Figure 3 Password Cracking Attack Done By Multiple Ips
Attack Wrangles Thousands Of Web Users Into A Password Cracking Botnet Capture 2 delves into a potential denial of service (dos) attack and a brute force password cracking attempt, showcasing how attackers attempt to disrupt services and gain unauthorized access to critical systems. When a hacker uses multiple ip addresses to carry out an attack, it's often referred to as “ip spoofing”. this involves sending traffic from numerous, seemingly legitimate ip addresses, which makes it difficult for the target to determine the true source of the attack.
Password Cracking Statistics On Password Security Most sites will detect repeated password attempts from the same ip, so the attacker needs to use multiple ips to extend the number of passwords they can try before being detected. In this scenario, since the attacker is on path, the attacker is able to see the port numbers and sequence addresses of the current stream, and can construct their own packets with malicious payloads to inject into the stream with the fully correct values. If a client is connected to a wireless router via wpa3, and the router has wpa3 transition feature enabled, an attacker can create a fake wpa2 access point, force the client to connect to it via wpa2, capture the handshake and crack the wi fi network’s password. Through user generated password surveys, we evaluate the crackability of three word passwords using dictionaries of varying common word proportions.

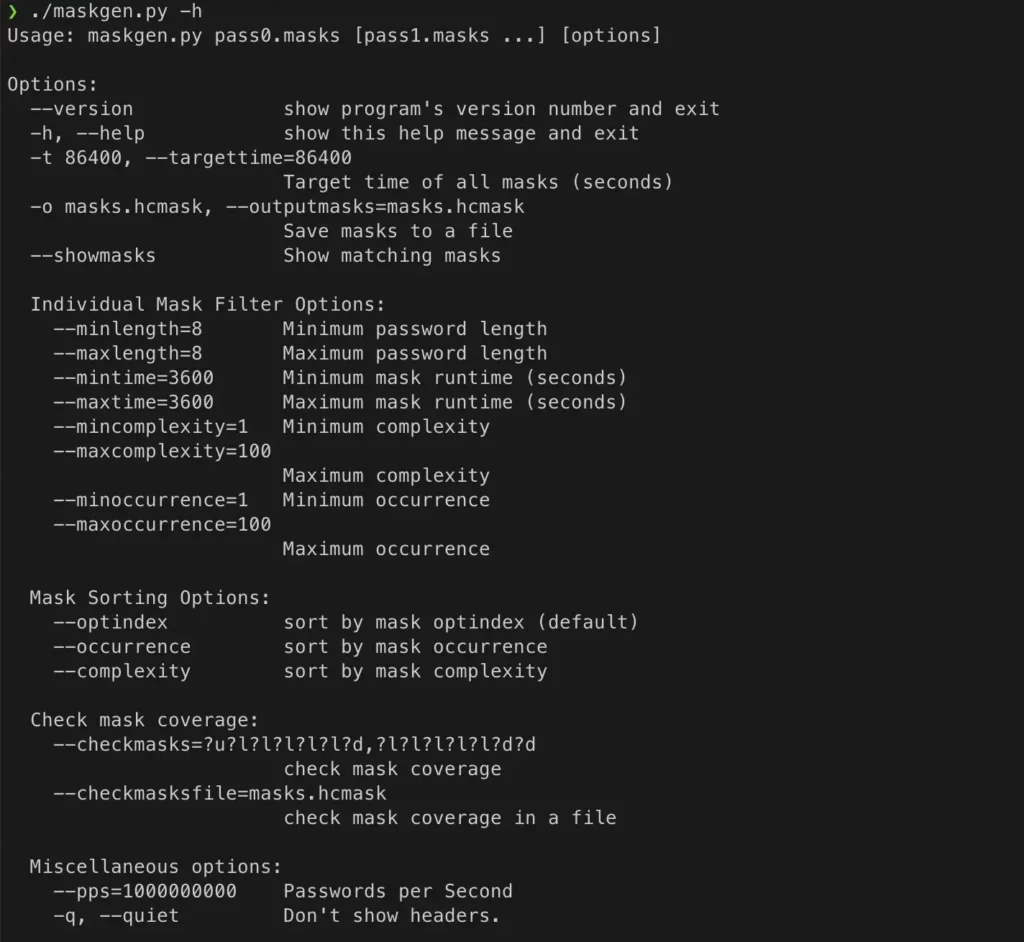
5 Password Cracking Techniques Used In Cyber Attacks Proofpoint Us If a client is connected to a wireless router via wpa3, and the router has wpa3 transition feature enabled, an attacker can create a fake wpa2 access point, force the client to connect to it via wpa2, capture the handshake and crack the wi fi network’s password. Through user generated password surveys, we evaluate the crackability of three word passwords using dictionaries of varying common word proportions. A brute force algorithm generates all possible combinations of characters in a specified range and length, while the dictionary attack checks against a predefined word list. this study compares the efficiency of these methods using parallel versions of python, c , and hashcat. Most methods of password cracking require the computer to produce many candidate passwords, each of which is checked. one example is brute force cracking, in which a computer tries every possible key or password until it succeeds. A brute force algorithm generates all possible combinations of characters in a specified range and length, while the dictionary attack checks against a predefined word list. Password guessing is a technique used to target online protocols and services. therefore, it’s considered time consuming and opens up the opportunity to generate logs for the failed login.

Password Cracking 101 Attacks Defenses Explained Beyondtrust A brute force algorithm generates all possible combinations of characters in a specified range and length, while the dictionary attack checks against a predefined word list. this study compares the efficiency of these methods using parallel versions of python, c , and hashcat. Most methods of password cracking require the computer to produce many candidate passwords, each of which is checked. one example is brute force cracking, in which a computer tries every possible key or password until it succeeds. A brute force algorithm generates all possible combinations of characters in a specified range and length, while the dictionary attack checks against a predefined word list. Password guessing is a technique used to target online protocols and services. therefore, it’s considered time consuming and opens up the opportunity to generate logs for the failed login.

Cyber Attack Password Cracking Vulnerability In Text Binary System A brute force algorithm generates all possible combinations of characters in a specified range and length, while the dictionary attack checks against a predefined word list. Password guessing is a technique used to target online protocols and services. therefore, it’s considered time consuming and opens up the opportunity to generate logs for the failed login.
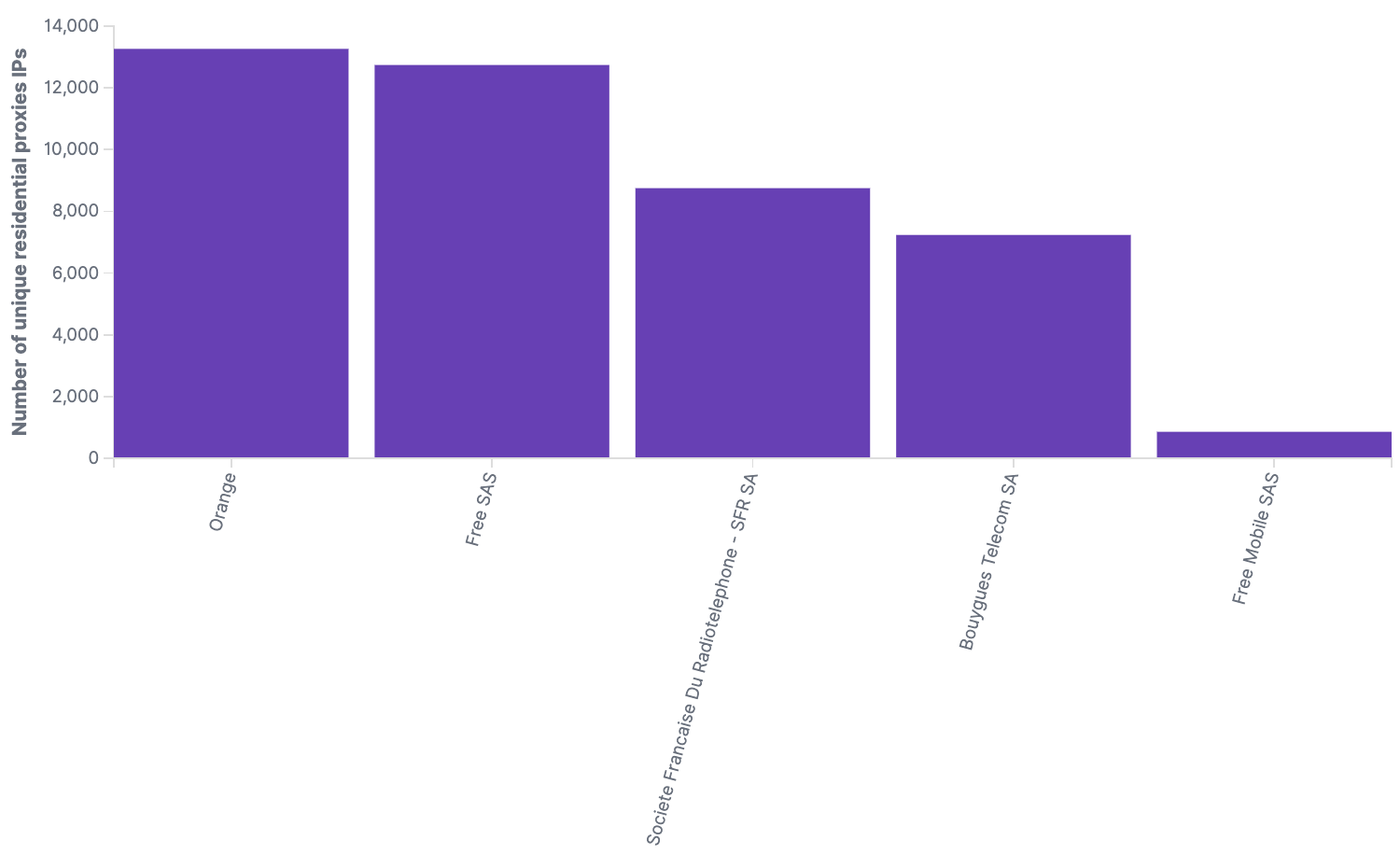
Anatomy Of A Distributed Scraping Attack
Comments are closed.