Exploit Javamaliciousinboundsocket And Minecraft Server Exploit

Patch Your Minecraft Server Now To Avoid Huge Java Exploit I am hosting a modded minecraft server (1.16) on my home pc, and started seeing malwarebytes detect and block exploit.javamaliciousinboundsocket everytime a specific friend tried to join the server. In this post, we covered the solution of hackthebox crafty machine where we showcased the exploitation of a vulnerable minecraft server to log4j vulnerability using a log4shell payload.

Exploit Javamaliciousinboundsocket And Minecraft Server Exploit Hello, i'm running a small, white listed minecraft server from my own computer, and today, i got two notifications from malwarebytes about a blocked inbound connection through the port that the server uses. Earlier today, we identified a vulnerability in the form of an exploit within log4j – a common java logging library. this exploit affects many services – including minecraft java edition. The exploitation was frighteningly simple. an attacker could input a malicious jndi string into any application field that gets logged—a username field, a search box, even a minecraft chat message—and execute remote code on the target system. I decided to leverage the two years old vulnerability cve 2021 44228 (a.k.a log4shell) in java log4j library. this library is also part of the minecraft java edition. it is very easy to exploit the vulnerability, as we will see later during this blog post.

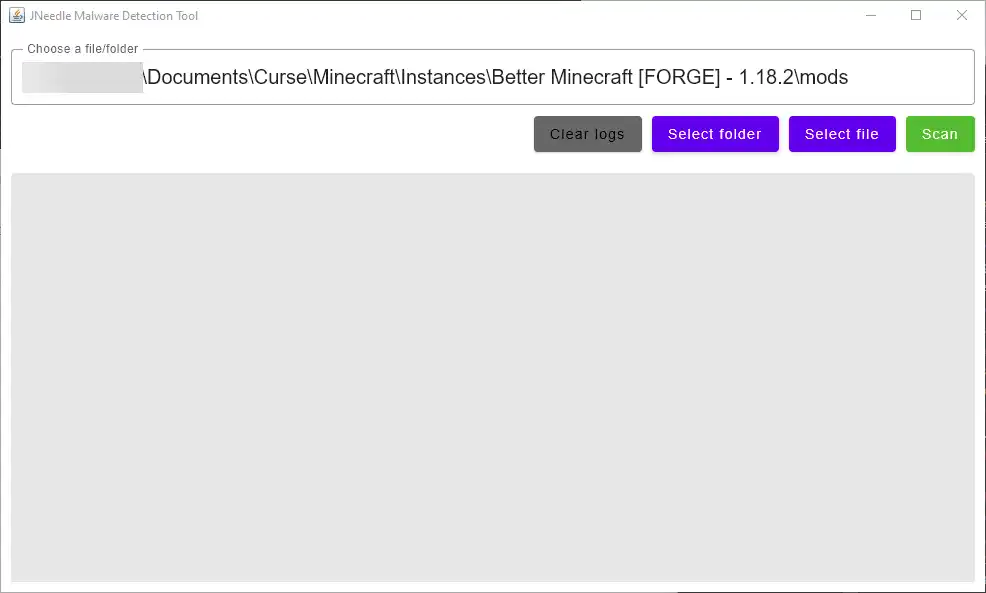
Solved Sometimes Blocking Java Exploit Code In Minecraft Anti The exploitation was frighteningly simple. an attacker could input a malicious jndi string into any application field that gets logged—a username field, a search box, even a minecraft chat message—and execute remote code on the target system. I decided to leverage the two years old vulnerability cve 2021 44228 (a.k.a log4shell) in java log4j library. this library is also part of the minecraft java edition. it is very easy to exploit the vulnerability, as we will see later during this blog post. Exploit.javamaliciousinboundsocket is malwarebytes’ detection name for remote shell exploits with payloads relying on inbound sockets. I want to make this thread a list of all ways to help fixing that new log4j zero day exploit that minecraft seems to have now. Using a vulnerable version of java and a minecraft server jar, we can show how log4j can be exploited with ease. there are plenty of online resources for how this can be done because of just how big this vulnerability was and somewhat still is. In the context of minecraft servers, attackers exploited this vulnerability to inject malicious code into servers, allowing them to gain unauthorized access, steal sensitive data, or disrupt.

Exploit Javamaliciousinboundsocket When Trying To Use A Localhost Exploit.javamaliciousinboundsocket is malwarebytes’ detection name for remote shell exploits with payloads relying on inbound sockets. I want to make this thread a list of all ways to help fixing that new log4j zero day exploit that minecraft seems to have now. Using a vulnerable version of java and a minecraft server jar, we can show how log4j can be exploited with ease. there are plenty of online resources for how this can be done because of just how big this vulnerability was and somewhat still is. In the context of minecraft servers, attackers exploited this vulnerability to inject malicious code into servers, allowing them to gain unauthorized access, steal sensitive data, or disrupt.
How To Protect Your Modded Minecraft Client Server From The Bleeding Using a vulnerable version of java and a minecraft server jar, we can show how log4j can be exploited with ease. there are plenty of online resources for how this can be done because of just how big this vulnerability was and somewhat still is. In the context of minecraft servers, attackers exploited this vulnerability to inject malicious code into servers, allowing them to gain unauthorized access, steal sensitive data, or disrupt.
Comments are closed.