Github Yossigor Acoustickeylogger A Side Channel Attack On The

Tag Side Channel Attack Ars Technica The purpose of this project is to explore the viability and effectiveness of a new type of keylogger. instead of using a malware installed on the target computer itself to record keystrokes, an acoustic keylogger can be deployed on a separate dedicated device and monitor keystrokes on another keyboard based on the acoustic sound fingerprinting. Abstract—acoustic side channel attacks (ascas) on key boards pose a significant security threat, yet existing research often overestimates their viability by focusing on sterile, noise free environments. this paper presents a comprehensive study on the robustness and generalization of modern hybrid neural archi tectures (coatnet, moat, swin transformer) for this task. un der controlled.
Acoustic Side Channel Attack The potential vulnerability to acoustic side channel attacks also increases. this survey paper thoroughly reviews existing research, explaining why such attacks are feasible, the applicable threat models, and the methodologies employed to launch and enhance these attacks. However, these systems are susceptible to acoustic side channel attacks. researchers have successfully developed methods that can extract typed keystrokes from ambient noise. The acoustic emanations from keyboards provide a side channel attack from which an attacker can recover sensitive user information, such as passwords and personally identifiable information. Acoustic side channel attacks (ascas) exploit sound em anations from electronic devices, particularly keyboards, to infer sensitive information like passwords and pins.
Mitigating A Token Length Side Channel Attack In Our Ai Products The acoustic emanations from keyboards provide a side channel attack from which an attacker can recover sensitive user information, such as passwords and personally identifiable information. Acoustic side channel attacks (ascas) exploit sound em anations from electronic devices, particularly keyboards, to infer sensitive information like passwords and pins. As the prevalence of keyboard based input systems continues to expand across various computing platforms, and with the improvement of microphone technology, the potential vulnerability to acoustic side channel attacks also increases. The most recent systematic literature review on acoustic side channel attacks is titled “a survey on acoustic side channel attacks on keyboards”, authored by alireza taheritajar, zahra mahmoudpour harris, and reza rahaeimehr. Acoustic side channel attacks (ascas) exploit the sound produced by keyboards and other devices to infer sensitive information without breaching software or network defenses. This survey paper thoroughly reviews existing research, explaining why acoustic side channel attacks are feasible, the applicable threat models, and the methodologies employed to launch and enhance these attacks.
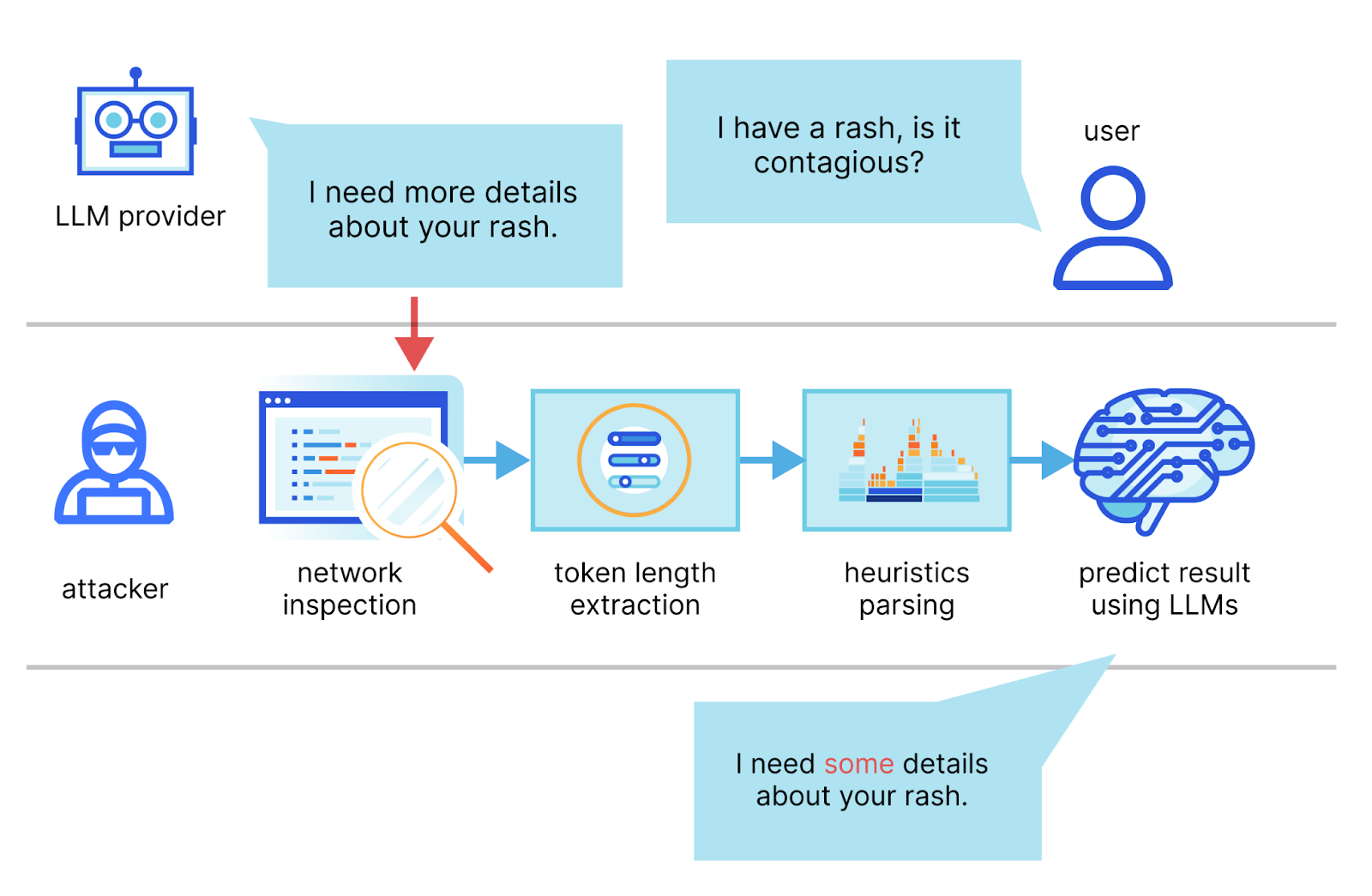
Mitigating A Token Length Side Channel Attack In Our Ai Products As the prevalence of keyboard based input systems continues to expand across various computing platforms, and with the improvement of microphone technology, the potential vulnerability to acoustic side channel attacks also increases. The most recent systematic literature review on acoustic side channel attacks is titled “a survey on acoustic side channel attacks on keyboards”, authored by alireza taheritajar, zahra mahmoudpour harris, and reza rahaeimehr. Acoustic side channel attacks (ascas) exploit the sound produced by keyboards and other devices to infer sensitive information without breaching software or network defenses. This survey paper thoroughly reviews existing research, explaining why acoustic side channel attacks are feasible, the applicable threat models, and the methodologies employed to launch and enhance these attacks.
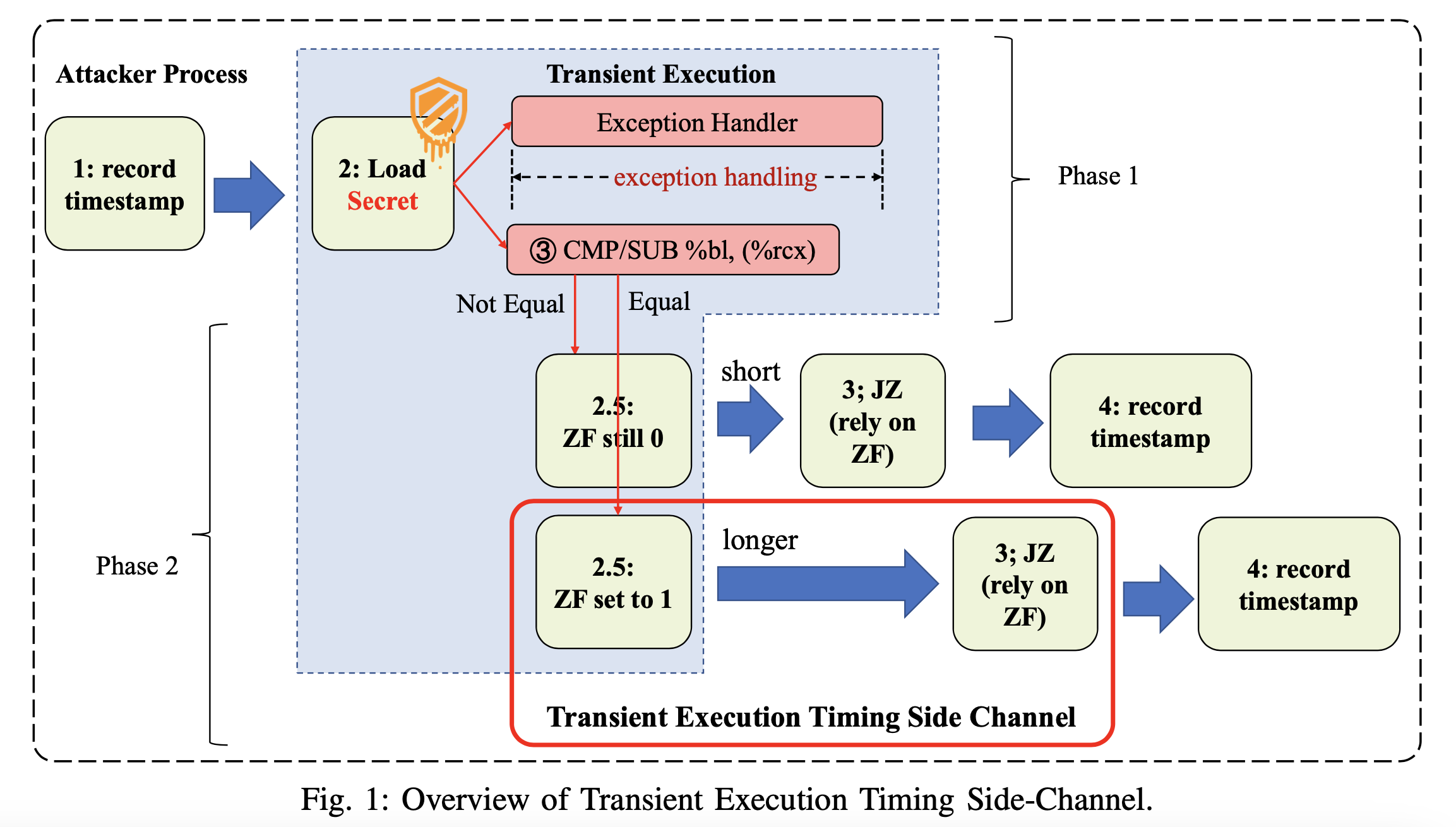
Researchers Discover New Side Channel Attack That Works Against Intel Acoustic side channel attacks (ascas) exploit the sound produced by keyboards and other devices to infer sensitive information without breaching software or network defenses. This survey paper thoroughly reviews existing research, explaining why acoustic side channel attacks are feasible, the applicable threat models, and the methodologies employed to launch and enhance these attacks.

прослушка нажатий на кнопки клавиатуры блог касперского
Comments are closed.