Getting Started With Attack Surface Management
A Practical Guide To Attack Surface Management Elasticito The attack surface includes digital, physical, and social engineering elements. managing the attack surface means accounting for not just cloud assets and infrastructure misconfigurations, but also endpoints like laptops and iot devices, plus human vulnerabilities such as phishing susceptibility. Your first day in attack surface management (surface command) focuses on getting comfortable with the interface and terminology while starting to map your external attack surface.
5 Step Attack Surface Management Guide Elasticito Tenable attack surface management (formerly known as tenable.asm) is a web based inventory tool that you can use to identify internet accessible assets that may or may not be known to your organization. Before you get started with cortex xdr attack surface management, review the topics in this section to better understand what attack surface management is, what the key use cases are, and how it works. To help you get started, attack surface management provides 120 policy and procedure templates to help your organization build your security program and operations. Discover what attack surface management is, how it enhances your security posture, and how to protect your digital assets with microsoft security.
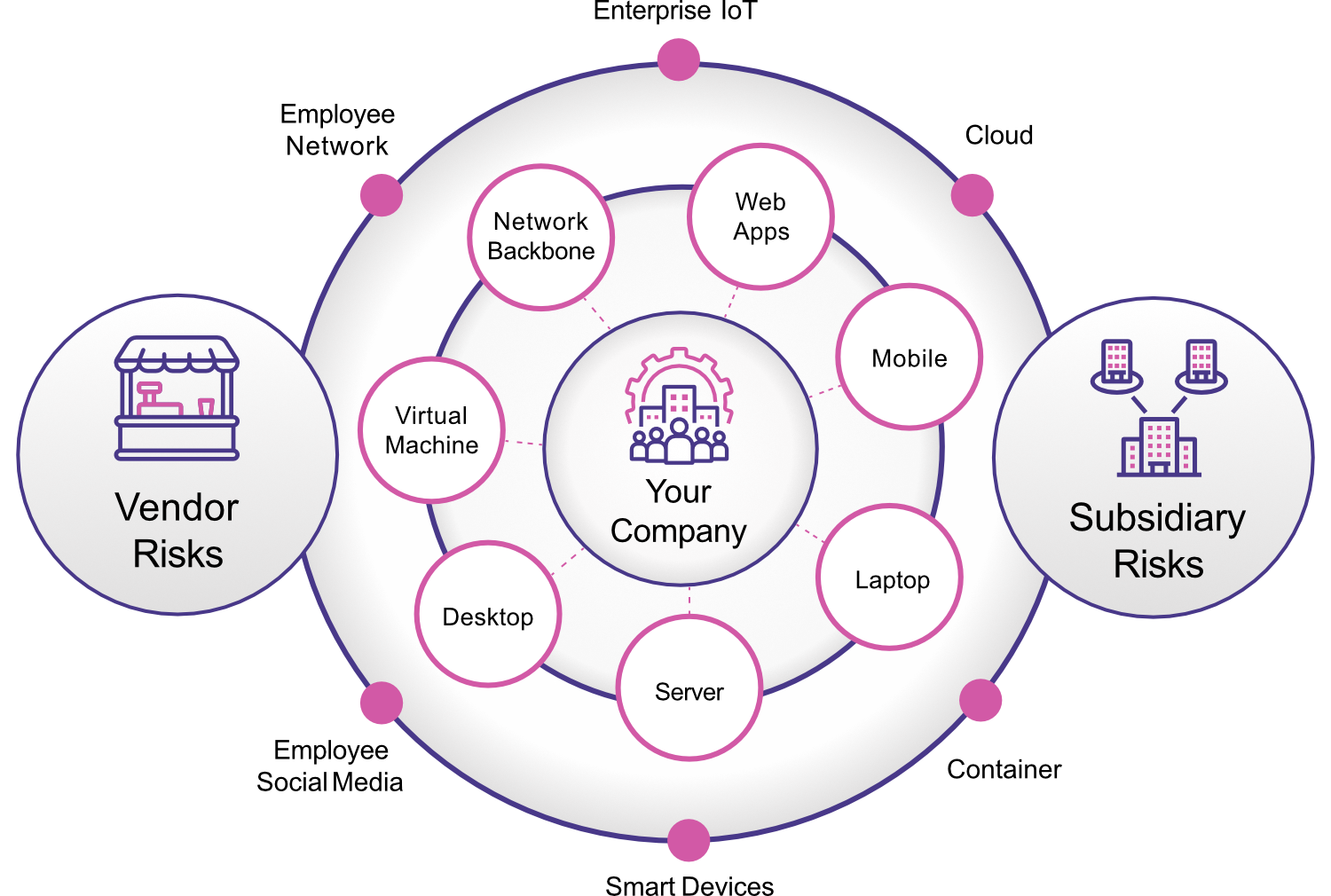
Attack Surface Management Complete Visibility Threat Protection To help you get started, attack surface management provides 120 policy and procedure templates to help your organization build your security program and operations. Discover what attack surface management is, how it enhances your security posture, and how to protect your digital assets with microsoft security. Learn what attack surface management is, the asm lifecycle, types of attack surfaces, and how to build an effective asm program. includes case studies and compliance mapping. Discover what attack surface management is and how to build a program that fixes security exposures instead of just generating more alerts and lists. Set up your attack surface get started by going here, clicking the button in the top right, and adding items to your attack surface. not much showing up? scan monster may take awhile after signing up to scan your entire attack surface. you'll get an email when results are ready!. A practical guide to attack surface management, covering easm vs caasm vs asm, the gartner ctem framework, asset discovery, risk prioritization, shadow it detection, and measuring attack surface reduction.

Attack Surface Management Redhunt Labs Learn what attack surface management is, the asm lifecycle, types of attack surfaces, and how to build an effective asm program. includes case studies and compliance mapping. Discover what attack surface management is and how to build a program that fixes security exposures instead of just generating more alerts and lists. Set up your attack surface get started by going here, clicking the button in the top right, and adding items to your attack surface. not much showing up? scan monster may take awhile after signing up to scan your entire attack surface. you'll get an email when results are ready!. A practical guide to attack surface management, covering easm vs caasm vs asm, the gartner ctem framework, asset discovery, risk prioritization, shadow it detection, and measuring attack surface reduction.

Mastering Attack Surface Management Set up your attack surface get started by going here, clicking the button in the top right, and adding items to your attack surface. not much showing up? scan monster may take awhile after signing up to scan your entire attack surface. you'll get an email when results are ready!. A practical guide to attack surface management, covering easm vs caasm vs asm, the gartner ctem framework, asset discovery, risk prioritization, shadow it detection, and measuring attack surface reduction.

Qualys Guide For Attack Surface Management Qualys Inc
Comments are closed.