Final Project Presentation How To Compress Encrypted Data

Project Pdf Encryption Cryptography About press copyright contact us creators advertise developers terms privacy policy & safety how works test new features nfl sunday ticket © 2023 google llc. This capstone project report presents a method for secure and efficient file compression and encryption by integrating aes 256 encryption with adaptive lossless techniques.

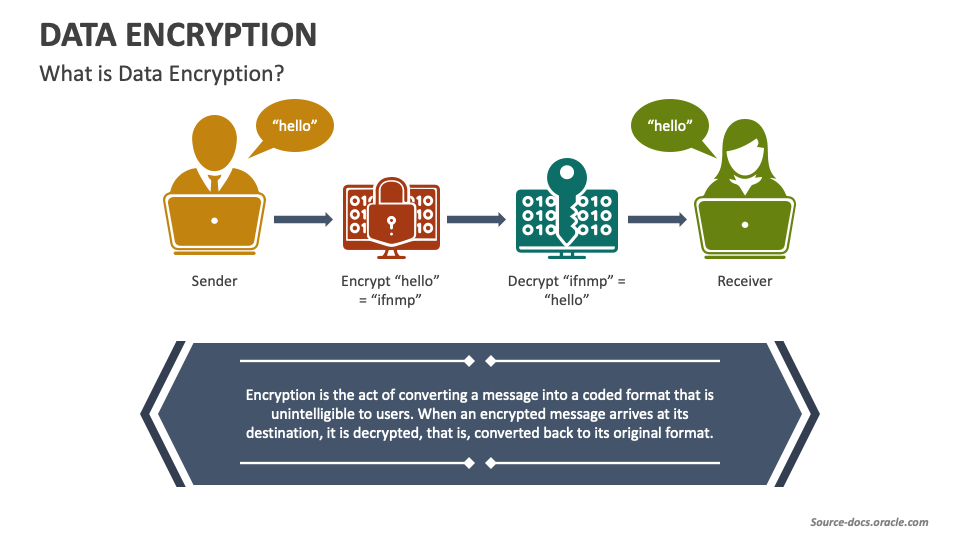
A Level 14 Presentation Compression Encryption And Hashing Pdf We present two new algorithms with provable worst case guarantees, solving this problem by using only homomorphic additions and multiplications by constants. both of our new constructions improve upon the state of the art asymptotically and concretely. Cryptography includes a set of techniques for scrambling or disguising data so that it is available only to someone who can restore the data to its original form. The report provides an introduction to the need for data encryption, describes the project requirements and design. it also includes screenshots and code snippets demonstrating how the project allows users to encrypt and decrypt data either directly or from files using caesar cipher encryption. Explore a comprehensive project report on aes based file encryption and decryption, highlighting user friendly design and robust security features.
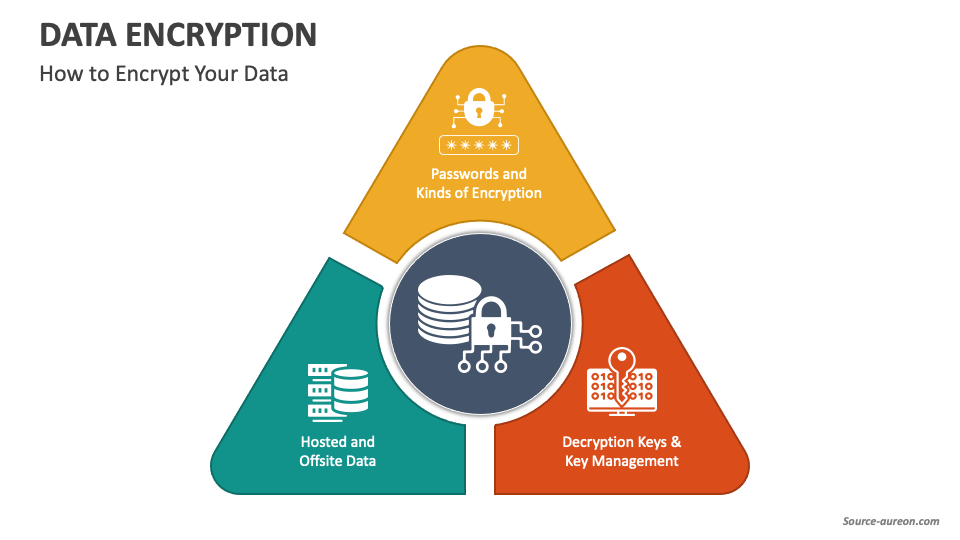
Data Encryption Powerpoint And Google Slides Template Ppt Slides The report provides an introduction to the need for data encryption, describes the project requirements and design. it also includes screenshots and code snippets demonstrating how the project allows users to encrypt and decrypt data either directly or from files using caesar cipher encryption. Explore a comprehensive project report on aes based file encryption and decryption, highlighting user friendly design and robust security features. We present two new algorithms with provable worst case guarantees, solving this problem by using only homomorphic additions and multiplications by constants. both of our new constructions improve upon the state of the art asymptotically and concretely. These encrypted data projects give practical experience and help complete final year submissions. all projects follow ieee standards and each project includes source code, project thesis report, presentation, project execution and explanation. We present two new algorithms, one based on polynomials and one based on algorithmic hashing, for com pressing sparse encrypted vectors, which both improve upon the prior state of the art in terms of compression rate. Leveraging insights from chaos theory, cryptography, and compression studies, this research embarks on the development of a tightly integrated compression and encryption scheme, aiming to unpredictably vary data compression while upholding data integrity.
Data Encryption Powerpoint And Google Slides Template Ppt Slides We present two new algorithms with provable worst case guarantees, solving this problem by using only homomorphic additions and multiplications by constants. both of our new constructions improve upon the state of the art asymptotically and concretely. These encrypted data projects give practical experience and help complete final year submissions. all projects follow ieee standards and each project includes source code, project thesis report, presentation, project execution and explanation. We present two new algorithms, one based on polynomials and one based on algorithmic hashing, for com pressing sparse encrypted vectors, which both improve upon the prior state of the art in terms of compression rate. Leveraging insights from chaos theory, cryptography, and compression studies, this research embarks on the development of a tightly integrated compression and encryption scheme, aiming to unpredictably vary data compression while upholding data integrity.
Data Encryption Powerpoint And Google Slides Template Ppt Slides We present two new algorithms, one based on polynomials and one based on algorithmic hashing, for com pressing sparse encrypted vectors, which both improve upon the prior state of the art in terms of compression rate. Leveraging insights from chaos theory, cryptography, and compression studies, this research embarks on the development of a tightly integrated compression and encryption scheme, aiming to unpredictably vary data compression while upholding data integrity.
Comments are closed.