Github Bad Microservices Py Auth Micro
How To Build And Deploy Microservices With Python Kinsta Py auth micro is a small identity provider library which can use an ldap ad as upstream identity provider and can also store users localy. the authentication and authorization is done via id tokens and access tokens. Py auth micro is a small identity provider library which can use an ldap ad as upstream identity provider and can also store users localy. the authentication and authorization is done via id tokens and access tokens. the id tokens are given out after a user successfully logged in.

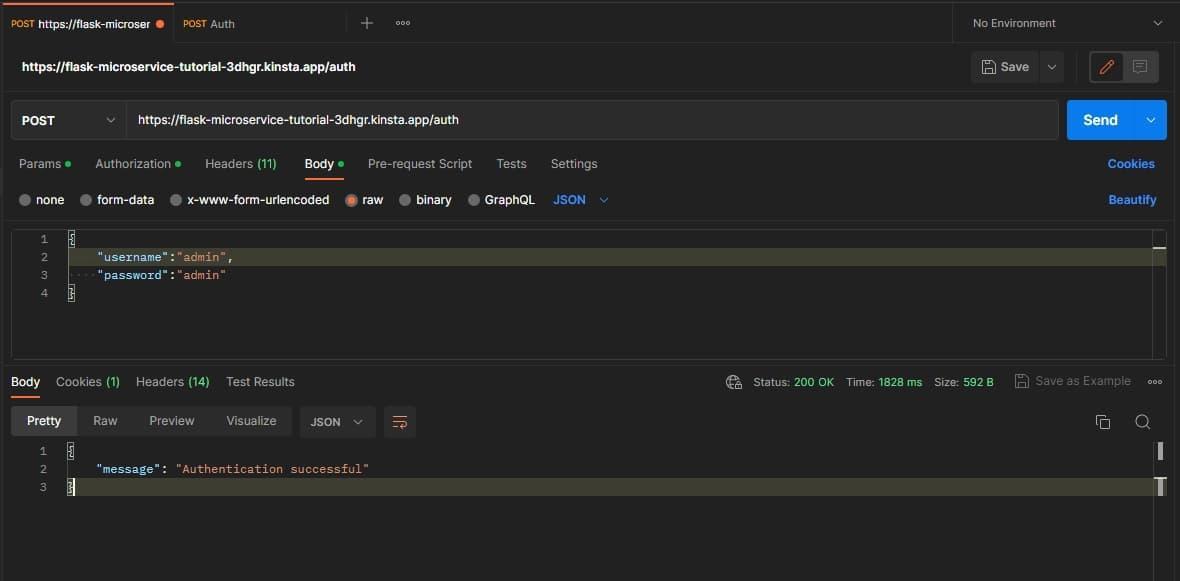
Github Bad Credentials No Description Threads Appwrite Bad microservices has 6 repositories available. follow their code on github. A small library for managing users and group based permissions releases · bad microservices py auth micro. Py auth amqp wrapper public a wrapper for using py auth micro via rpc over amqp python • mit license. Example implementation # here is an example auth flow you could implement with this library.
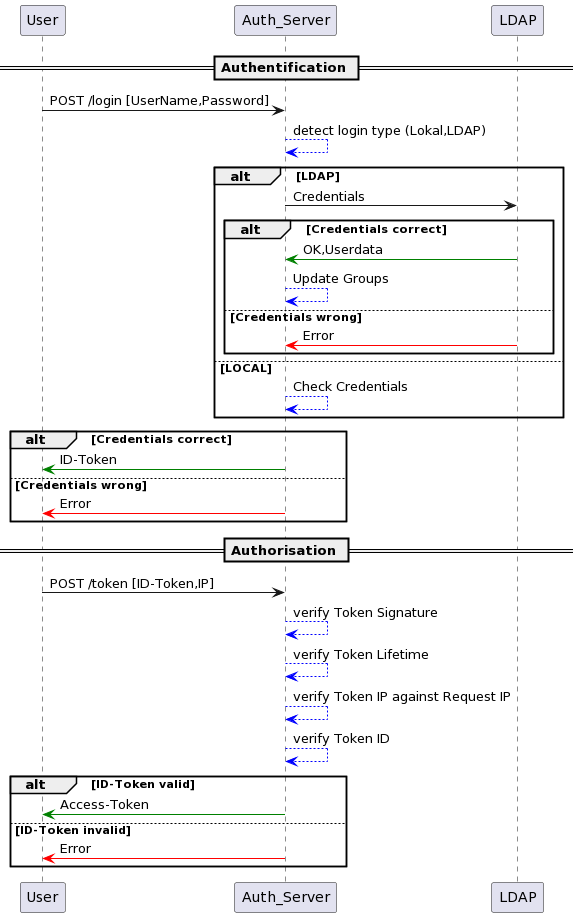
Getting Started Py Auth Micro Documentation Py auth amqp wrapper public a wrapper for using py auth micro via rpc over amqp python • mit license. Example implementation # here is an example auth flow you could implement with this library. Exceptions submodule # this submodule contains custom exceptions for the py auth micro framework. Examples # show source. Raises: permissionerror: not authorized to change userinformation valueerror: changed value is invalid returns: dict: :code:` {"success":true}` if operation was successfull """req user,is admin= get info from token(self.jwt validator,self.app cfg,access token)# check if we are allowed to even change the userifreq user!=usernameornotis admin:raisepermissionerror("missing permission")user:user=awaituser.get(username=username)# check if its an local user or an ad useris ad user=(user.auth type==authsource.ldaporuser.auth type==authsource.kerberos)ifis ad userand(passwordisnotnoneoremailisnotnone):raisevalueerror("can't change attribute for ad user")ifnotis adminandactivatedisnotnone:raisepermissionerror("unauthorized")ifemailisnotnone:# check emailifre.fullmatch(self.app cfg.email regex,email)isnone:raisevalueerror("bad email")user.email=emailifactivatedisnotnone:user.activated=activatedifpasswordisnotnone:# create password hashifre.fullmatch(self.app cfg.password regex,password)isnone:raisevalueerror("bad password")pw salt=bcrypt.gensalt()pw hash=bcrypt.hashpw(password.encode("utf 8"),pw salt)user.password hash=pw hashawaituser.revoke id token()awaituser.save()return{"resp code":200,"resp data":{"msg":f"changed data for user {username}"},}. Name: py auth micro description: a wrapper around pyjwt license spdx: mit version: 0.1.0 spec version: 1.0 home url: github bad microservices py auth micro news url: libraries.io pypi py auth micro versions.atom date: 2023 05 08 about resource: none libraries io url: libraries.io pypi py auth micro?number=0.1.0 vcs.
Comments are closed.