Figure 1 Full Autonomous Artificial Intelligence In Attack

Figure 1 Full Autonomous Artificial Intelligence In Attack Security researchers document the first completely autonomous ai driven cyberattack where artificial intelligence systems managed the entire attack lifecycle from reconnaissance to data exfiltration without human intervention. The first section presents the full autonomous artificial intelligence in attack or defense decisions making in military drones’ system box (the neurondrone box) to adapt to any drone to the main control system of any drone.
Figure 5 Full Autonomous Artificial Intelligence In Attack This research paper introduces the full autonomous artificial intelligence in attack or defense decisions making in military drones’ system box (the neurondrone box): the hardware,. This paper describes an ai powered mechanism for the automatic generation of attack techniques, ranging from initial vectors to impact related actions. the research contributions provided by the present paper are summarized below. Progress in autonomous cyber operations: this appears to be the first publicly known example of ai systems autonomously conducting multi step attacks against well defended targets in the wild. This editorial dives deep into the six ai powered attack types covered in the script, the terrifying capabilities they unlock, and what this shift means for businesses, individuals, and the future of cybersecurity.
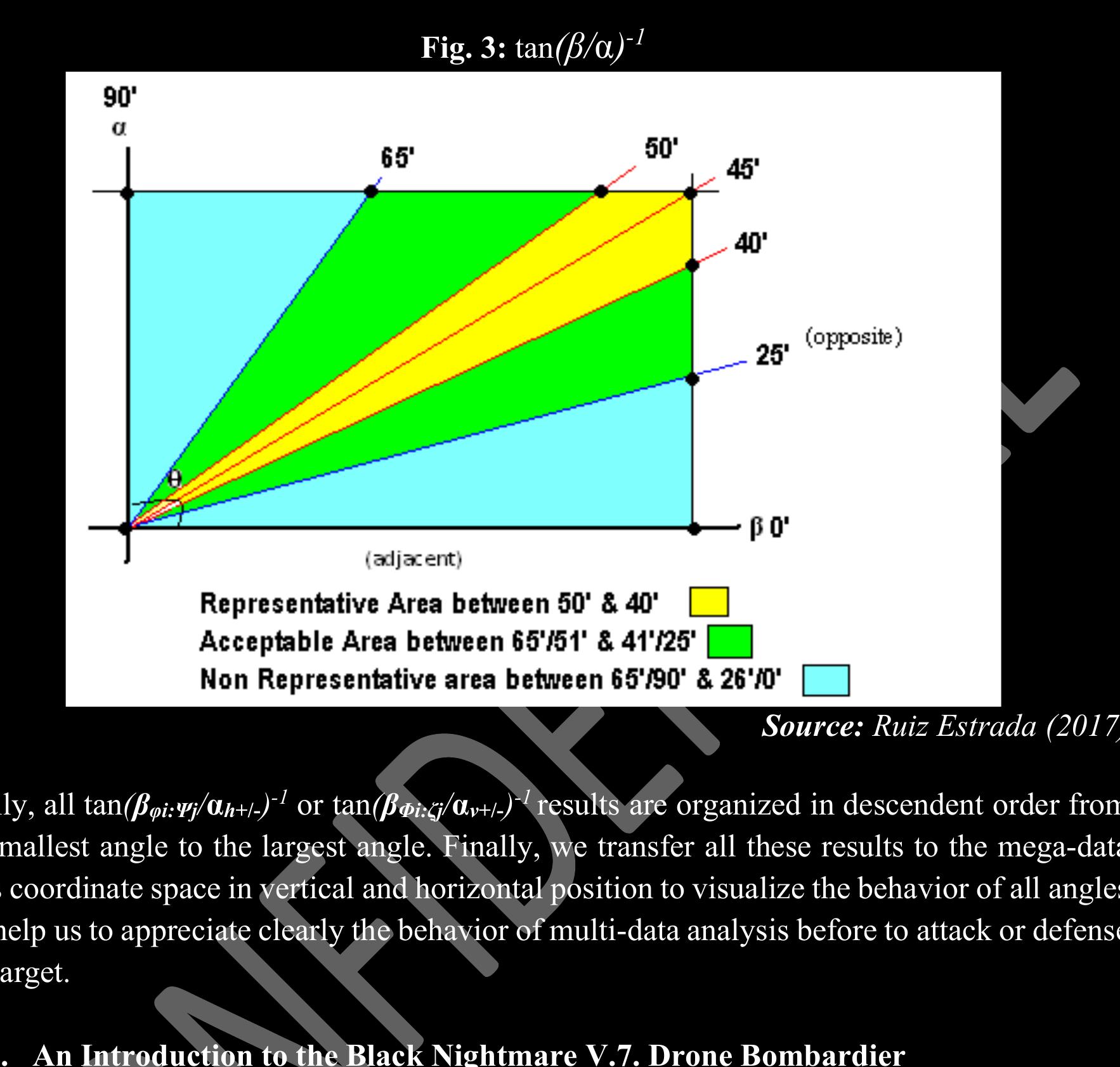
Figure 7 Full Autonomous Artificial Intelligence In Attack Progress in autonomous cyber operations: this appears to be the first publicly known example of ai systems autonomously conducting multi step attacks against well defended targets in the wild. This editorial dives deep into the six ai powered attack types covered in the script, the terrifying capabilities they unlock, and what this shift means for businesses, individuals, and the future of cybersecurity. How the cyberattack worked the attack relied on several features of ai models that did not exist, or were in much more nascent form, just a year ago: intelligence. models’ general levels of capability have increased to the point that they can follow complex instructions and understand context in ways that make very sophisticated tasks possible. Ai has introduced a new era of cybersecurity challenges by morphing the threats into layered, intelligent, and scalable attack vectors. this paper has examined four types of ai driven threats: deepfakes, adversarial attacks, automated malware, ai phishing, and ai social engineering. Learn how attackers use ai for reconnaissance, phishing, malware, and evolving botnets. understand common threats like deepfakes, ai ransomware, data poisoning, and multi channel scams. see real world cases and trends showing ai driven attacks growing in sophistication. The researchers hope that these contributions would provide valuable insights for academics, policymakers, and practitioners to better understand and address ai cybersecurity threats and opportunities holistically. the rest of the paper is structured as outlined in fig. 1.

Understanding Autonomous Artificial Intelligence The Pros And Cons How the cyberattack worked the attack relied on several features of ai models that did not exist, or were in much more nascent form, just a year ago: intelligence. models’ general levels of capability have increased to the point that they can follow complex instructions and understand context in ways that make very sophisticated tasks possible. Ai has introduced a new era of cybersecurity challenges by morphing the threats into layered, intelligent, and scalable attack vectors. this paper has examined four types of ai driven threats: deepfakes, adversarial attacks, automated malware, ai phishing, and ai social engineering. Learn how attackers use ai for reconnaissance, phishing, malware, and evolving botnets. understand common threats like deepfakes, ai ransomware, data poisoning, and multi channel scams. see real world cases and trends showing ai driven attacks growing in sophistication. The researchers hope that these contributions would provide valuable insights for academics, policymakers, and practitioners to better understand and address ai cybersecurity threats and opportunities holistically. the rest of the paper is structured as outlined in fig. 1.
Comments are closed.