Fast And Fuzzy Private Set Intersection
Fast And Fuzzy Private Set Intersection Psi algorithms to seconds or minutes. this paper introduces an algorithm to implement psi in a different way: sets are first encrypted and then c. Our new fmap instances lead to the fastest semi honest secure fpsi protocols in high dimensional space to date, for both hamming and general distances. for hamming distance, our protocol is the first one that achieves strictly linear complexity with input sizes.

Fuzzy Private Set Intersection With Large Hyperballs Traditional private set intersection (psi) involves a receiver and a sender holding sets x and y, respectively, with the receiver learning only the intersection x ∩ y. Private set intersection (psi) is usually implemented as a sequence of encryption rounds between pairs of users, whereas the present work implements psi in a simpler fashion: each set only needs to be encrypted once, after which each pair of users need only one ordinary set comparison. Private set intersection (psi) is usually implemented as a sequence of encryption rounds between pairs of users, whereas the present work implements psi in a simpler fashion: each set only needs to be encrypted once, after which each pair of users need only one ordinary set comparison. Private set intersection (psi) is a cryptographic primitive that allows two parties to compute the intersection \ (x\cap y\) of their private datasets x and y, without revealing any information about items not in the intersection.
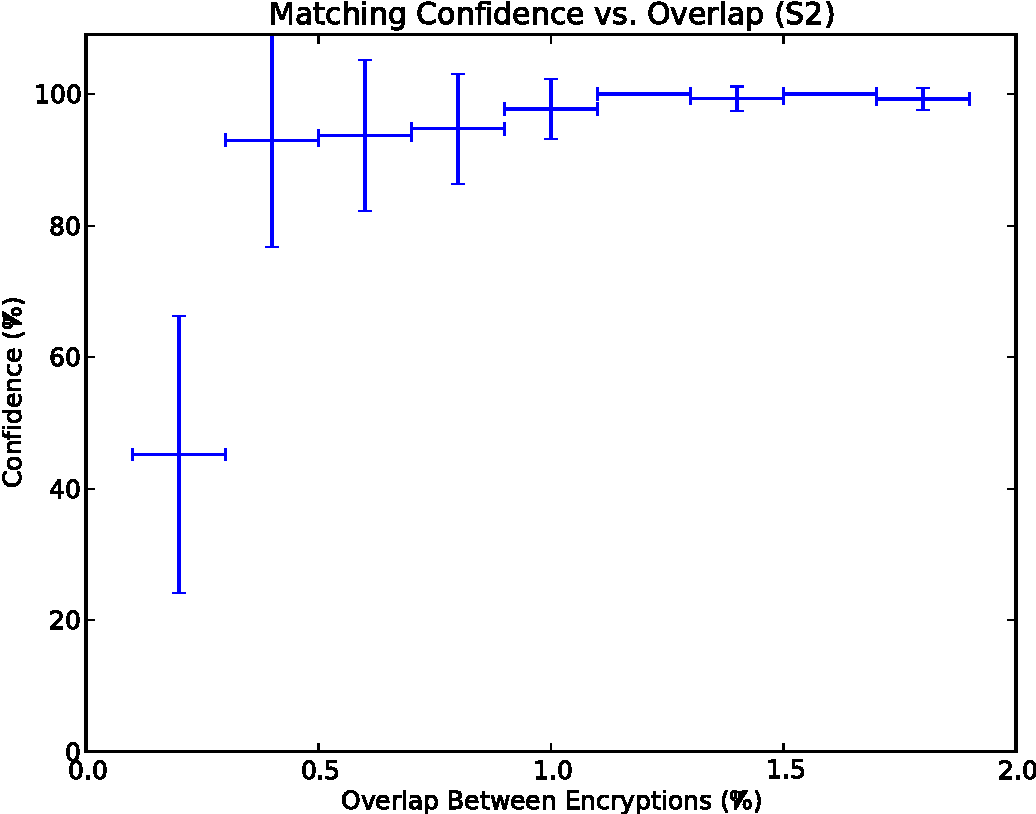
Research Project Adaptive Thresholding In Fuzzy Labeled Private Set Private set intersection (psi) is usually implemented as a sequence of encryption rounds between pairs of users, whereas the present work implements psi in a simpler fashion: each set only needs to be encrypted once, after which each pair of users need only one ordinary set comparison. Private set intersection (psi) is a cryptographic primitive that allows two parties to compute the intersection \ (x\cap y\) of their private datasets x and y, without revealing any information about items not in the intersection. We consider the problem of computing the intersection of private datasets of two parties, where the datasets contain lists of elements taken from a large domain. this problem has many. Fuzzy private set intersection from fuzzy mapping please star this repository if it is helpful for your research. that is important for me. please note that this implementation can only be used to test the efficiency of the fpsi protocols in [gql 24] (full version) for academic purposes. In this paper, we survey existing fpsi protocols in various aspects, including distance metrics supported by protocols, protocol designs, and core cryptographic tools. furthermore, we discuss (potential) technical challenges regarding deployments of them in real world application scenarios. The explosive growth of biometrics use (e.g., in surveillance) poses a persistent challenge to keep biometric data private without sacrificing the apps' functionality. we consider private querying of a real life biometric scan (e.g., a person's face) against a private biometric database.

5 Graphical View Of Fuzzy Set Intersection Operation Download We consider the problem of computing the intersection of private datasets of two parties, where the datasets contain lists of elements taken from a large domain. this problem has many. Fuzzy private set intersection from fuzzy mapping please star this repository if it is helpful for your research. that is important for me. please note that this implementation can only be used to test the efficiency of the fpsi protocols in [gql 24] (full version) for academic purposes. In this paper, we survey existing fpsi protocols in various aspects, including distance metrics supported by protocols, protocol designs, and core cryptographic tools. furthermore, we discuss (potential) technical challenges regarding deployments of them in real world application scenarios. The explosive growth of biometrics use (e.g., in surveillance) poses a persistent challenge to keep biometric data private without sacrificing the apps' functionality. we consider private querying of a real life biometric scan (e.g., a person's face) against a private biometric database.

Private Set Intersection Functionality Fpsi Download Scientific Diagram In this paper, we survey existing fpsi protocols in various aspects, including distance metrics supported by protocols, protocol designs, and core cryptographic tools. furthermore, we discuss (potential) technical challenges regarding deployments of them in real world application scenarios. The explosive growth of biometrics use (e.g., in surveillance) poses a persistent challenge to keep biometric data private without sacrificing the apps' functionality. we consider private querying of a real life biometric scan (e.g., a person's face) against a private biometric database.
Comments are closed.