File Encryption With Gpg
Encrypting And Decrypting Files With Gpg How to use gpg to encrypt and decrypt files learn how gpg encryption protects your data through authenticity, integrity and nonrepudiation. this guide covers installation and symmetric and asymmetric cryptography basics. It’s easy to get started with gpg, and you can be on your way with using it in a matter of minutes. in this tutorial, i’ll show you how to encrypt and decrypt files with gpg.

File Encryption With Gpg In this article, we show you how to encrypt files with gpg in linux, generate key pairs, share encrypted files securely, and decrypt them. Protect your privacy with the linux gpg command. use world class encryption to keep your secrets safe. we'll show you how to use gpg to work with keys, encrypt files, and decrypt them. gnuprivacy guard (gpg) allows you to securely encrypt files so that only the intended recipient can decrypt them. The procedure for encrypting and decrypting documents is straightforward with this mental model. if you want to encrypt a message to alice, you encrypt it using alice's public key, and she decrypts it with her private key. In this guide, we’ll walk through everything you need to know to start using gpg effectively: from installing the tool and generating key pairs to encrypting decrypting files, troubleshooting issues, and advanced tips for enhanced security.
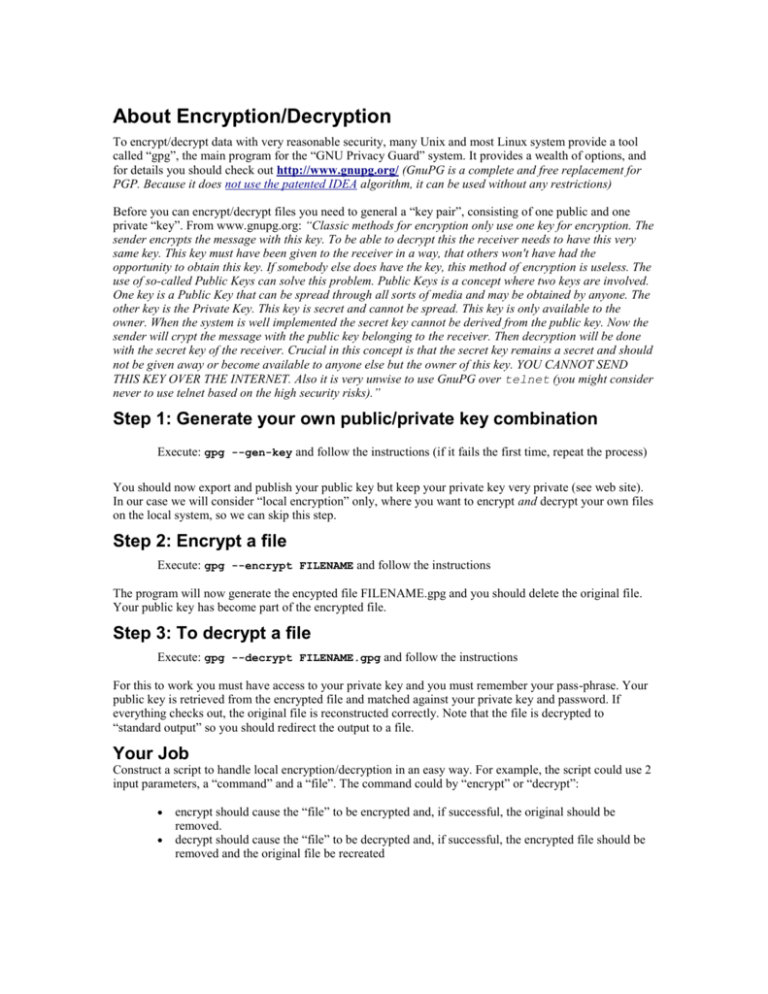
Gpg Encryption The procedure for encrypting and decrypting documents is straightforward with this mental model. if you want to encrypt a message to alice, you encrypt it using alice's public key, and she decrypts it with her private key. In this guide, we’ll walk through everything you need to know to start using gpg effectively: from installing the tool and generating key pairs to encrypting decrypting files, troubleshooting issues, and advanced tips for enhanced security. Of course, gpg has many more options than i've shown here. but these three are easy to use encryption and decryption options that will get you started protecting your files right away. Discover how to protect sensitive data using `gpg`, a robust encryption tool, as cybersecurity threats increase. this guide covers everything from `gpg` installation across various operating systems to generating key pairs and encrypting decrypting files. In this comprehensive guide, i‘ll demonstrate how to leverage gpg (gnu privacy guard) to encrypt files and directories on your linux machines using secure passphrases. This guide focuses on disk encryption with luks and dm crypt, file level encryption with gpg and ecryptfs, encrypted usb drives, and key management best practices.
Comments are closed.