Every Hacking Technique Explained As Fast As Possible

Hacking Techniques Pdf Computing System Software Each technique is explained with real world examples so you can understand how hackers operate and how to protect yourself from these attacks. by the end of this video, you’ll have a solid. In this video, we explore the top 40 hacking techniques that are essential for anyone interested in cybersecurity. whether you're a beginner or a seasoned it professional, understanding these.

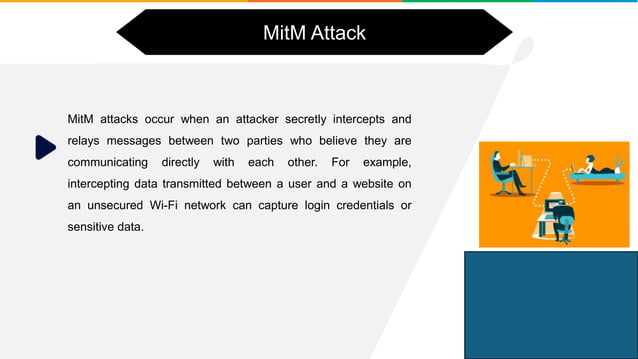
Gabriel Herrera On Linkedin Every Hacking Technique Explained In 4 Minutes In this video, we're exposing the most powerful hacking techniques that will blow your mind. from penetration testing to password cracking, we're covering it all in just minutes. The video "every hacking technique explained as fast as possible!" outlines 40 different hacking techniques, focusing on ethical hacking and security practices. it emphasizes the importance of understanding these techniques to better protect against potential threats. Every hacking technique explained as fast as possible 20 hacking techniques explained fast! secret tools unlock your potential with our latest video, "20 hacks broken down! top. Every hacking technique — explained at lightning speed. from phishing, sql injection, buffer overflows, ddos, password cracking, social engineering, privilege escalation, wifi attacks,.
Top 10 Common Hacking Techniques You Should Know About Pdf Pdf Every hacking technique explained as fast as possible 20 hacking techniques explained fast! secret tools unlock your potential with our latest video, "20 hacks broken down! top. Every hacking technique — explained at lightning speed. from phishing, sql injection, buffer overflows, ddos, password cracking, social engineering, privilege escalation, wifi attacks,. Every hacking method explained in 11 minutes this fast paced, informative guide covers the most common and dangerous hacking techniques used by cybercriminals today. In this video, we break down every major hacking technique in under 10 minutes, including phishing, social engineering, keyloggers, ransomware, malware, brute force attacks, and more. Here are some common techniques used by hackers that you should know to protect yourself from being hacked or at least use some preventive measures. not all hackers are bad. hackers are usually grouped by their intentions and the way they use their skills. here are the most common types:. This tutorial spans various subjects, including comprehension of the ethical hacking process, along with practical applications using cutting edge hacking tools and methodologies.

40 Hacking Techniques Explained Tools And Examples For Ethical Hackers Every hacking method explained in 11 minutes this fast paced, informative guide covers the most common and dangerous hacking techniques used by cybercriminals today. In this video, we break down every major hacking technique in under 10 minutes, including phishing, social engineering, keyloggers, ransomware, malware, brute force attacks, and more. Here are some common techniques used by hackers that you should know to protect yourself from being hacked or at least use some preventive measures. not all hackers are bad. hackers are usually grouped by their intentions and the way they use their skills. here are the most common types:. This tutorial spans various subjects, including comprehension of the ethical hacking process, along with practical applications using cutting edge hacking tools and methodologies.
Top 10 Hacking Techniques Explained In 10 Minutes Ethical Hacking Here are some common techniques used by hackers that you should know to protect yourself from being hacked or at least use some preventive measures. not all hackers are bad. hackers are usually grouped by their intentions and the way they use their skills. here are the most common types:. This tutorial spans various subjects, including comprehension of the ethical hacking process, along with practical applications using cutting edge hacking tools and methodologies.
Comments are closed.