Finding Security Vulnerabilities Through Code Review The Owasp Way

Owasp Code Review Guide V2 1 10 Pdf Source Code Unit Testing This cheat sheet provides practical guidance for conducting effective manual security code reviews, with emphasis on both baseline and incremental review methodologies. The owasp code review guide helps developers, security professionals, and management improve application security through systematic code reviews. it has become a cornerstone of web application security, providing detailed processes and techniques for identifying and fixing vulnerabilities.

Owasp Code Review Guide V2 21 30 Pdf Security Computer Security This secure code review checklist helps code reviewers find security vulnerabilities and security bugs. In this guide, you'll learn why code review checklists are important to security, how to tailor a java secure code review checklist, and apply an owasp security code review checklist to any language. Use this security code review checklist to find security vulnerabilities and privacy issues, and remember the owasp top 10. Learn how to run secure code reviews that catch vulnerabilities early. explore process steps, tools, owasp tips, and real world coding practices.
Github Owasp Codereviewguide Repository For Owasp Code Review Document Use this security code review checklist to find security vulnerabilities and privacy issues, and remember the owasp top 10. Learn how to run secure code reviews that catch vulnerabilities early. explore process steps, tools, owasp tips, and real world coding practices. Her focus for this session is to give you an overview of the best practices and recommendations from the owasp code review task force. in addition, michaela will share insights from her. This project is a python based tool designed to detect security vulnerabilities in source code using static analysis. it integrates two powerful security analyzers — sonarqube and bandit — to identify owasp top 10 issues like injection flaws, insecure deserialization, and insecure apis in python applications. It’s the process of evaluating application source code for security flaws—combining automated scanning and manual analysis—to find vulnerabilities before deployment. In this one hour session, michaela outlines the fundamentals of using the power of code reviews to detect security vulnerabilities. her focus for this session is to give you an overview of the best practices and recommendations from the owasp code review task force.
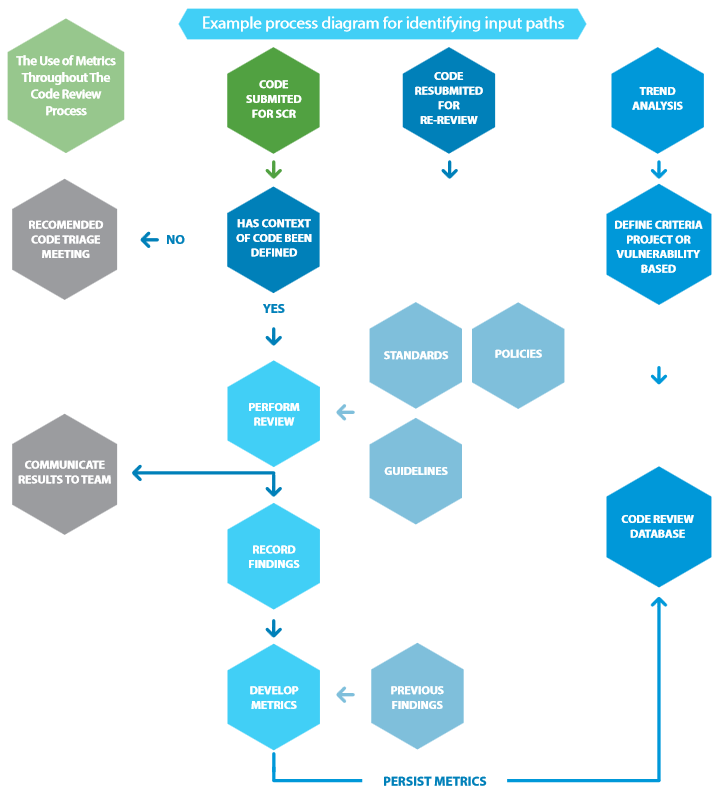
Owasp Secure Code Review A Comprehensive Step By Step Guide Her focus for this session is to give you an overview of the best practices and recommendations from the owasp code review task force. in addition, michaela will share insights from her. This project is a python based tool designed to detect security vulnerabilities in source code using static analysis. it integrates two powerful security analyzers — sonarqube and bandit — to identify owasp top 10 issues like injection flaws, insecure deserialization, and insecure apis in python applications. It’s the process of evaluating application source code for security flaws—combining automated scanning and manual analysis—to find vulnerabilities before deployment. In this one hour session, michaela outlines the fundamentals of using the power of code reviews to detect security vulnerabilities. her focus for this session is to give you an overview of the best practices and recommendations from the owasp code review task force.
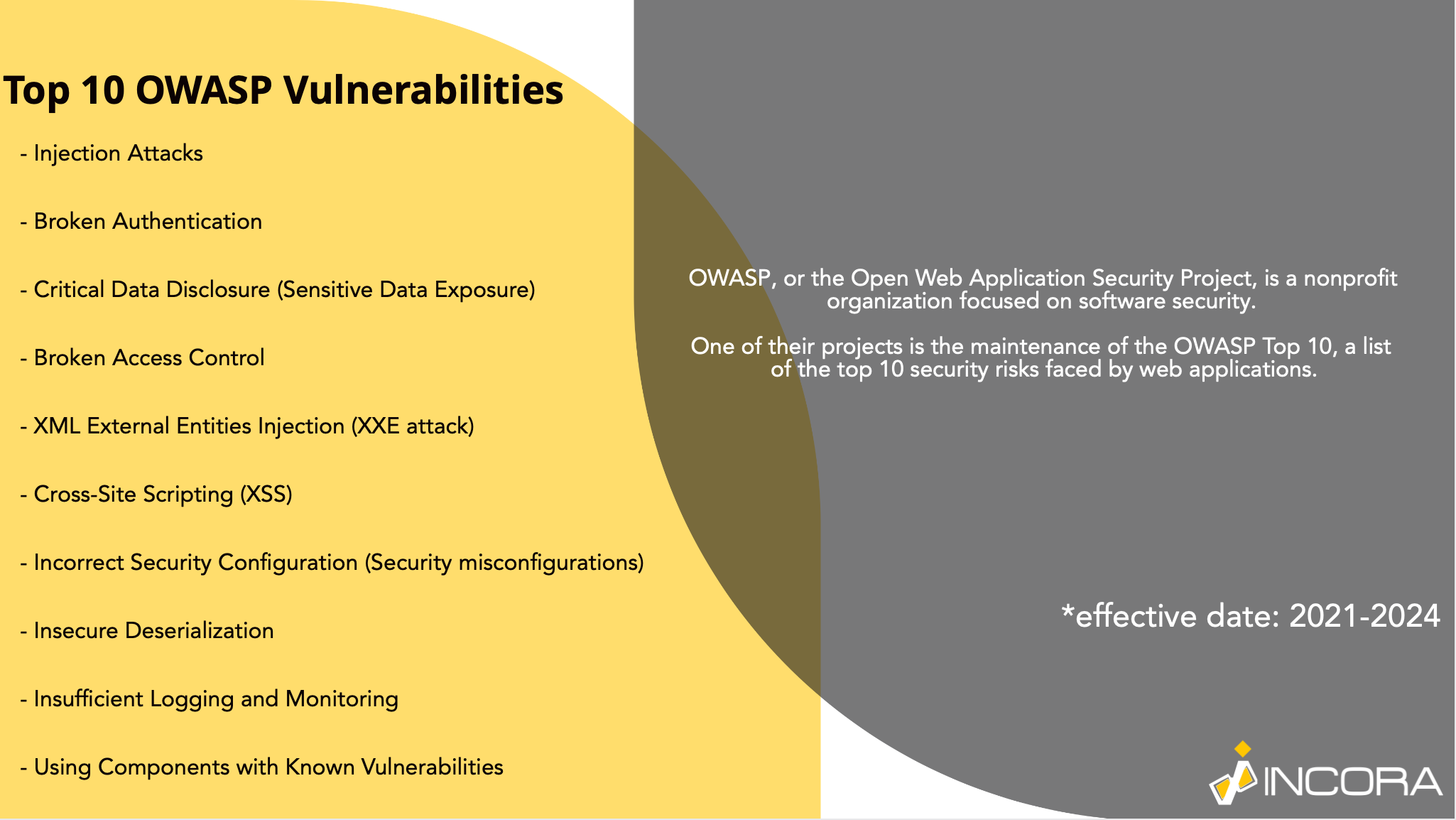
Going Through Top 10 Owasp Vulnerabilities It’s the process of evaluating application source code for security flaws—combining automated scanning and manual analysis—to find vulnerabilities before deployment. In this one hour session, michaela outlines the fundamentals of using the power of code reviews to detect security vulnerabilities. her focus for this session is to give you an overview of the best practices and recommendations from the owasp code review task force.
Github Owasp Www Project Code Review Guide Owasp Foundation Web
Comments are closed.