Github 1blackline Bug Bounty Dork
Bug Bounty Program Contact github support about this user’s behavior. learn more about reporting abuse. 1blackline has 26 repositories available. follow their code on github. External tools github shodan crt.sh censys reddit stackoverflow bug bounty programs bug bounty security.txt responsible disclosure vrp hackerone bugcrowd.

Hackerone On Twitter We See The Bug Bounty Program As A Permanent Uncover vulnerabilities, enhance web security, and improve your ethical hacking skills with our curated list of dorks for various exposures and misconfigurations. The google dork, github dork, and shodan dork tools are intended to assist ethical security researchers, bug bounty hunters, and penetration testers in identifying potential vulnerabilities and sensitive information in web applications and internet connected devices. Contribute to 1blackline bug bounty dork development by creating an account on github. Github is where people build software. more than 150 million people use github to discover, fork, and contribute to over 420 million projects.
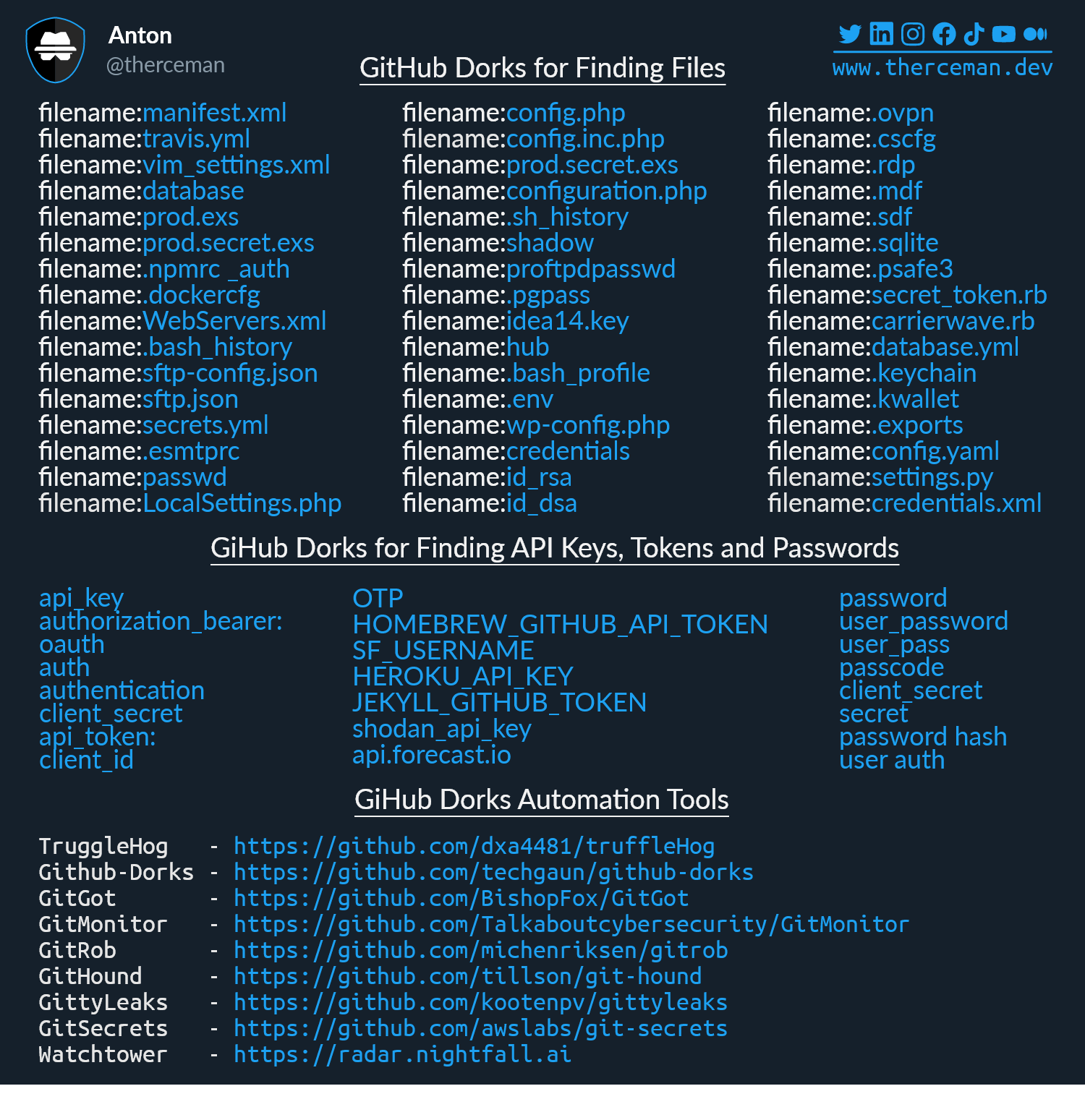
Anton On Twitter Bug Bounty Info Github Recon Using Github Dorks рџ Contribute to 1blackline bug bounty dork development by creating an account on github. Github is where people build software. more than 150 million people use github to discover, fork, and contribute to over 420 million projects. By leveraging these techniques, ethical hackers can identify vulnerabilities in public and private bug bounty programs. this article explores powerful github dorking methods, verified commands, and actionable steps to enhance your cybersecurity research. List of google dorks to search for companies that have a responsible disclosure program or bug bounty program which are not affiliated with known bug bounty platforms such as hackerone or bugcrowd. Target domain tip: add ?d=example to url to auto load execute scan all modules google dorks recon & subdomains archives & history osint & intelligence specific files. Github repo enter a domain: for multiple domains, separate by comma. e.g., example1 , example2.
Github 1blackline Bug Bounty Dork By leveraging these techniques, ethical hackers can identify vulnerabilities in public and private bug bounty programs. this article explores powerful github dorking methods, verified commands, and actionable steps to enhance your cybersecurity research. List of google dorks to search for companies that have a responsible disclosure program or bug bounty program which are not affiliated with known bug bounty platforms such as hackerone or bugcrowd. Target domain tip: add ?d=example to url to auto load execute scan all modules google dorks recon & subdomains archives & history osint & intelligence specific files. Github repo enter a domain: for multiple domains, separate by comma. e.g., example1 , example2.
Github Hktalent Bug Bounty Bounty Collection Target domain tip: add ?d=example to url to auto load execute scan all modules google dorks recon & subdomains archives & history osint & intelligence specific files. Github repo enter a domain: for multiple domains, separate by comma. e.g., example1 , example2.
Github Pwdec Bug Bounty Helper
Comments are closed.