Firewall Security Settings For Awaberry

Panduan Setting Firewall Pdf This page allows you to manage the security settings of your awaberry device. you can configure various aspects of device security, including end to end encryption, firewall rules, ssh (secure shell) port access, and administrator access. Ready to lock down your devices without losing access? in this tutorial, we dive into awaberry's firewall security settings to deliver secure, zero trust rem.
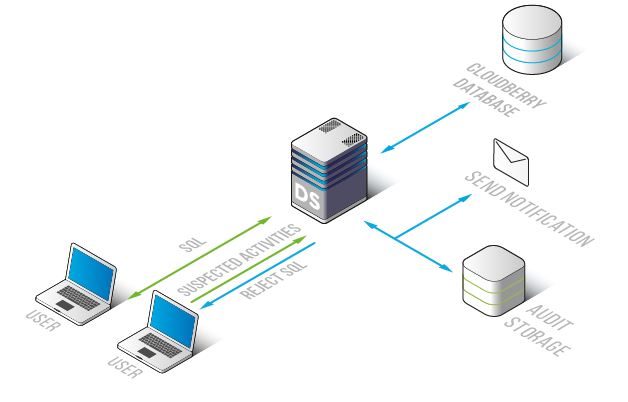
Datasunrise Firewall For Cloudberry Database Advanced Security Awaberry secure and seamless remote access to devices and automation access your devices via web browser from anywhere requires no ssh, no vpn, no port forwarding, no open firewall ports!. In this guide, we use the login via google. on the first login, awaberry asks you to setup the two factor authentification, which is important, because it protects your personal encryption key. Awaberry agentic allows to access devices connected to awaberry remote via an api. automate tasks via scripts and to integrate them into agentic frameworks. setup projects via agentic to receive api keys for access to the api. client implementations are available for python, javascript based on node.js and typescript and java. This page allows you to configure your device's security settings, including firewall rules, ssh connection encryption, and automated administrator access.

Windows Defender Firewall Is Using Settings That Make The Device Unsafe Awaberry agentic allows to access devices connected to awaberry remote via an api. automate tasks via scripts and to integrate them into agentic frameworks. setup projects via agentic to receive api keys for access to the api. client implementations are available for python, javascript based on node.js and typescript and java. This page allows you to configure your device's security settings, including firewall rules, ssh connection encryption, and automated administrator access. The device security settings panel gives you transparent control over every layer of protection — encryption, firewalls and ssh port exposure — without requiring cybersecurity expertise. This page allows you to manage your awaberry account settings, including security, subscriptions, usage, and data management. Devices behind nat, mobile data connections, or strict enterprise firewalls are fully supported — network administrators observing traffic see standard outbound https. Learn how the awaberry protocol eliminates open ports, vpns, and reverse tunnels through certificate based end to end encryption and zero trust architecture for secure device access.

Setting Up A Firewall On Your Raspberry Pi Pi My Life Up The device security settings panel gives you transparent control over every layer of protection — encryption, firewalls and ssh port exposure — without requiring cybersecurity expertise. This page allows you to manage your awaberry account settings, including security, subscriptions, usage, and data management. Devices behind nat, mobile data connections, or strict enterprise firewalls are fully supported — network administrators observing traffic see standard outbound https. Learn how the awaberry protocol eliminates open ports, vpns, and reverse tunnels through certificate based end to end encryption and zero trust architecture for secure device access.

Setting Up A Firewall On Your Raspberry Pi Pi My Life Up Devices behind nat, mobile data connections, or strict enterprise firewalls are fully supported — network administrators observing traffic see standard outbound https. Learn how the awaberry protocol eliminates open ports, vpns, and reverse tunnels through certificate based end to end encryption and zero trust architecture for secure device access.
Comments are closed.