Exporting Vulnerability Assessment Results In Microsoft Defender For
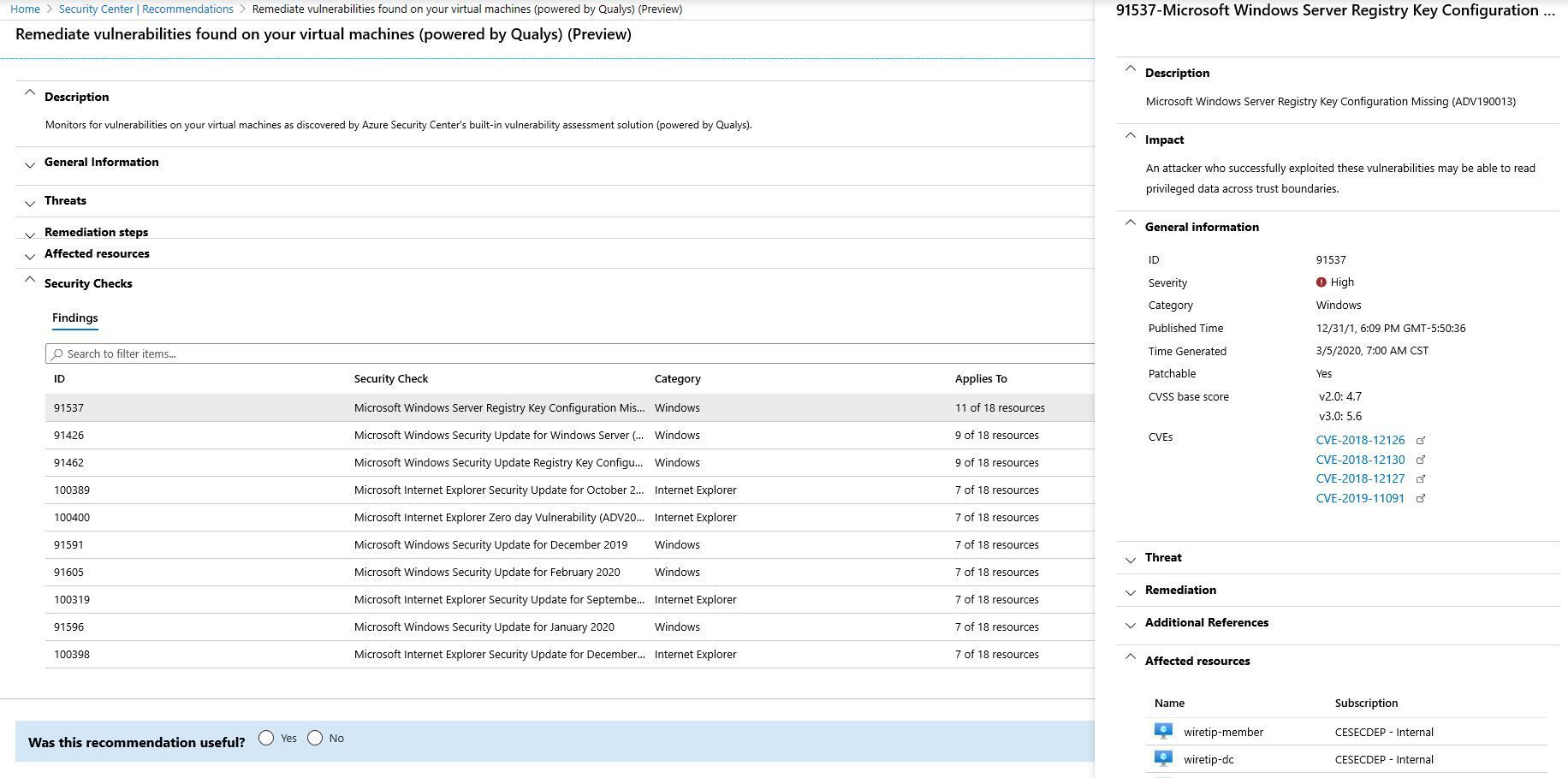
Exporting Vulnerability Assessment Results In Microsoft Defender For While this visualization is very helpful and dynamic, one question that comes up very often is: how can i export this assessment to a csv file? the answer is: you can do that using azure resource graph (arg)!. With the new microsoft defender for cloud built in vulnerability assessment solution, you can manage the deployment of the agent and the visualization of the results from a single.
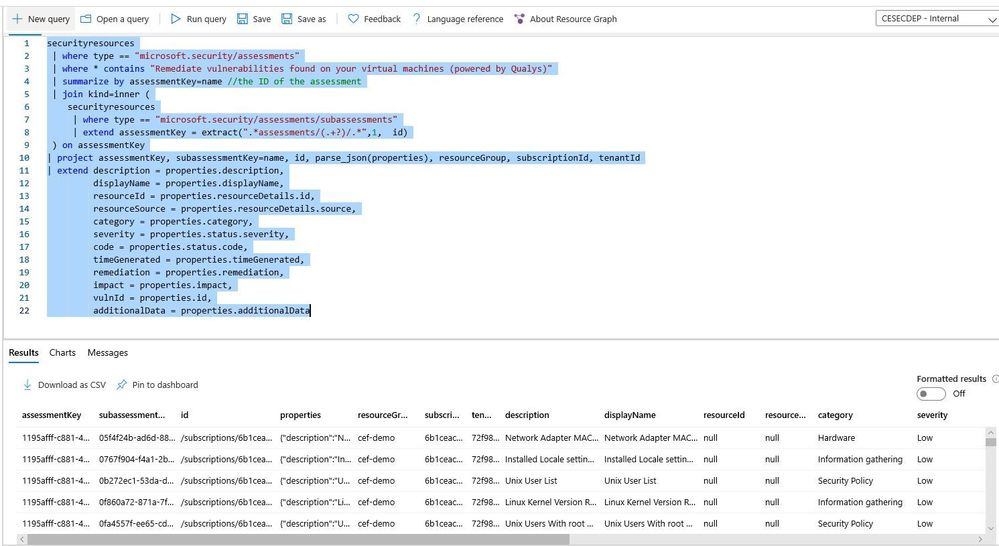
Exporting Vulnerability Assessment Results In Microsoft Defender For You can use logic app to automate the reports of your vulnerability assessment findings across all supported versions of sql, to send a weekly vulnerability report summary for any servers that were scanned. Each returned record contains all the data from the full export software vulnerabilities assessment by device api, plus two more fields: eventtimestamp and status. Defender vulnerability management provides an export api that allows programmatic access to vulnerability data. the api can be used to automate vulnerability management tasks, integrate vulnerability data with other security tools, and generate custom reports and dashboards. I'm trying to figure out how to export "device software vulnerability" into preferably xml, csv or some other format. according to the documentation it can be done via either json or "files".
Exporting Vulnerability Assessment Results In Microsoft Defender For Defender vulnerability management provides an export api that allows programmatic access to vulnerability data. the api can be used to automate vulnerability management tasks, integrate vulnerability data with other security tools, and generate custom reports and dashboards. I'm trying to figure out how to export "device software vulnerability" into preferably xml, csv or some other format. according to the documentation it can be done via either json or "files". We’ll register an app in azure ad, write a powershell script that creates automated vulnerability reports using the microsoft defender for endpoint apis, and deploy the script to azure automation for production. Complete guide to continuous vulnerability scanning with microsoft defender for cloud, including scanner setup, recommendations, remediation, and secure score optimization. If your idea of 'continuous export' is manually copying security data into a spreadsheet at 2 am, it might be time to let defender for cloud do the heavy lifting. in this blog, we’ll break down how continuous export works at scale to get all the data you need in one place. Export scan results for compliance reporting or integration with siem tools 3. this process supports the zero trust principle of "assume breach" by ensuring that known vulnerabilities are identified and resolved before they can be exploited.
Exporting Vulnerability Assessment Results In Microsoft Defender For We’ll register an app in azure ad, write a powershell script that creates automated vulnerability reports using the microsoft defender for endpoint apis, and deploy the script to azure automation for production. Complete guide to continuous vulnerability scanning with microsoft defender for cloud, including scanner setup, recommendations, remediation, and secure score optimization. If your idea of 'continuous export' is manually copying security data into a spreadsheet at 2 am, it might be time to let defender for cloud do the heavy lifting. in this blog, we’ll break down how continuous export works at scale to get all the data you need in one place. Export scan results for compliance reporting or integration with siem tools 3. this process supports the zero trust principle of "assume breach" by ensuring that known vulnerabilities are identified and resolved before they can be exploited.
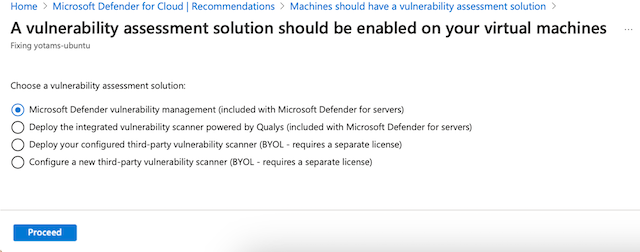
Enable Vulnerability Scanning With Microsoft Defender Vulnerability If your idea of 'continuous export' is manually copying security data into a spreadsheet at 2 am, it might be time to let defender for cloud do the heavy lifting. in this blog, we’ll break down how continuous export works at scale to get all the data you need in one place. Export scan results for compliance reporting or integration with siem tools 3. this process supports the zero trust principle of "assume breach" by ensuring that known vulnerabilities are identified and resolved before they can be exploited.
Comments are closed.