Encryption Lesson Pdf Cipher Cryptography

Lesson 6 Cryptography Pdf Cryptography Public Key Cryptography Convention: alicekazam is sending encrypted messages to bobasaur, bobasaur is decrypting them, and eevee is an eavesdropper who overhears everything being sent, but hopefully still can’t understand it. an encryption method together with a decryption method is known as a cryptographic scheme. This page contains a selection of downloadable resources for teaching using cryptography.
Cryptography 2 Pdf Cryptography Cipher Cipher achieves perfect secrecy if and only if there are as many possible keys as possible plaintexts, and every key is equally likely (claude shannon’s result). The national bureau of standards (nbs) (now called nist, the national institute of standards and technology) put out a call for a modern, public encryption algorithm. In today's lecture, we will explore how cryptography motivates solutions to the security concerns we discussed in monday's lecture. to do so, we will discuss: cryptography is the study of secure communication techniques in the presence of an adversary. others from understanding that same message. The purpose of this module is to provide students an introduction into the world of cryptography through the caesar cipher and to help students understand how cryptography is used in computer science.
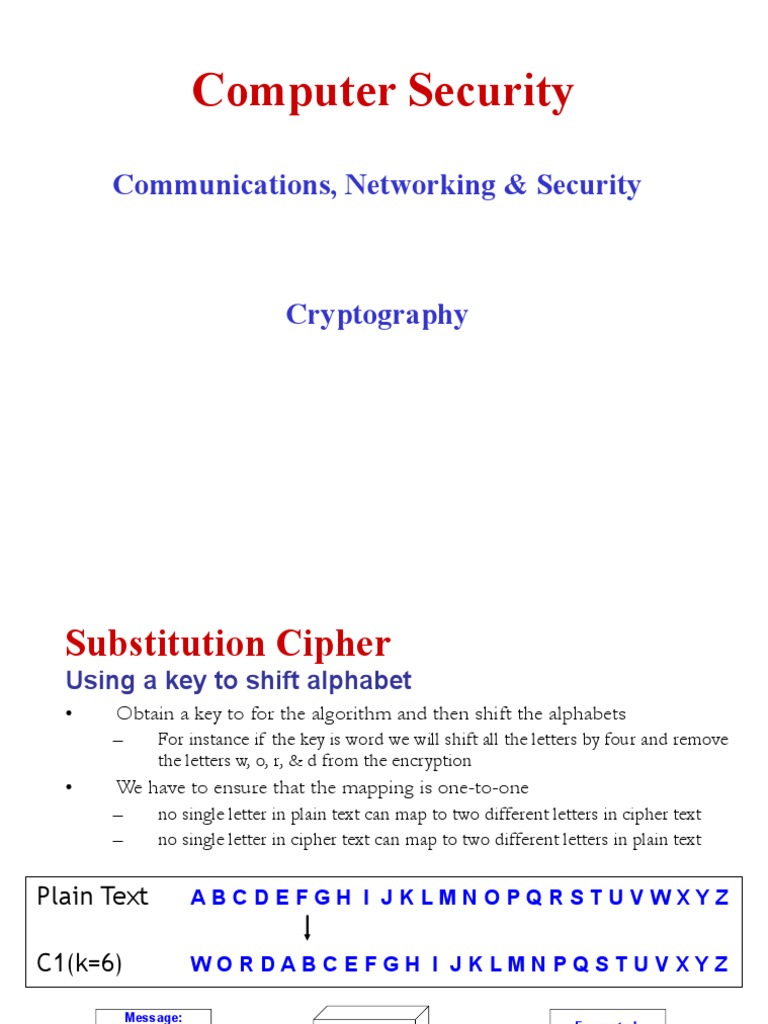
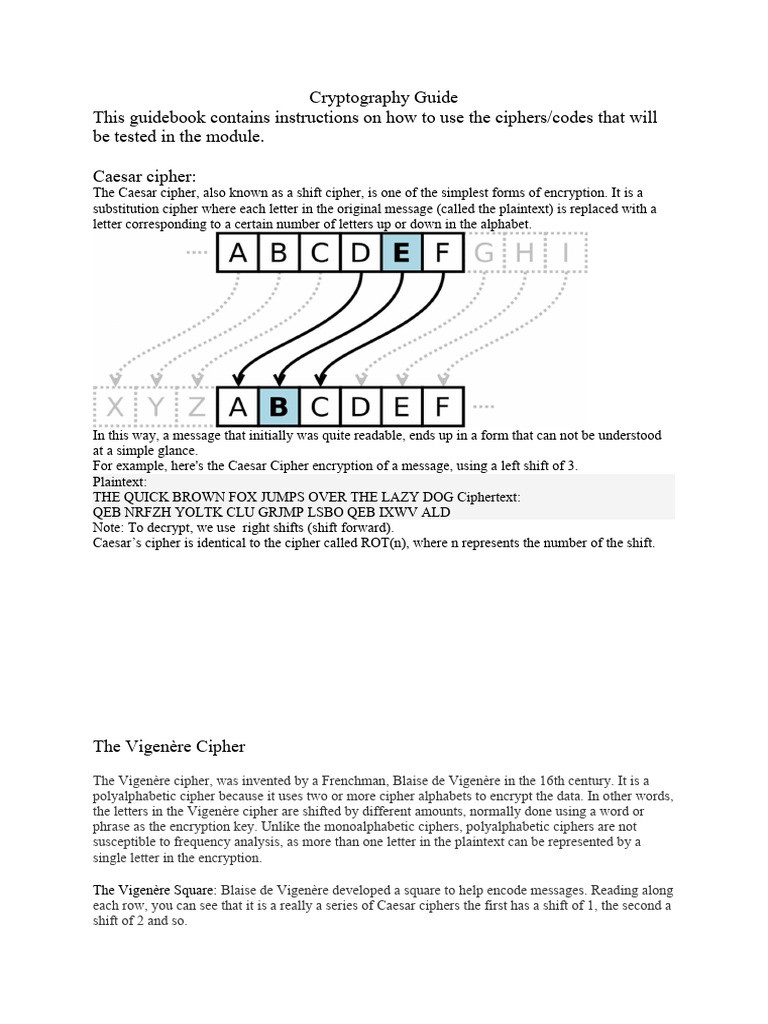
Lecture 2 Cryptography Pdf Cryptography Key Cryptography In today's lecture, we will explore how cryptography motivates solutions to the security concerns we discussed in monday's lecture. to do so, we will discuss: cryptography is the study of secure communication techniques in the presence of an adversary. others from understanding that same message. The purpose of this module is to provide students an introduction into the world of cryptography through the caesar cipher and to help students understand how cryptography is used in computer science. While encryption is probably the most prominent example of a crypto graphic problem, modern cryptography is much more than that. in this class, we will learn about pseudorandom number generators, digital signatures, zero knowledge proofs, multi party computation, to name just a few examples. Polyalphabetic cipher is a substitution cipher in which the cipher alphabet for the plain alphabet may be different at different places during the encryption process. Also known as secret key cryptography or conventional cryptography, symmetric key cryptography is an encryption system in which the sender and receiver of a message share a single, common key that is used to encrypt and decrypt the message. Cryptography and free speech: the cryptography involve not just products, it involves ideas too, although governments effectively control the flow of products across borders, controlling the floe ideas either head or on the internet, is also impossible.

Lecture 1 1 Introduction Cryptography Updated Pdf Cryptography While encryption is probably the most prominent example of a crypto graphic problem, modern cryptography is much more than that. in this class, we will learn about pseudorandom number generators, digital signatures, zero knowledge proofs, multi party computation, to name just a few examples. Polyalphabetic cipher is a substitution cipher in which the cipher alphabet for the plain alphabet may be different at different places during the encryption process. Also known as secret key cryptography or conventional cryptography, symmetric key cryptography is an encryption system in which the sender and receiver of a message share a single, common key that is used to encrypt and decrypt the message. Cryptography and free speech: the cryptography involve not just products, it involves ideas too, although governments effectively control the flow of products across borders, controlling the floe ideas either head or on the internet, is also impossible.

Encryption Lesson Pdf Cipher Cryptography Also known as secret key cryptography or conventional cryptography, symmetric key cryptography is an encryption system in which the sender and receiver of a message share a single, common key that is used to encrypt and decrypt the message. Cryptography and free speech: the cryptography involve not just products, it involves ideas too, although governments effectively control the flow of products across borders, controlling the floe ideas either head or on the internet, is also impossible.
Cryptography Guide Pdf Cipher Cryptography
Comments are closed.