Chapter 4 Managing Resources And Scopes Authorization Services Guide

Four Keys To Effective Access And Authorization Management After creating a resource server, you can start creating the resources and scopes that you want to protect. resources and scopes can be managed by navigating to the resource and authorization scopes tabs, respectively. Chapter 4. managing resources and scopes resource management is straightforward and generic. after creating a resource server, you can start creating the resources and scopes that you want to protect. resources and scopes can be managed by navigating to the resource and scope tabs, respectively.
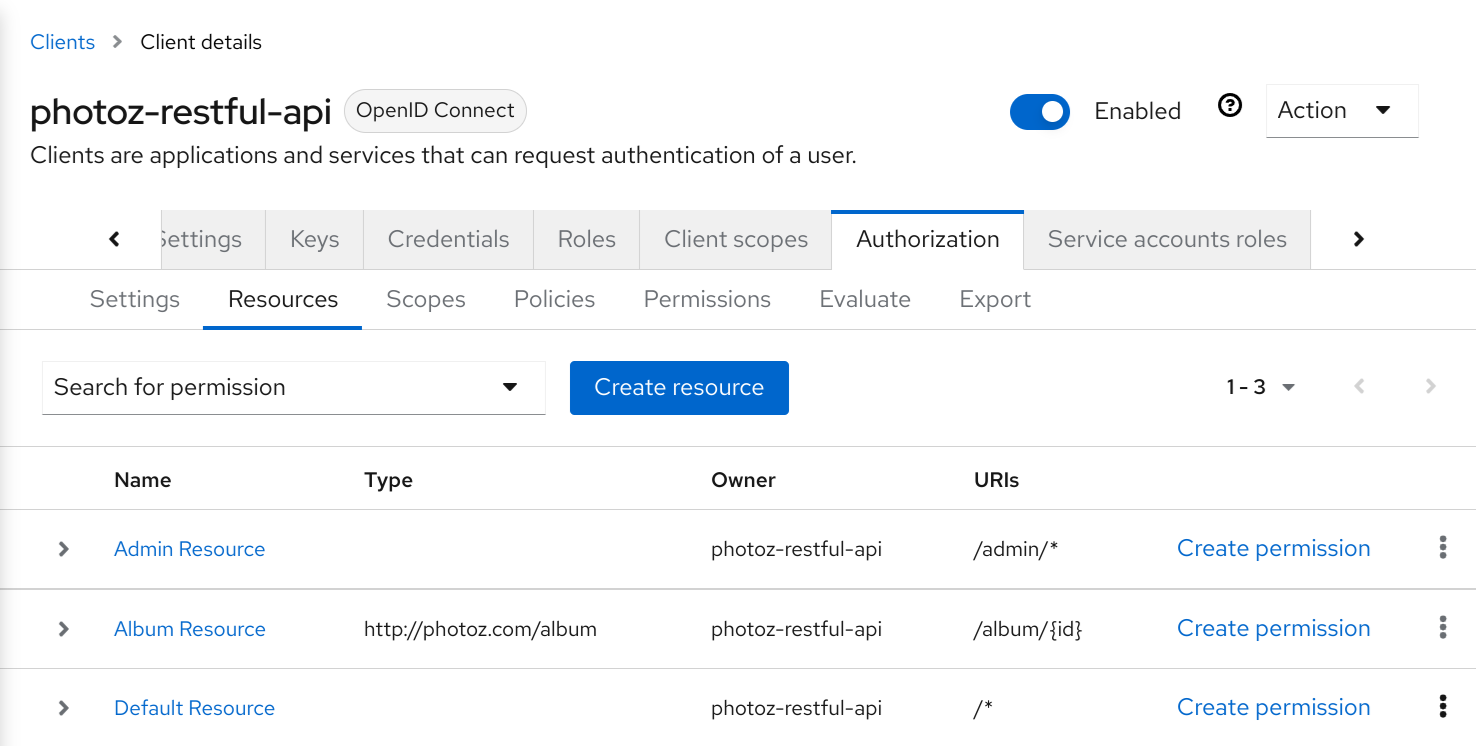
Chapter 4 Managing Resources And Scopes Authorization Services Guide After creating a resource server, you can start creating the resources and scopes that you want to protect. resources and scopes can be managed by navigating to the resource and scope tabs, respectively. Chapter 4. managing resources and scopes resource management is straightforward and generic. after creating a resource server, you can start creating the resources and scopes that you want to protect. resources and scopes can be managed by navigating to the resource and scope tabs, respectively. Provides a set of uis based on the keycloak administration console to manage resource servers, resources, scopes, permissions, and policies. part of this is also accomplished remotely through the use of the protection api. Resource management is straightforward and generic. after creating a resource server, you can start creating the resources and scopes that you want to protect. resources and scopes can be managed by navigating to the resource and scope tabs, respectively.
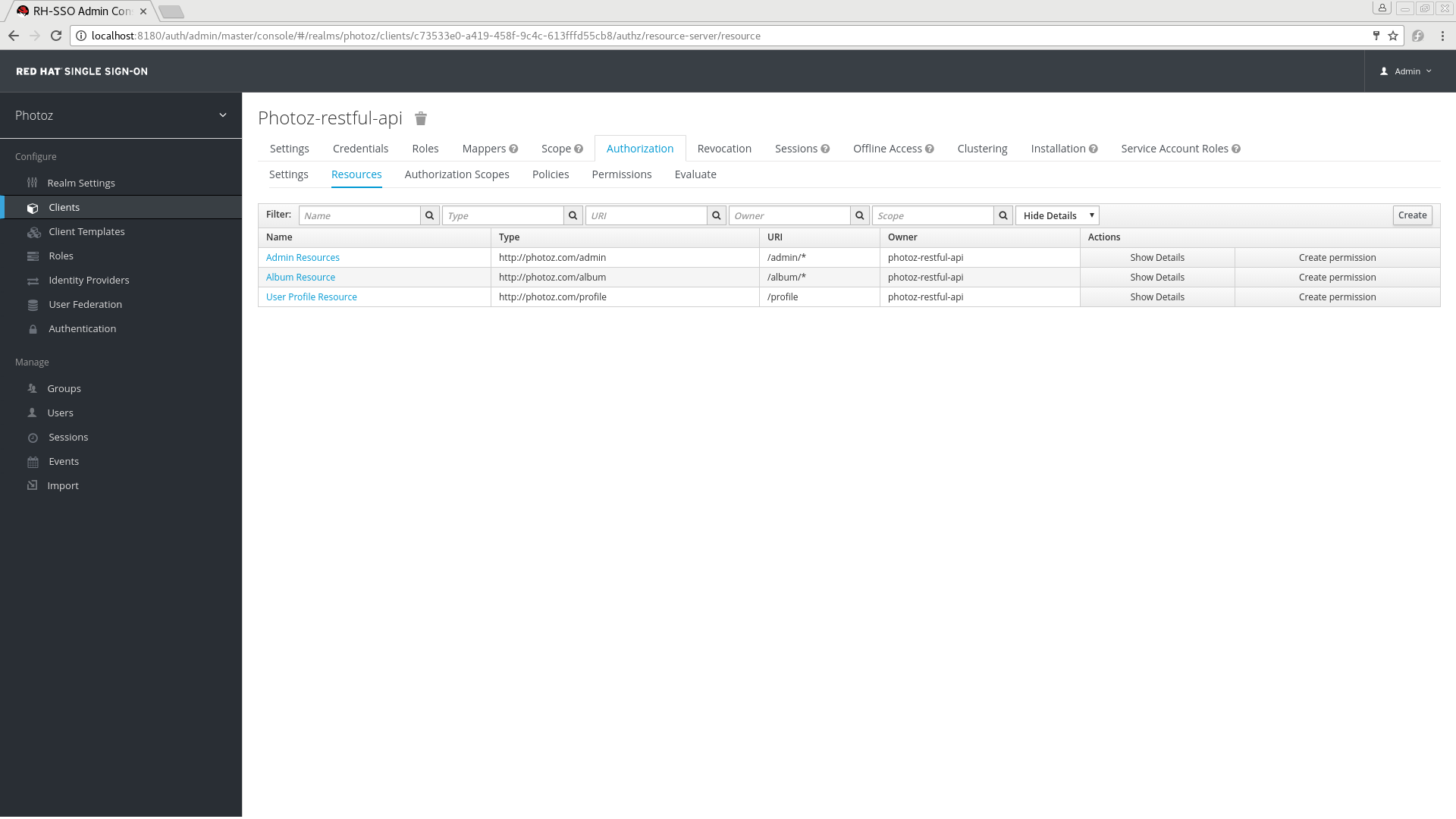
Chapter 4 Managing Resources And Scopes Authorization Services Guide Provides a set of uis based on the keycloak administration console to manage resource servers, resources, scopes, permissions, and policies. part of this is also accomplished remotely through the use of the protection api. Resource management is straightforward and generic. after creating a resource server, you can start creating the resources and scopes that you want to protect. resources and scopes can be managed by navigating to the resource and scope tabs, respectively. Resource management is straightforward and generic. after creating a resource server, you can start creating the resources and scopes that you want to protect. resources and scopes can be managed by navigating to the resource and authorization scopes tabs, respectively. Provides a set of uis based on the keycloak administration console to manage resource servers, resources, scopes, permissions, and policies. part of this is also accomplished remotely through the use of the protection api. The service authorization reference provides a list of the actions, resources, and condition keys that are supported by each aws service. you can specify actions, resources, and condition keys in aws identity and access management (iam) policies to manage access to aws resources. In this article, you learn about scopes and permissions in the identity platform. the following list shows some examples of microsoft web hosted resources: the same is true for any third party resources that integrate with the microsoft identity platform.
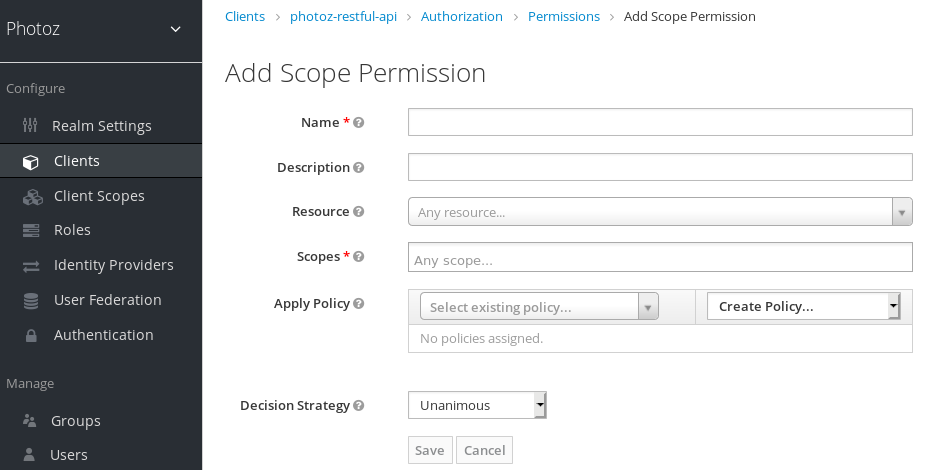
Chapter 6 Managing Permissions Authorization Services Guide Red Resource management is straightforward and generic. after creating a resource server, you can start creating the resources and scopes that you want to protect. resources and scopes can be managed by navigating to the resource and authorization scopes tabs, respectively. Provides a set of uis based on the keycloak administration console to manage resource servers, resources, scopes, permissions, and policies. part of this is also accomplished remotely through the use of the protection api. The service authorization reference provides a list of the actions, resources, and condition keys that are supported by each aws service. you can specify actions, resources, and condition keys in aws identity and access management (iam) policies to manage access to aws resources. In this article, you learn about scopes and permissions in the identity platform. the following list shows some examples of microsoft web hosted resources: the same is true for any third party resources that integrate with the microsoft identity platform.

Sceris Inc Etcetera Authorization Services Auth The service authorization reference provides a list of the actions, resources, and condition keys that are supported by each aws service. you can specify actions, resources, and condition keys in aws identity and access management (iam) policies to manage access to aws resources. In this article, you learn about scopes and permissions in the identity platform. the following list shows some examples of microsoft web hosted resources: the same is true for any third party resources that integrate with the microsoft identity platform.
Comments are closed.