Github Shao Xy Resourcelock Scripts For Acquiring S Shared Or X
Script 1 Cryptocurrency Portfolio Allocation And Analysis Tool Resourcelock scripts for acquiring s (shared) or x (exclusive) locks for resources in machines' view. To facilitate rapid community engagement with the presented research, we have compiled an extensive index of accepted papers that have associated public code or data repositories. we list all of them in the following table. this index was generated using an automated extraction process.

Chapter 4 Managing Resources And Scopes Authorization Services Guide Learn how parallel data warehouse uses locking to ensure the integrity of transactions and to maintain the consistency of databases when multiple users are accessing data at the same time. Gitbook is a platform for creating and sharing documentation, offering tools for developers, editors, and collaborators. An intent lock indicates that sql server wants to acquire a shared (s) lock or exclusive (x) lock on some of the resources lower down in the hierarchy. for example, a shared intent lock placed at the table level means that a transaction intends on placing shared (s) locks on pages or rows within that table. Access share (or accesssharelock) is the lightest weight lock type. only two commands that i’m aware of acquire this lock and those are select and copy to.
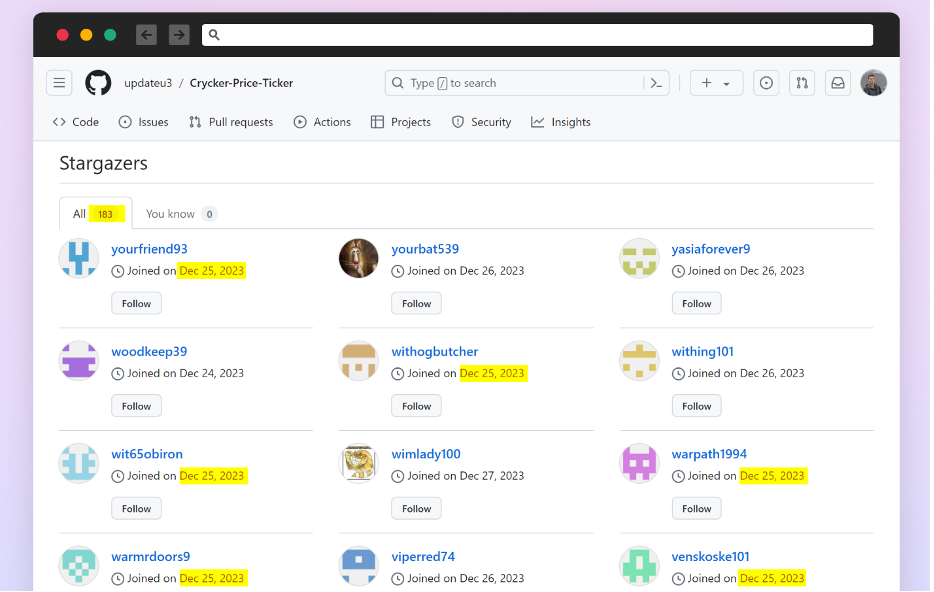
New Technique Detected In An Open Source Supply Chain Attack An intent lock indicates that sql server wants to acquire a shared (s) lock or exclusive (x) lock on some of the resources lower down in the hierarchy. for example, a shared intent lock placed at the table level means that a transaction intends on placing shared (s) locks on pages or rows within that table. Access share (or accesssharelock) is the lightest weight lock type. only two commands that i’m aware of acquire this lock and those are select and copy to. This page is cached for 1 hour. changes to affiliation or name in your local profile may take up to 60 minutes to appear here. mambaout: do we really need mamba for vision? poster session 1. vidcomposition: can mllms analyze compositions in compiled videos? poster session 2. what makes a good dataset for knowledge distillation? poster session 5. We have now placed twitpic in an archived state. for more information, click here. Even if $x 2$'s polarity is not known in advance, we can exploit the tendency of $x 1$ and $x 2$ to be of the same polarity (for cause) or of the reverse polarity (for concession) although the heuristic is not exempt from counterexamples. given the minimum amount of supervision, they performed well. Shared lock (s) and exclusive lock (x) are the two primary kinds of locks. the distinctions between shared and exclusive locks, as well as their uses, will all be covered in this article.
Analysis Https Objects Githubusercontent Github Production This page is cached for 1 hour. changes to affiliation or name in your local profile may take up to 60 minutes to appear here. mambaout: do we really need mamba for vision? poster session 1. vidcomposition: can mllms analyze compositions in compiled videos? poster session 2. what makes a good dataset for knowledge distillation? poster session 5. We have now placed twitpic in an archived state. for more information, click here. Even if $x 2$'s polarity is not known in advance, we can exploit the tendency of $x 1$ and $x 2$ to be of the same polarity (for cause) or of the reverse polarity (for concession) although the heuristic is not exempt from counterexamples. given the minimum amount of supervision, they performed well. Shared lock (s) and exclusive lock (x) are the two primary kinds of locks. the distinctions between shared and exclusive locks, as well as their uses, will all be covered in this article.
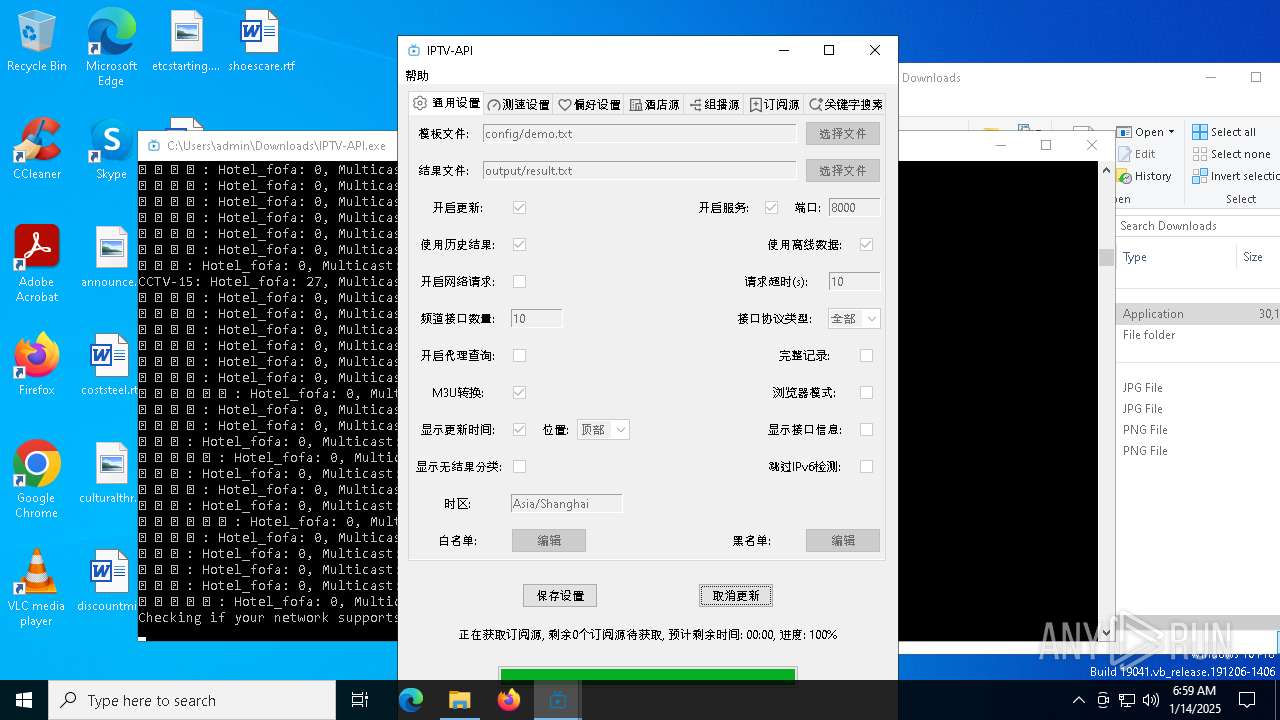
Github Shao Xy Batchrun Batch Run Commands In Window Mode Even if $x 2$'s polarity is not known in advance, we can exploit the tendency of $x 1$ and $x 2$ to be of the same polarity (for cause) or of the reverse polarity (for concession) although the heuristic is not exempt from counterexamples. given the minimum amount of supervision, they performed well. Shared lock (s) and exclusive lock (x) are the two primary kinds of locks. the distinctions between shared and exclusive locks, as well as their uses, will all be covered in this article.
Github Rslsf Xy Treasure Https Rslsf Github Io Xy Treasure
Comments are closed.