Explain Attack Simulation In Akamai Api Security
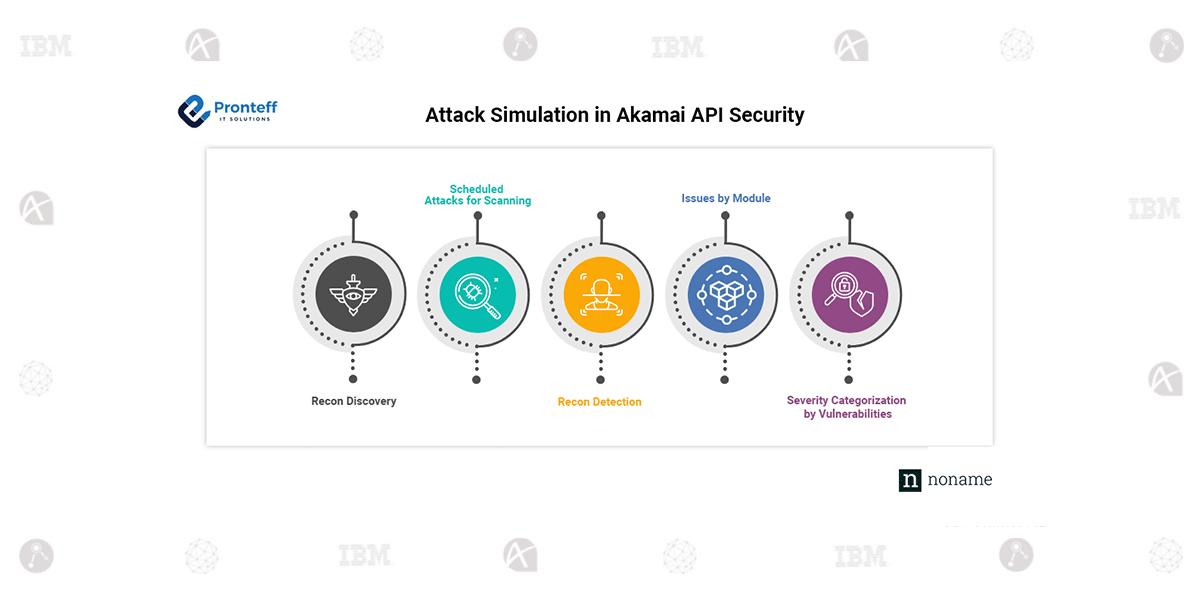
Explain Attack Simulation In Akamai Api Security Api security is crucial for businesses today, and akamai’s api security functionality offers an effective way to identify and resolve vulnerabilities. by simulating real world attacks on domains, it helps organizations detect issues and implement solutions to enhance their api security. Api attacks are growing and evolving fast, often in ways your web application and api protection may not detect. and without a comprehensive inventory of your apis, your team will have a blind spot and your organizations’ apis will be unprotected.
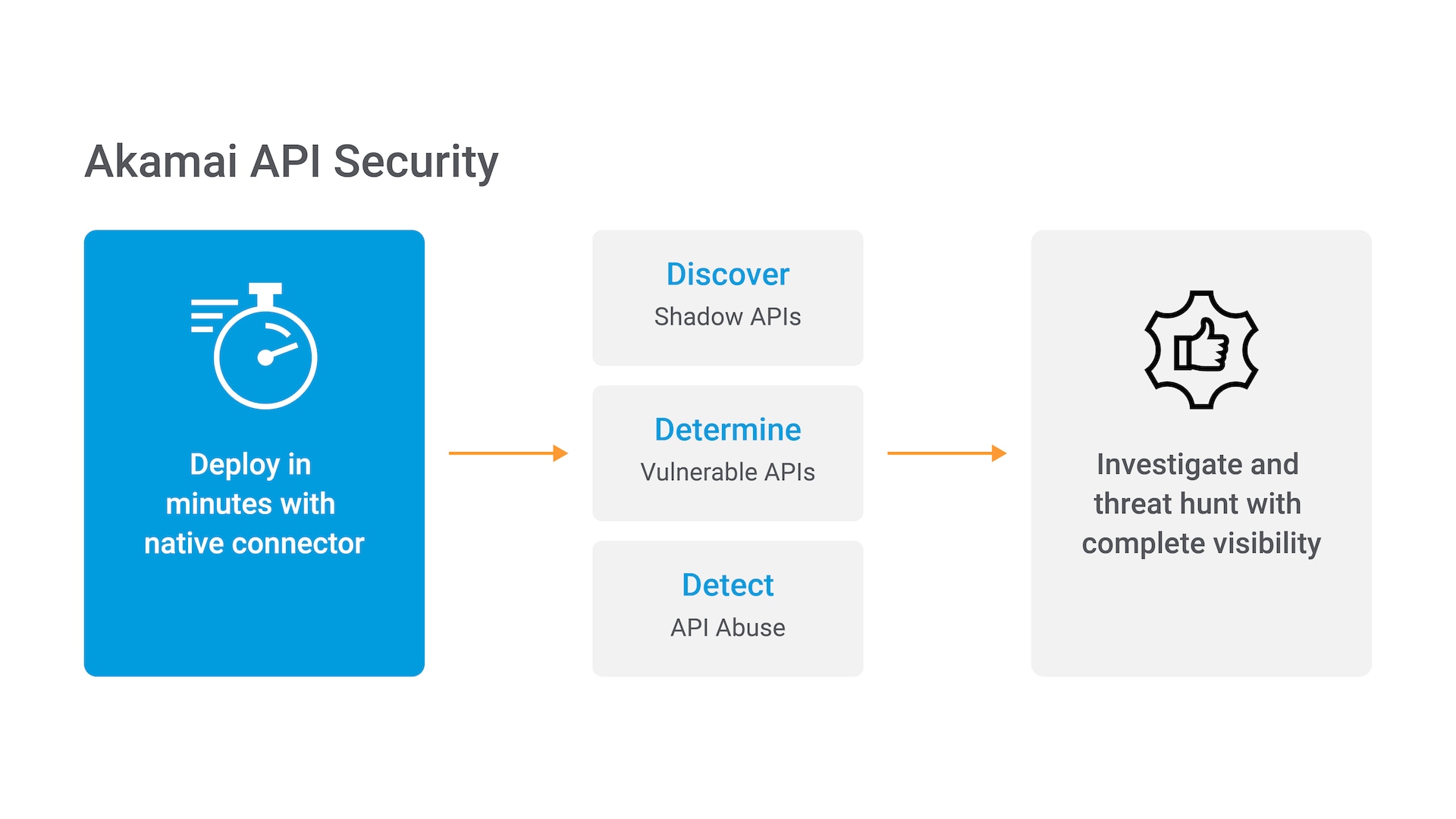
Api Security Akamai By mapping adversary tactics to api specific behaviors, security teams can enhance incident response and threat detection by identifying attack stages and associated tactics, techniques, and procedures. Legitimate consumers and malicious actors access apis through the akamai intelligent edge platform. edge servers automatically drop network layer ddos attacks and protect the application layer from ddos and application attacks. By integrating an api security solution with your existing security stack (e.g., waf or waap), you’ll be able to spot high risk behavior and block suspicious traffic before it can access. Once an api has been authorized by a web application and api protection (waap) product, security teams have no visibility into its use within the organization. malicious actors are aware of this gap, and they have shifted to abusing the vast api attack surface of the vulnerabilities that are present within organizations.
.png)
Akamai App Api Protector By integrating an api security solution with your existing security stack (e.g., waf or waap), you’ll be able to spot high risk behavior and block suspicious traffic before it can access. Once an api has been authorized by a web application and api protection (waap) product, security teams have no visibility into its use within the organization. malicious actors are aware of this gap, and they have shifted to abusing the vast api attack surface of the vulnerabilities that are present within organizations. As apis become more pervasive, attacks like bola (broken object level authorization) and mass assignment exploits will rise. ai driven api security tools will emerge to detect anomalies in real time. Let's delve deeper into these upgrades and explore how they strengthen application security for businesses. the improved layer 7 ddos protections precisely detect and counter short attack bursts, while incorporating client reputation scores for more effective rate limiting. The enhanced layer 7 ddos protections now precisely detect and mitigate short ddos attack bursts and use client reputation scores for improved rate limiting. Cloud security vendor akamai has announced the release of api security, a product built to stop application programming interface (api) attacks and detect business logic abuse inside.

Akamai Unraveling The Complexity Of Api Security And Observability In As apis become more pervasive, attacks like bola (broken object level authorization) and mass assignment exploits will rise. ai driven api security tools will emerge to detect anomalies in real time. Let's delve deeper into these upgrades and explore how they strengthen application security for businesses. the improved layer 7 ddos protections precisely detect and counter short attack bursts, while incorporating client reputation scores for more effective rate limiting. The enhanced layer 7 ddos protections now precisely detect and mitigate short ddos attack bursts and use client reputation scores for improved rate limiting. Cloud security vendor akamai has announced the release of api security, a product built to stop application programming interface (api) attacks and detect business logic abuse inside.
Comments are closed.