Forgetalks Beyond Authentication
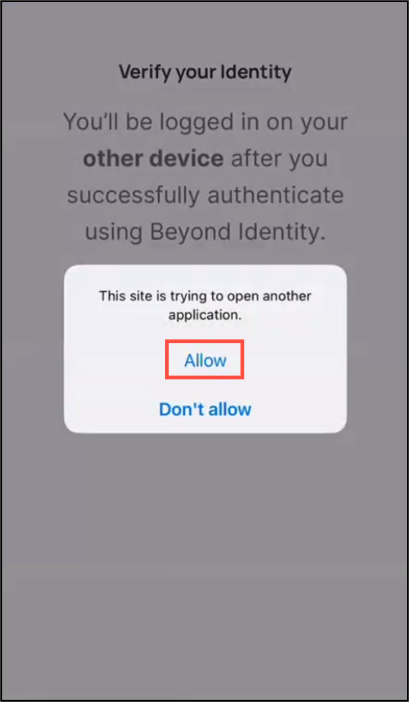
Roaming Authentication End User Beyond Identity Next Generation Docs This article explains how the protectionpolicy registry key can cause beyond identity platform authenticator passkeys to become invalid after a forced windows password reset, and provides steps to identify and resolve the issue. The second forgetalks episode with ben and frank is now live! tune in for a conversation described by frank as "riveting" and by ben as "a highlight of his existence!".

Going Beyond Authentication Cyber Security Magazine Troubleshoot authentication errors and issues for beyondinsight and password safe. These failures make a clear case for the future of authentication beyond passwords: approaches that reduce reliance on human generated secrets and introduce stronger cryptographic protections. Authentication without secrets: inside the world of passkeys if you’ve ever forgotten a password, reused one you shouldn’t have (don’t lie), or waited anxiously for an otp that never arrived …. Learn effective passkey recovery and management strategies for secure, user friendly passwordless authentication. implement fallback methods and enhance security.

The Future Of Authentication Beyond Passwords Sixmedium Authentication without secrets: inside the world of passkeys if you’ve ever forgotten a password, reused one you shouldn’t have (don’t lie), or waited anxiously for an otp that never arrived …. Learn effective passkey recovery and management strategies for secure, user friendly passwordless authentication. implement fallback methods and enhance security. Passwords have been the primary method of online authentication for decades. however, they are increasingly becoming a security risk due to weak password practices, phishing attacks, and data breaches. We have a scenario where, based on the username collected in the tree, we intend to invalidate all the sessions associated with the provided username. how can we obtain the sso token of an administrative user in an authentication decision script?. This article explains how beyond identity passkeys are handled when the authenticator is uninstalled, when user profiles change, or when a device is reimaged. it also outlines how these actions are reflected in the admin console. In this whitepaper, you will learn about the features and benefits of forgerock intelligent access, including user journeys, nodes and the trust network.

Beyond Passwords Exploring Advanced Authentication Methods Securityhq Passwords have been the primary method of online authentication for decades. however, they are increasingly becoming a security risk due to weak password practices, phishing attacks, and data breaches. We have a scenario where, based on the username collected in the tree, we intend to invalidate all the sessions associated with the provided username. how can we obtain the sso token of an administrative user in an authentication decision script?. This article explains how beyond identity passkeys are handled when the authenticator is uninstalled, when user profiles change, or when a device is reimaged. it also outlines how these actions are reflected in the admin console. In this whitepaper, you will learn about the features and benefits of forgerock intelligent access, including user journeys, nodes and the trust network.

Beyond Passwords Exploring Advanced Authentication Methods Securityhq This article explains how beyond identity passkeys are handled when the authenticator is uninstalled, when user profiles change, or when a device is reimaged. it also outlines how these actions are reflected in the admin console. In this whitepaper, you will learn about the features and benefits of forgerock intelligent access, including user journeys, nodes and the trust network.
Comments are closed.