Encryption And Decryption Images
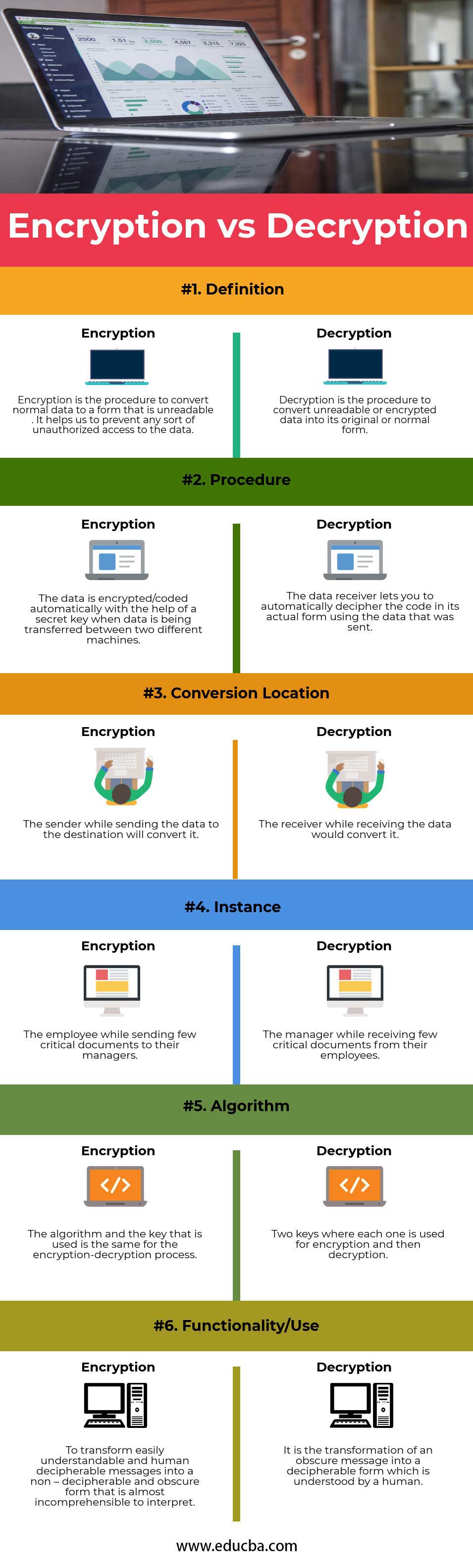
Encryption Vs Decryption A Comprehensive Comparison A free online tool to encrypt and decrypt images securely. protect your images with advanced and authenticated encryption techniques. Free online tool to encrypt and decrypt images using 7 encryption algorithms (aes 256 gcm, aes cbc, chacha20, 3des). supports png, jpeg, gif, webp. 100% browser based no uploads.
Symmetric Encryption Decryption Stable Diffusion Online Once image content is encrypted, it no longer contains meaningful information, and each image sounds almost identical until its decryption. these images are at risk of being intercepted by attackers after their decryption, which may lead to copyright violations and the misuse of the original content. In this article, we will encrypt decrypt an image using simple mathematical logic. it requires two things, data, and key, and when xor operation is applied on both the operands i.e data and key, the data gets encrypted but when the same process is done again with the same key value data gets decrypted. This project is a command line tool designed for secure encryption and decryption of image files using aes and rsa algorithms. it provides a menu driven interface that enables users to list images, encrypt and decrypt images, and view rsa key pairs. Image encryption algorithms aim to ensure the security of the image from unauthorized access by encrypting the plaintext image and producing a cipher image that can only be decrypted by the intended users.
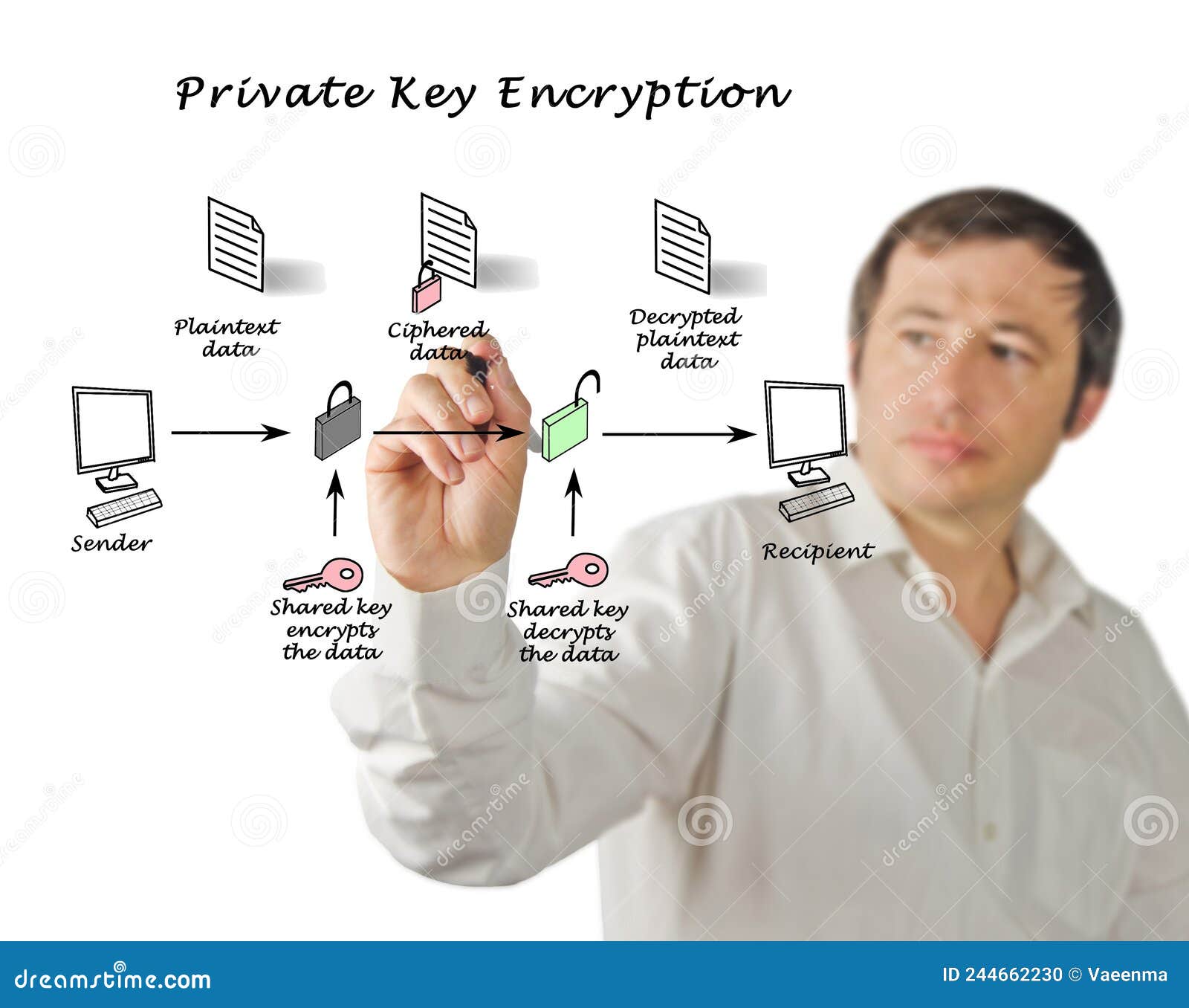
Free Text Encryption And Decryption Tool Easy To Use This project is a command line tool designed for secure encryption and decryption of image files using aes and rsa algorithms. it provides a menu driven interface that enables users to list images, encrypt and decrypt images, and view rsa key pairs. Image encryption algorithms aim to ensure the security of the image from unauthorized access by encrypting the plaintext image and producing a cipher image that can only be decrypted by the intended users. In recent years, many image encryption approaches are designed by the researchers. they use different concepts for image encryption to increase security. the main aim of this paper is to present a comprehensive review of the existing image encryption approaches. The system proposed in this project employs aes to encrypt and decrypt both text and image files, ensuring confidentiality and integrity during transmission. Unlike text data, images have high redundancy and strong spatial correlation, posing unique challenges for traditional cryptographic systems. this paper aims to provide a detailed review of image encryption and decryption methods, with emphasis on performance, security, and applicability. We begin by providing a background on image encryption, highlighting its importance in safeguarding image data from unauthorized access and tampering. we discuss symmetric, asymmetric, and hybrid encryption techniques, analyzing their suitability for different scenarios.

Encryption And Decryption Principles Stable Diffusion Online In recent years, many image encryption approaches are designed by the researchers. they use different concepts for image encryption to increase security. the main aim of this paper is to present a comprehensive review of the existing image encryption approaches. The system proposed in this project employs aes to encrypt and decrypt both text and image files, ensuring confidentiality and integrity during transmission. Unlike text data, images have high redundancy and strong spatial correlation, posing unique challenges for traditional cryptographic systems. this paper aims to provide a detailed review of image encryption and decryption methods, with emphasis on performance, security, and applicability. We begin by providing a background on image encryption, highlighting its importance in safeguarding image data from unauthorized access and tampering. we discuss symmetric, asymmetric, and hybrid encryption techniques, analyzing their suitability for different scenarios.

Encryption And Decryption Download Scientific Diagram Unlike text data, images have high redundancy and strong spatial correlation, posing unique challenges for traditional cryptographic systems. this paper aims to provide a detailed review of image encryption and decryption methods, with emphasis on performance, security, and applicability. We begin by providing a background on image encryption, highlighting its importance in safeguarding image data from unauthorized access and tampering. we discuss symmetric, asymmetric, and hybrid encryption techniques, analyzing their suitability for different scenarios.
Public Key Encryption And Decryption Stock Photography Cartoondealer
Comments are closed.