are closed.