Github Interstellarspace Rsa Common Mod Protocol Failure Decryption
Ssl Decryption Profile Ssl Protocol Settings Rsa decryption on a protocol failure (same modulo and plaintext) interstellarspace rsa common mod protocol failure decryption. Any language github actions supports node.js, python, java, ruby, php, go, rust, , and more. build, test, and deploy applications in your language of choice.
Spaces Overview Rsa decryption on a protocol failure (same modulo and plaintext) releases · interstellarspace rsa common mod protocol failure decryption. Bleichenbacher’s attack is reported in the publication “chosen ciphertext attacks against protocols based on the rsa encryption standard pkcs#1,” that is available from his home page. A common modulus attack on rsa is a type of cryptographic attack that takes advantage of the properties of rsa encryption when the same modulus is used for multiple encryptions. Many of the cryptographic failures of rsa that we will see today come from misuses of the rsa function; such as assuming that it is hard to invert on non random inputs.
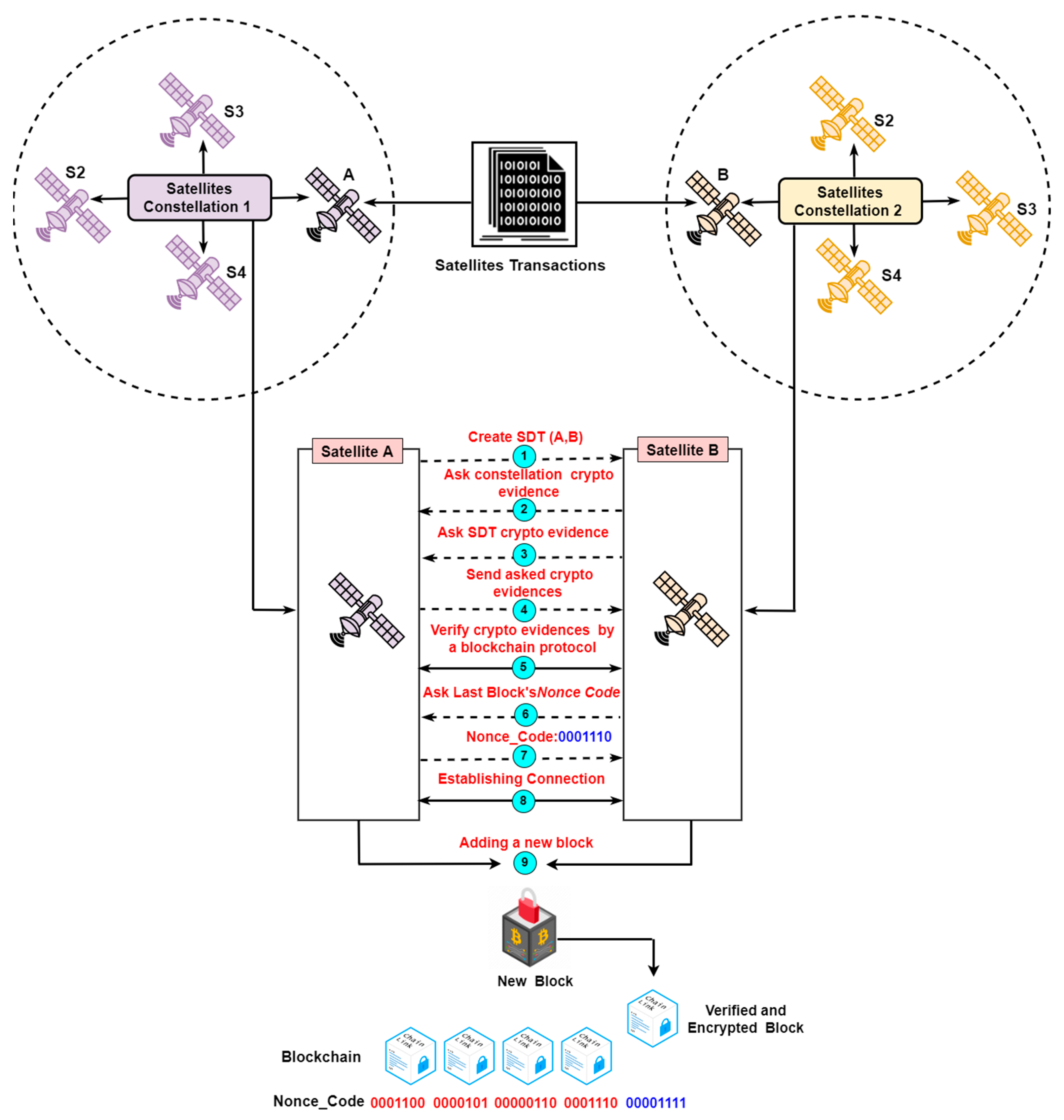
A Blockchain Protocol For Authenticating Space Communications Between A common modulus attack on rsa is a type of cryptographic attack that takes advantage of the properties of rsa encryption when the same modulus is used for multiple encryptions. Many of the cryptographic failures of rsa that we will see today come from misuses of the rsa function; such as assuming that it is hard to invert on non random inputs. Limited use in some applications: rsa algorithm is not suitable for some applications, such as those that require constant encryption and decryption of large amounts of data, due to its slow processing speed. Identify decryption failures and why they happened and drill down into the exact failure reasons so you can address issues. Even worse, nobody has ever proved that factoring n is the fastest way to break rsa. in other words, there may exist a clever algorithm (for either factoring n or breaking rsa in a di erent manner) that remains undiscovered yet. once found, rsa algorithm will become insecure, and therefore, obsolete. The certification authority browser forum (ca browser forum) is a voluntary gathering of certificate issuers and suppliers of internet browser software and other applications that use certificates (certificate consumers). more information for about the forum and information for site owners, developers, auditors and assessors, and potential members can be found in the about section of this.

A Blockchain Protocol For Authenticating Space Communications Between Limited use in some applications: rsa algorithm is not suitable for some applications, such as those that require constant encryption and decryption of large amounts of data, due to its slow processing speed. Identify decryption failures and why they happened and drill down into the exact failure reasons so you can address issues. Even worse, nobody has ever proved that factoring n is the fastest way to break rsa. in other words, there may exist a clever algorithm (for either factoring n or breaking rsa in a di erent manner) that remains undiscovered yet. once found, rsa algorithm will become insecure, and therefore, obsolete. The certification authority browser forum (ca browser forum) is a voluntary gathering of certificate issuers and suppliers of internet browser software and other applications that use certificates (certificate consumers). more information for about the forum and information for site owners, developers, auditors and assessors, and potential members can be found in the about section of this.

A Blockchain Protocol For Authenticating Space Communications Between Even worse, nobody has ever proved that factoring n is the fastest way to break rsa. in other words, there may exist a clever algorithm (for either factoring n or breaking rsa in a di erent manner) that remains undiscovered yet. once found, rsa algorithm will become insecure, and therefore, obsolete. The certification authority browser forum (ca browser forum) is a voluntary gathering of certificate issuers and suppliers of internet browser software and other applications that use certificates (certificate consumers). more information for about the forum and information for site owners, developers, auditors and assessors, and potential members can be found in the about section of this.
Comments are closed.