Github Ibm Blackbox Adversarial Reprogramming Code For Reproducing
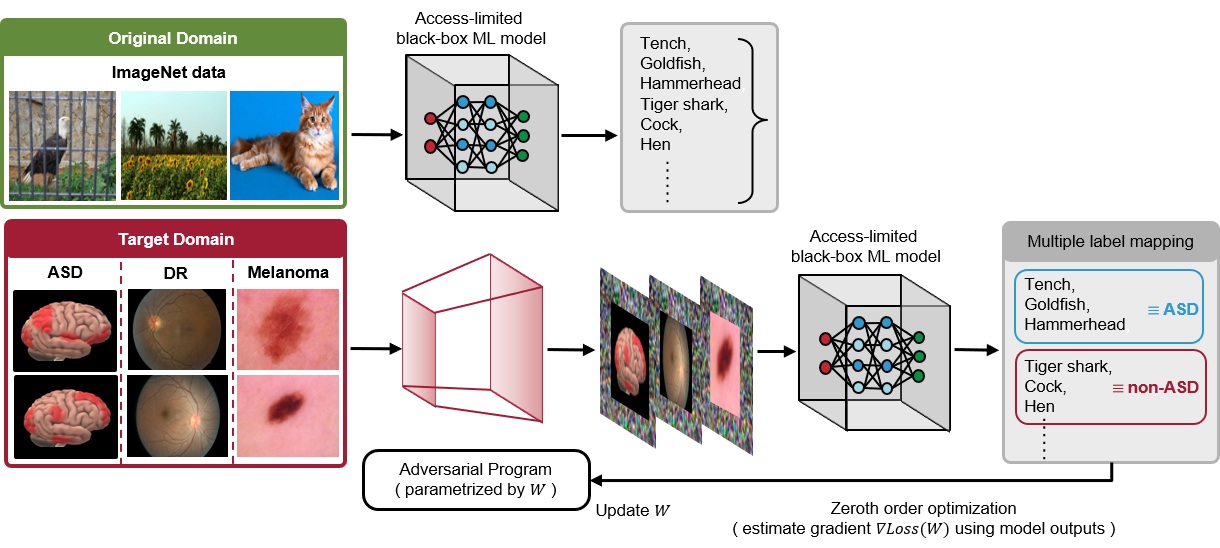
Github Ibm Blackbox Adversarial Reprogramming Code For Reproducing Our code is implemented in python 3.6 and tensorflow 1.14. the following figure illustrates the framework for our proposed black box adversarial reprogramming method (bar):. You can create a release to package software, along with release notes and links to binary files, for other people to use. learn more about releases in our docs.
Github Rajatvd Adversarialreprogramming Code For My Blog Post On Code for reproducing the icml 2020 paper "transfer learning without knowing: reprogramming black box machine learning models with scarce data and limited resources" arxiv.org abs 2007.08714 activity · ibm blackbox adversarial reprogramming. Code for reproducing the icml 2020 paper "transfer learning without knowing: reprogramming black box machine learning models with scarce data and limited resources" arxiv.org abs 2007.08714 blackbox adversarial reprogramming adv reprogramming.py at main · ibm blackbox adversarial reprogramming. Code for reproducing the icml 2020 paper "transfer learning without knowing: reprogramming black box machine learning models with scarce data and limited resources" arxiv.org abs 2007.08714 pull requests · ibm blackbox adversarial reprogramming. The adversarial robustness toolbox (art) is an open source project, started by ibm, for machine learning security and has recently been donated to the linux foundation for ai (lfai) by ibm as part of the trustworthy ai tools.
Github Ibm Blackbox Adversarial Reprogramming Code For Reproducing Code for reproducing the icml 2020 paper "transfer learning without knowing: reprogramming black box machine learning models with scarce data and limited resources" arxiv.org abs 2007.08714 pull requests · ibm blackbox adversarial reprogramming. The adversarial robustness toolbox (art) is an open source project, started by ibm, for machine learning security and has recently been donated to the linux foundation for ai (lfai) by ibm as part of the trustworthy ai tools. Code for reproducing the icml 2020 paper "transfer learning without knowing: reprogramming black box machine learning models with scarce data and limited resources" arxiv.org abs 2007.08714 file finder · ibm blackbox adversarial reprogramming. Code for reproducing the icml 2020 paper "transfer learning without knowing: reprogramming black box machine learning models with scarce data and limited resources" arxiv.org abs 2007.08714 blackbox adversarial reprogramming utils.py at main · ibm blackbox adversarial reprogramming. Code for reproducing the icml 2020 paper "transfer learning without knowing: reprogramming black box machine learning models with scarce data and limited resources" arxiv.org abs 2007.08714 workflow runs · ibm blackbox adversarial reprogramming. Art provides tools that enable developers and researchers to evaluate, defend, certify and verify machine learning models and applications against the adversarial threats of evasion, poisoning, extraction, and inference.
Github Yunyuntsai Black Box Adversarial Reprogramming Code For Code for reproducing the icml 2020 paper "transfer learning without knowing: reprogramming black box machine learning models with scarce data and limited resources" arxiv.org abs 2007.08714 file finder · ibm blackbox adversarial reprogramming. Code for reproducing the icml 2020 paper "transfer learning without knowing: reprogramming black box machine learning models with scarce data and limited resources" arxiv.org abs 2007.08714 blackbox adversarial reprogramming utils.py at main · ibm blackbox adversarial reprogramming. Code for reproducing the icml 2020 paper "transfer learning without knowing: reprogramming black box machine learning models with scarce data and limited resources" arxiv.org abs 2007.08714 workflow runs · ibm blackbox adversarial reprogramming. Art provides tools that enable developers and researchers to evaluate, defend, certify and verify machine learning models and applications against the adversarial threats of evasion, poisoning, extraction, and inference.
Comments are closed.