Face Presentation Attack Detection Paper And Code Catalyzex
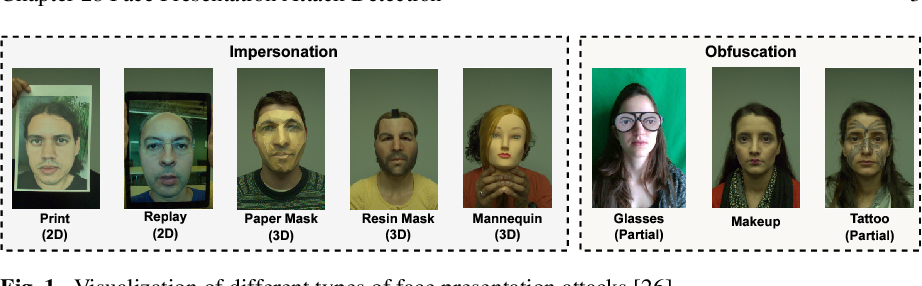
Face Presentation Attack Detection Paper And Code Catalyzex Face recognition technology has been widely used in daily interactive applications such as checking in and mobile payment due to its convenience and high accuracy. however, its vulnerability to presentation attacks (pas) limits its reliable use in ultra secure applicational scenarios. The objective of this survey is to provide a comprehensive and scholarly review of the field of face pad to readers. the survey facilitates the understanding of the overall problems of detecting facial presentation attacks, including the various types of attacks and their associated challenges.

Surveillance Face Presentation Attack Detection Challenge Deepai Face recognition technology has been widely used in daily interactive applications such as checking in and mobile payment due to its convenience and high accuracy. however, its vulnerability to presentation attacks (pas) limits its reliable use in ultra secure applicational scenarios. It is showcased that current state of the art presentation attack detection algorithms, including the foundation models, are sensitive to the amalgamation of attacks. In depth technical details of existing presentation attack detection methods are then presented and critically discussed and evaluated, followed by a comprehensive discussion and evaluation of existing public datasets and commonly used evaluation metrics. In this study, we introduced a novel evaluation protocol—leave one pai in—for assessing the generalization capabilities of face presentation attack detection models under conditions of minimal attack exposure.
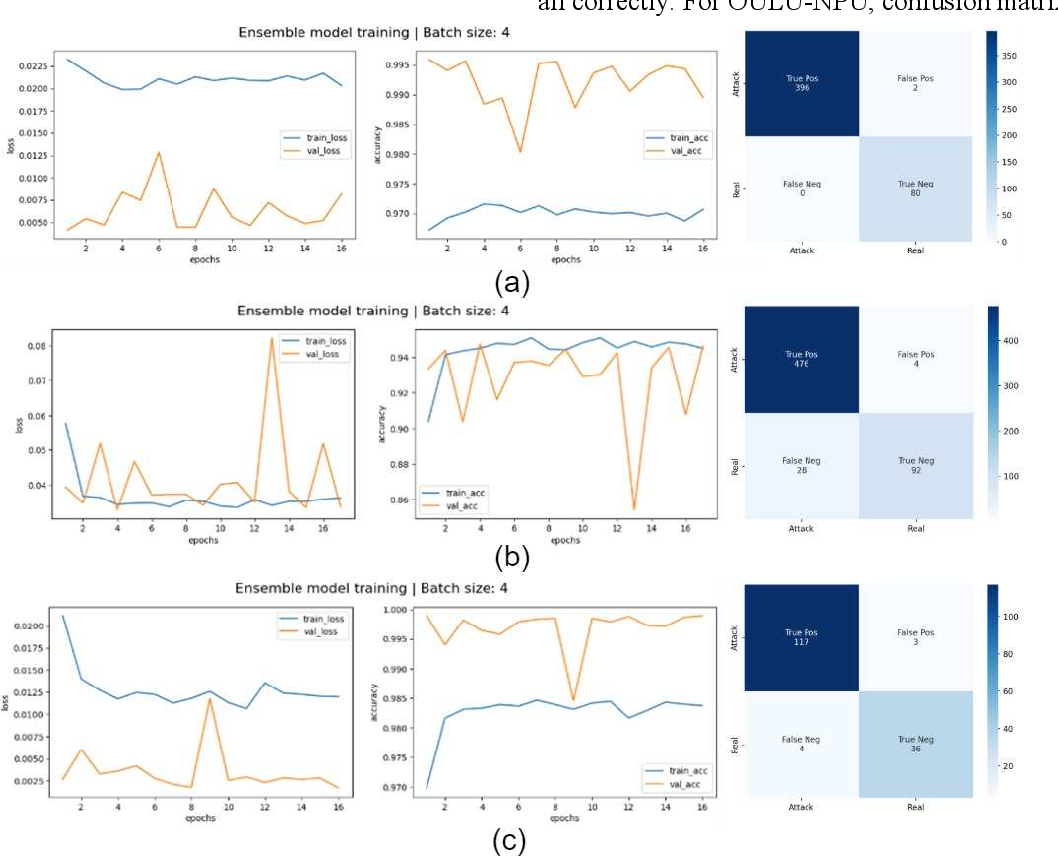
Figure 3 From Face Presentation Attack Detection Via Ensemble Learning In depth technical details of existing presentation attack detection methods are then presented and critically discussed and evaluated, followed by a comprehensive discussion and evaluation of existing public datasets and commonly used evaluation metrics. In this study, we introduced a novel evaluation protocol—leave one pai in—for assessing the generalization capabilities of face presentation attack detection models under conditions of minimal attack exposure. We propose a new framework (called synthdistill) to train lightweight face recognition models by distilling the knowledge from a pretrained teacher model using synthetic data. We have introduced an efficient dual branch convolutional neural network architecture for face presentation attack detection. utilizing a dual branch architecture that processes both facial and contextual information, our approach effectively addresses the limitations of existing methods. Many presentation attack detection (pad) methods (also known as face anti spoofing methods or countermeasures) have been proposed that can automatically detect and mitigate such targeted attacks. In this study, the fpa detection performances of both uniform lbp patterns and all lbp patterns were investigated. the size of feature vector is reduced by principal component analysis, and real fake classification is performed with support vector machines.
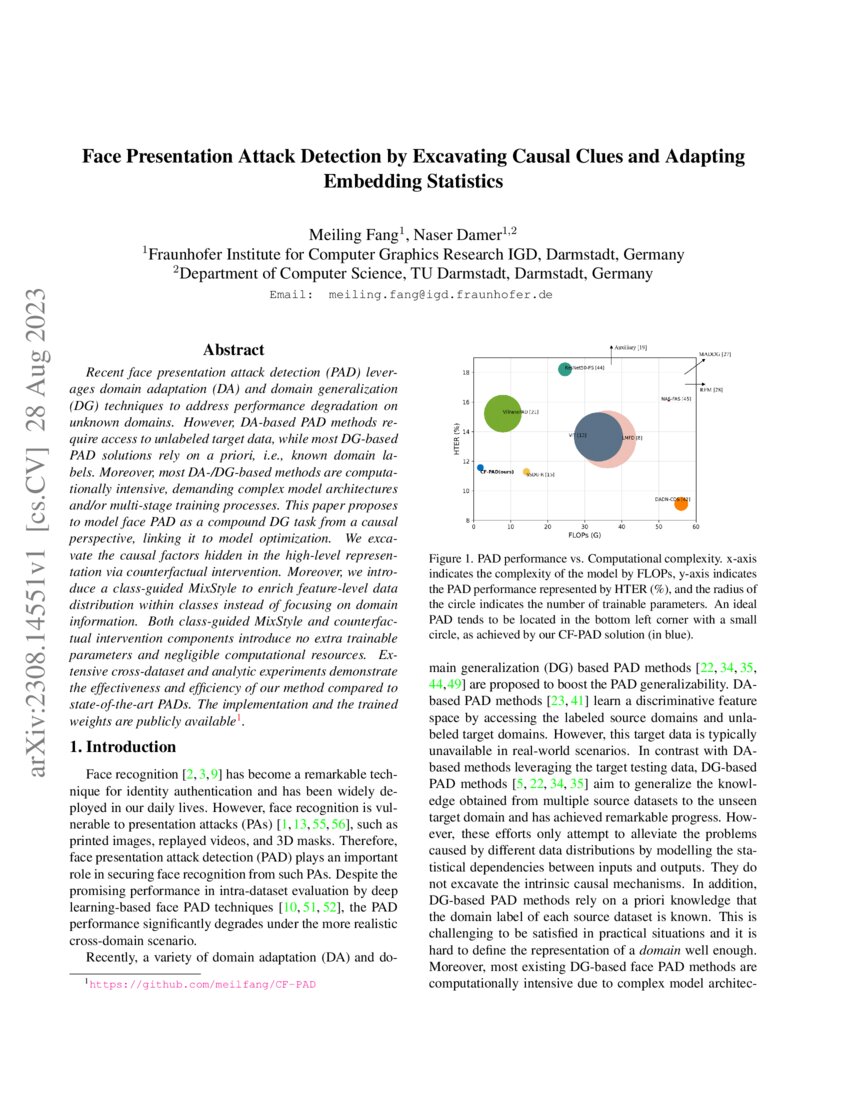
Face Presentation Attack Detection By Excavating Causal Clues And We propose a new framework (called synthdistill) to train lightweight face recognition models by distilling the knowledge from a pretrained teacher model using synthetic data. We have introduced an efficient dual branch convolutional neural network architecture for face presentation attack detection. utilizing a dual branch architecture that processes both facial and contextual information, our approach effectively addresses the limitations of existing methods. Many presentation attack detection (pad) methods (also known as face anti spoofing methods or countermeasures) have been proposed that can automatically detect and mitigate such targeted attacks. In this study, the fpa detection performances of both uniform lbp patterns and all lbp patterns were investigated. the size of feature vector is reduced by principal component analysis, and real fake classification is performed with support vector machines.
Comments are closed.