Encryption Cybersec 101 Medium
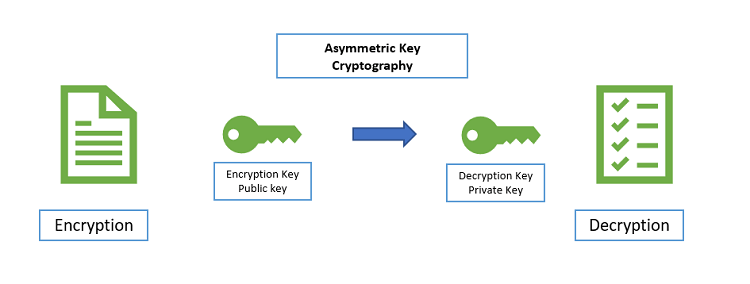
Encryption Cybersec 101 Medium Read writing about encryption in cybersec 101. this publication is for complete beginners who are starting out in the field of information security and are passionate about it. This article outlines the complete guide on encryption suited to businesses and organizations: it includes basic principles, mechanisms, and types of encryption that would play a credible role in the provision of cybersecurity.
Encryption 101 The Story Of Hiding Message In Plain By Kittiphat This cryptography cheat sheet provides a structured overview of modern cryptographic concepts, algorithms, protocols, and best practices for 2025. it is designed for developers, security professionals, and enthusiasts to quickly reference important information. Cryptography is fundamental to the confidentiality and integrity of applications and systems. the owasp cheat sheet series describes the use of cryptography and some of these are listed in the further reading at the end of this section. Learn everything you need to embark on a career path in offensive or defensive cyber security. prove your core cyber security skills and build the foundation for a career in cyber. this beginner friendly path aims to give a solid introduction to the different areas in computer security. Learn how cryptography powers authentication mechanisms to verify the authenticity of users and systems. this lecture provides a foundational understanding of cryptography, focusing on its purpose and importance in securing information.
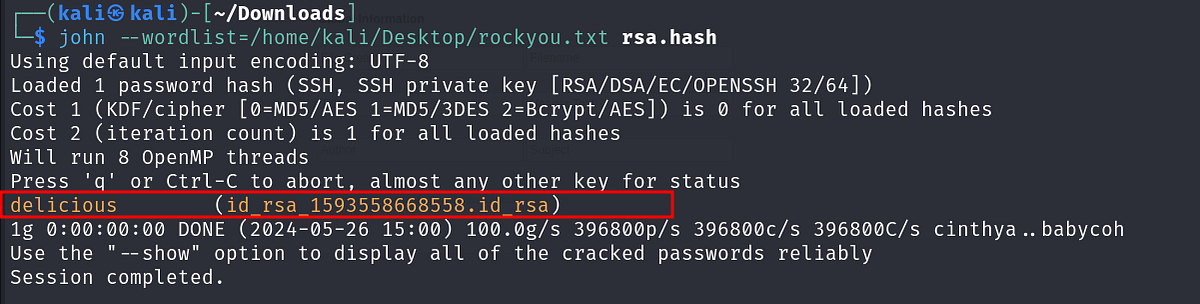
Encryption Crypto 101 Crypto Cryptography Ensures That Data By Learn everything you need to embark on a career path in offensive or defensive cyber security. prove your core cyber security skills and build the foundation for a career in cyber. this beginner friendly path aims to give a solid introduction to the different areas in computer security. Learn how cryptography powers authentication mechanisms to verify the authenticity of users and systems. this lecture provides a foundational understanding of cryptography, focusing on its purpose and importance in securing information. Learn how cryptography in cybersecurity protects data, secures communication, and ensures privacy. explore its types, techniques, and real world applications. Hackthebox interactive cybersecurity platform with diverse challenges for hands on practice, covering areas like penetration testing, reverse engineering, and cryptography. Master cryptographic hashing: how md5, sha 1, sha 256, sha 384, sha 512 work, when to use each, hmac authentication, output formats, and real security guidance. A collection of various awesome lists for hackers, pentesters and security researchers.

Tryhackme Encryption Crypto 101 By Temidayo Adejumo Medium Learn how cryptography in cybersecurity protects data, secures communication, and ensures privacy. explore its types, techniques, and real world applications. Hackthebox interactive cybersecurity platform with diverse challenges for hands on practice, covering areas like penetration testing, reverse engineering, and cryptography. Master cryptographic hashing: how md5, sha 1, sha 256, sha 384, sha 512 work, when to use each, hmac authentication, output formats, and real security guidance. A collection of various awesome lists for hackers, pentesters and security researchers.

Tryhackme Encryption Crypto 101 By Temidayo Adejumo Medium Master cryptographic hashing: how md5, sha 1, sha 256, sha 384, sha 512 work, when to use each, hmac authentication, output formats, and real security guidance. A collection of various awesome lists for hackers, pentesters and security researchers.

Tryhackme Encryption Crypto 101 By Temidayo Adejumo Medium
Comments are closed.