Essential Eight Cybersecurity Alignment Smile It
Essential Eight Cybersecurity Alignment Smile It Smile it is here to assess your essential eight compliance and guide you to an improved cybersecurity posture. get in touch using the form below and let’s get started!. The most effective of these mitigation strategies are the essential eight. the essential eight has been designed to protect organisations’ internet connected information technology networks.

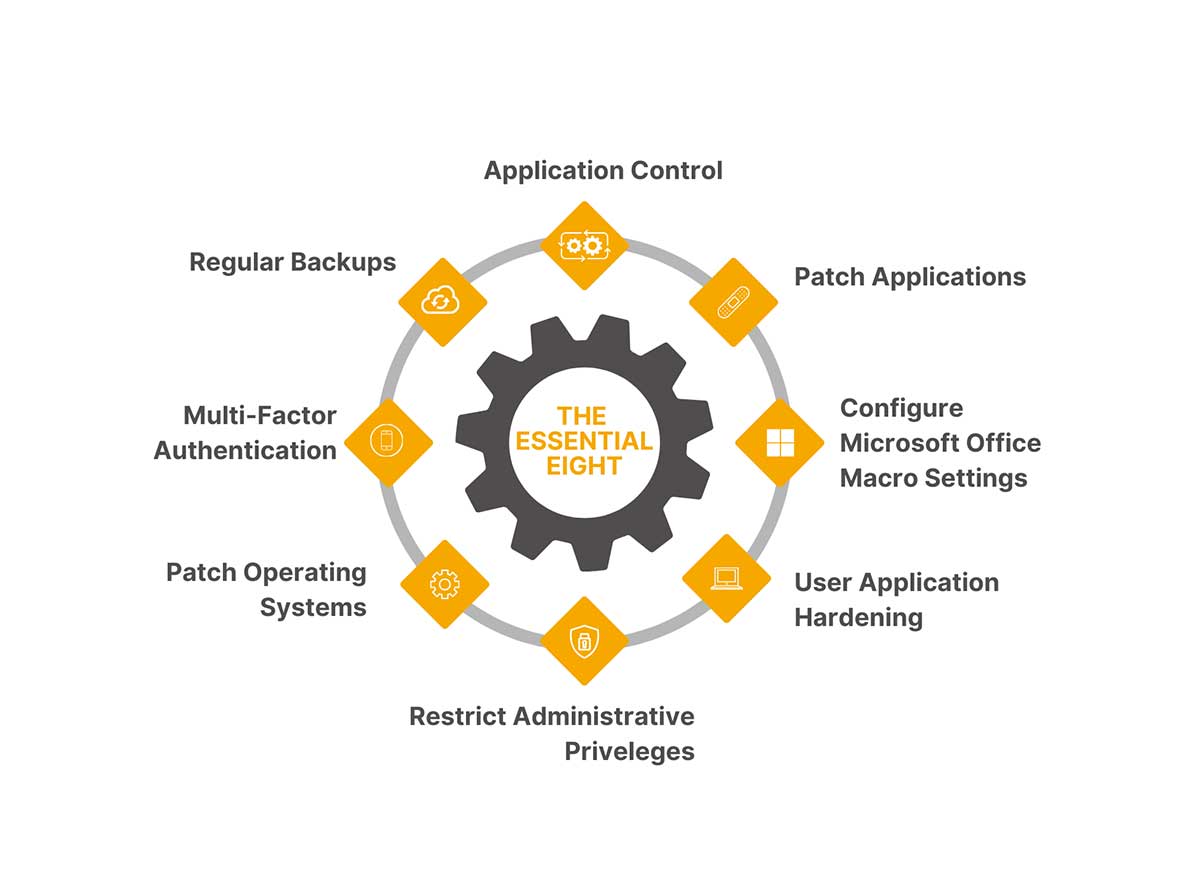
Essential Eight Cybersecurity Alignment Smile It The mandatory requirements aligned to the essential eight maturity level 1 in the nsw cyber security policy are mapped to the controls taken from the december 2024 release of the information security manual (ism). The essential eight is a set of eight prioritized cyber security mitigation strategies developed by the australian cyber security centre (acsc). it provides a baseline framework to protect against common cyber threats such as ransomware, phishing, and data breaches. Learn how cios and ctos can implement the essential eight cybersecurity framework. step by step guide, maturity levels, compliance, and faqs. The acsc developed the essential eight to give australian businesses a clear, practical baseline for defending against the most common cyber threats. its purpose is to reduce exposure to attacks and provide a measurable maturity model that aligns with government security requirements.

Essential Eight Cybersecurity Alignment Smile It Learn how cios and ctos can implement the essential eight cybersecurity framework. step by step guide, maturity levels, compliance, and faqs. The acsc developed the essential eight to give australian businesses a clear, practical baseline for defending against the most common cyber threats. its purpose is to reduce exposure to attacks and provide a measurable maturity model that aligns with government security requirements. Designed to provide an overview of where your business stands with regards to the essential eight, it's completely free to use. Clarify maturity and uplift pathways — learn how maturity levels work and how to plan incremental improvement over time. reduce ambiguity for stakeholders — use plain language explanations that help align it, security, leadership, and audit requirements. Improve your organisation’s cyber security posture by adopting the essential eight series of mitigations, as outlined in this guide. ready to get started? find out how cybercx can help your organisation manage risk, respond to incidents and build cyber resilience. The acsc essential 8 cybersecurity model is a comprehensive guide to help organizations improve their cybersecurity posture. here is the full guide.

The Importance Of The Essential Eight For Cybersecurity In Australia Designed to provide an overview of where your business stands with regards to the essential eight, it's completely free to use. Clarify maturity and uplift pathways — learn how maturity levels work and how to plan incremental improvement over time. reduce ambiguity for stakeholders — use plain language explanations that help align it, security, leadership, and audit requirements. Improve your organisation’s cyber security posture by adopting the essential eight series of mitigations, as outlined in this guide. ready to get started? find out how cybercx can help your organisation manage risk, respond to incidents and build cyber resilience. The acsc essential 8 cybersecurity model is a comprehensive guide to help organizations improve their cybersecurity posture. here is the full guide.
Comments are closed.