Github Python Nerd Git Sudo Security Bypass
Introduction To Git And Github For Python Real Python Contribute to python nerd git sudo security bypass development by creating an account on github. Cve 2019–14287 is a vulnerability discovered by apple researcher joe vennix in the unix based sudo program. this vulnerability allows sudo to be configured with specific user permissions, but.
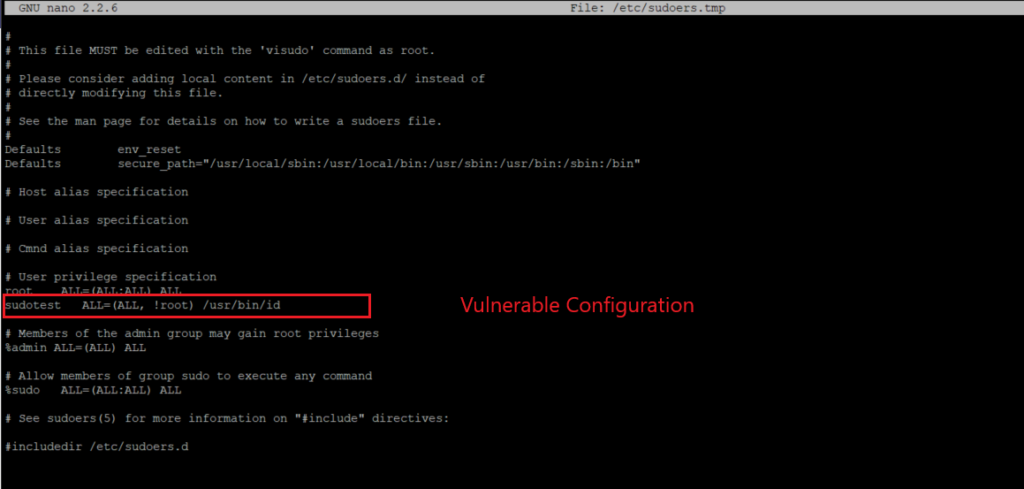
Sudo Security Policy Bypass Vulnerability Qualys Threatprotect Sudo security bypass tryhackme walkthrough (privilege escalation) in this video, i walk you through the "sudo security bypass" room on tryhackme. In cases where you have sudo access but not the password, you can escalate privileges by waiting for a sudo command execution and then hijacking the session token. For some reason i need, as user, to run without sudo a script script.sh which needs root privileges to work. i saw as the only solution to put sudo inside script.sh. let's take an example : #! bin sh . of course, if i execute this script, i get a prompt asking me for a password. Does it provide an additional layer of security, or is it easy for a skilled attacker to bypass the security policies it’s enforcing? by answering these questions and exploring the bypass we found, we hope to provide stronger security measures to protect ci cd workflows running on github actions.
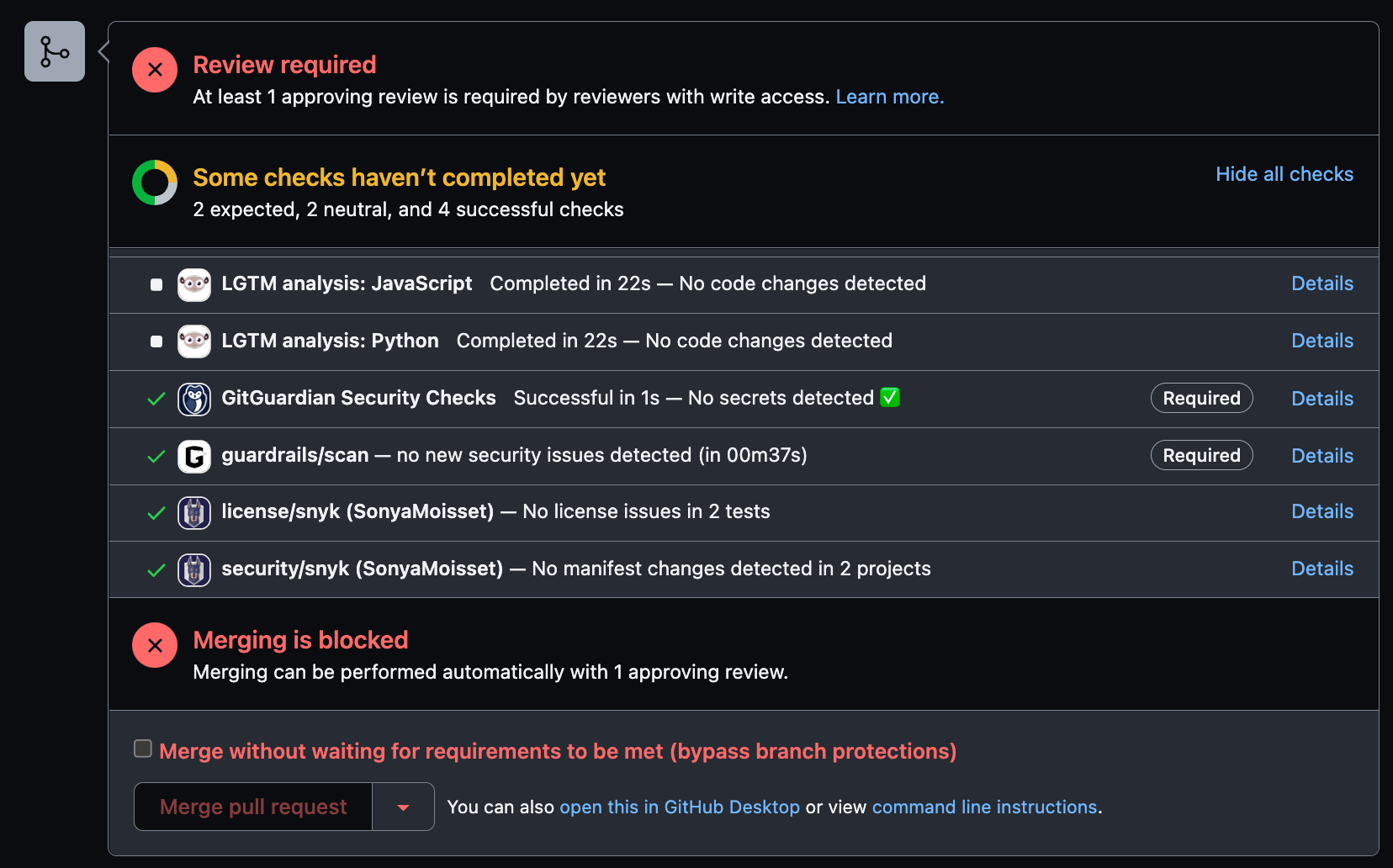
Github Security 101 Best Practices For Securing Your Repository For some reason i need, as user, to run without sudo a script script.sh which needs root privileges to work. i saw as the only solution to put sudo inside script.sh. let's take an example : #! bin sh . of course, if i execute this script, i get a prompt asking me for a password. Does it provide an additional layer of security, or is it easy for a skilled attacker to bypass the security policies it’s enforcing? by answering these questions and exploring the bypass we found, we hope to provide stronger security measures to protect ci cd workflows running on github actions. This blog will guide you through setting up ssh keys for the target user, using su to switch to the target user, and leveraging sudo to run git commands directly —all while adhering to security best practices. Get root using sudo (as a user with uid 1) with the command you found in the last question, then use cat root root.txt to get the flag. このマシンには cve 2019 14287 の脆弱性があります。. Joe vennix discovered that sudo, a program designed to provide limited super user privileges to specific users, when configured to allow a user to run commands as an arbitrary user via the all keyword in a runas specification, allows to run commands as root by specifying the user id 1 or 4294967295 this could allow a user with sufficient sudo. This vulnerability leads to a security bypass in the sudoedit feature, allowing unauthorized users to escalate their privileges by editing files. this vulnerability affects versions of sudo from 1.8.0 through 1.9.12p1.
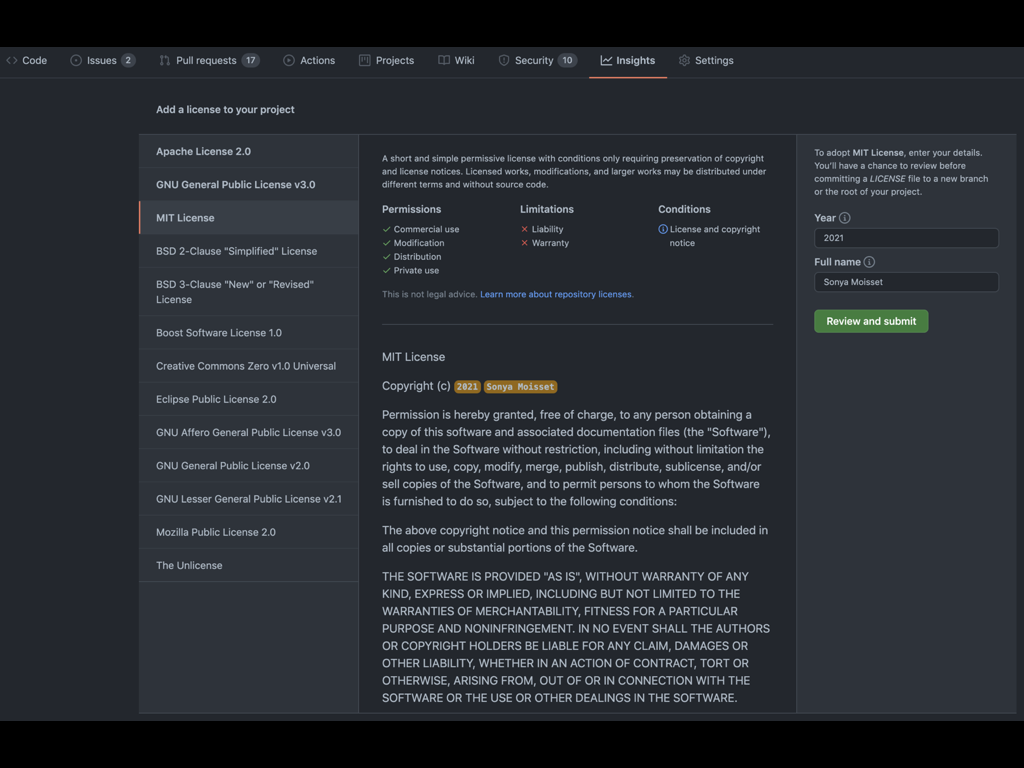
Github Security 101 Best Practices For Securing Your Repository This blog will guide you through setting up ssh keys for the target user, using su to switch to the target user, and leveraging sudo to run git commands directly —all while adhering to security best practices. Get root using sudo (as a user with uid 1) with the command you found in the last question, then use cat root root.txt to get the flag. このマシンには cve 2019 14287 の脆弱性があります。. Joe vennix discovered that sudo, a program designed to provide limited super user privileges to specific users, when configured to allow a user to run commands as an arbitrary user via the all keyword in a runas specification, allows to run commands as root by specifying the user id 1 or 4294967295 this could allow a user with sufficient sudo. This vulnerability leads to a security bypass in the sudoedit feature, allowing unauthorized users to escalate their privileges by editing files. this vulnerability affects versions of sudo from 1.8.0 through 1.9.12p1.
Comments are closed.