Enhancing Remote Access Security Controls A Comprehensive Guide

Enhancing Remote Access Security Controls A Comprehensive Guide By Implementing effective remote access security controls is vital to safeguarding your organization’s sensitive data and network infrastructure. by understanding the key components and adopting best practices, you can significantly reduce the risk of unauthorized access and potential data breaches. This article explores the importance of robust remote access security controls and how they can protect your organization from cyber threats.
Remote Access Security Essential Strategies To Protect Data Implementing effective remote access security controls is vital to safeguarding your organization’s sensitive data and network infrastructure. by understanding the key components and. This article explores the importance of robust remote access security controls and how they can protect your organization from cyber threats. Learn remote access security best practices for vpn, ssh, and rdp hardening. protect your distributed workforce from credential based attacks. learn more. Explore the world of remote access control systems, their benefits, features, and key considerations for implementation.
The Essential Guide To Securing Remote Access Duo Security Learn remote access security best practices for vpn, ssh, and rdp hardening. protect your distributed workforce from credential based attacks. learn more. Explore the world of remote access control systems, their benefits, features, and key considerations for implementation. Data on securing remote access below are five tables providing data related to securing remote access, including adoption rates, effectiveness, challenges, and best practices. This remote access control systems guide will provide insights into the evolving nature of remote access solutions, including their implementation, benefits, and best practices in security management. Secure remote access best practices fall into several broad categories: authentication and access controls, device and network security, data protection and monitoring, user training and audits. Remote access security with strong authentication, zero trust, and encryption. learn best practices to protect users, devices, and data from cyber threats.

Infographic Secure Remote Access Data on securing remote access below are five tables providing data related to securing remote access, including adoption rates, effectiveness, challenges, and best practices. This remote access control systems guide will provide insights into the evolving nature of remote access solutions, including their implementation, benefits, and best practices in security management. Secure remote access best practices fall into several broad categories: authentication and access controls, device and network security, data protection and monitoring, user training and audits. Remote access security with strong authentication, zero trust, and encryption. learn best practices to protect users, devices, and data from cyber threats.
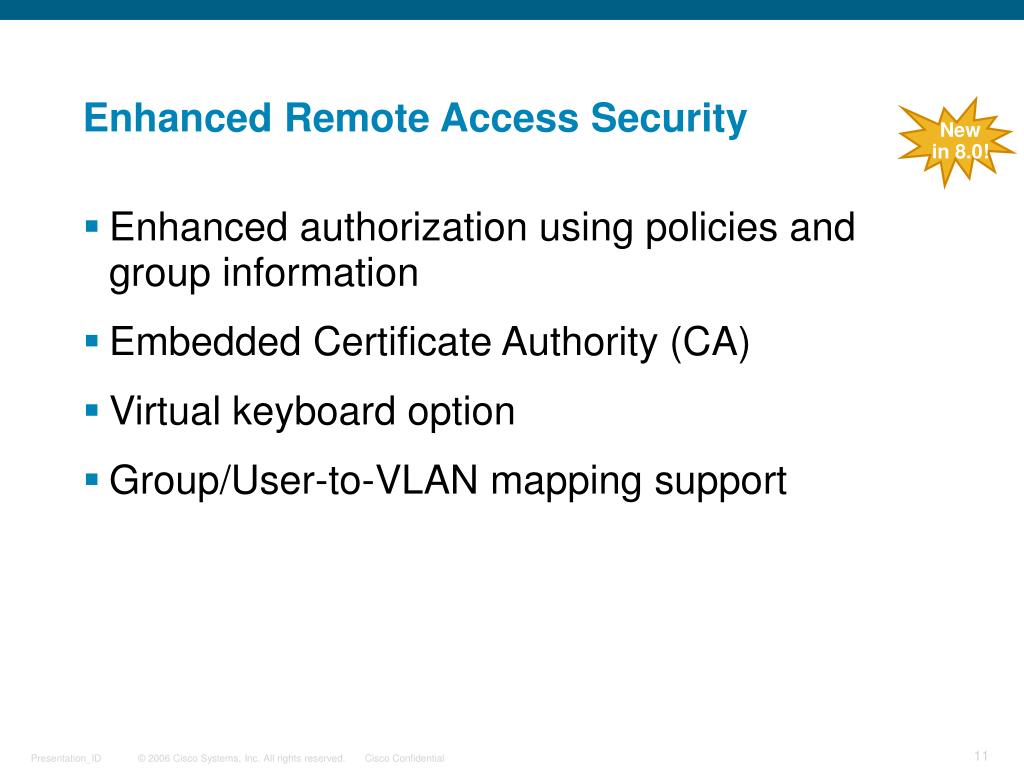
Ppt Virtual Private Networks Powerpoint Presentation Free Download Secure remote access best practices fall into several broad categories: authentication and access controls, device and network security, data protection and monitoring, user training and audits. Remote access security with strong authentication, zero trust, and encryption. learn best practices to protect users, devices, and data from cyber threats.

Don T Be A Target Your 2024 Guide To Locking Down Remote Access Security
Comments are closed.