Encrypt And Decrypt Password Using C
Encrypt And Decrypt Password Using C Our goal is to encrypt the contents of the file named original.txt by using the key character in the key.txt file and then to decrypt the password and make it original. A tiny (>90 semicolons of c!) cli tool for password authenticated encryption decryption of files using libsodium; written in pure c. schjmann19 ezcrpyt.
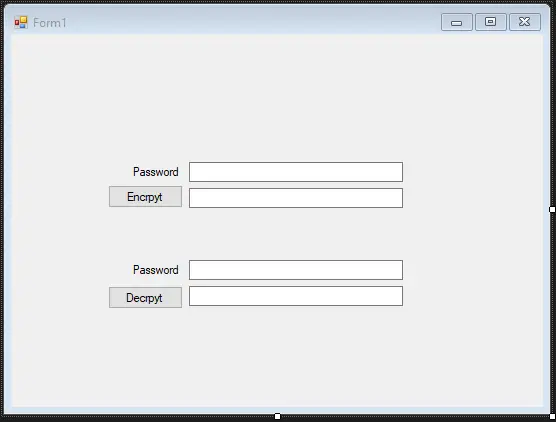
Encrypt And Decrypt Password Using C In this article, you will learn and get code about how to encrypt or decrypt a file using the c programming language. but before going through the program of encryption and decryption, let's first understand what it actually means when encrypting or decrypting a file. In this article i will explain with an example, how to encrypt and store username or password in sql server database table and then fetch, decrypt and display it in windows forms (winforms) application using c# and vb . Write a c program to encryption and decryption of password. in this program we encrypt the given string by subtracting the hex value from it. password encryption is required for the security reason, you can use so many functions like hash or other keys to encrypt. In this article, symmetric cryptography is used to encrypt and decrypt data. approach: let's discuss the approach in detail before proceeding to the implementation part:.
Encrypt And Decrypt Password Using C Write a c program to encryption and decryption of password. in this program we encrypt the given string by subtracting the hex value from it. password encryption is required for the security reason, you can use so many functions like hash or other keys to encrypt. In this article, symmetric cryptography is used to encrypt and decrypt data. approach: let's discuss the approach in detail before proceeding to the implementation part:. While gnupg can encrypt decrypt with key pairs, the symmetric or c command line option makes it encrypt decrypt with a password or passphrase (specified with the passphrase or passphrase fd or passphrase file option). Learn how to securely encrypt passwords using sha 256 in c# and . this step by step guide ensures your application's password hashing meets modern security standards. Encrypt and decrypt text or files using aes (advanced encryption standard) with support for 128, 192, and 256‑bit keys. choose from cbc, ecb, and gcm modes, generate random ivs, and secure your sensitive data. perfect for developers, security professionals, and anyone needing strong symmetric encryption. The recipient option is used once for each recipient and takes an extra argument specifying the public key to which the document should be encrypted. the encrypted document can only be decrypted by someone with a private key that complements one of the recipients' public keys.
Encrypt And Decrypt Password Using C While gnupg can encrypt decrypt with key pairs, the symmetric or c command line option makes it encrypt decrypt with a password or passphrase (specified with the passphrase or passphrase fd or passphrase file option). Learn how to securely encrypt passwords using sha 256 in c# and . this step by step guide ensures your application's password hashing meets modern security standards. Encrypt and decrypt text or files using aes (advanced encryption standard) with support for 128, 192, and 256‑bit keys. choose from cbc, ecb, and gcm modes, generate random ivs, and secure your sensitive data. perfect for developers, security professionals, and anyone needing strong symmetric encryption. The recipient option is used once for each recipient and takes an extra argument specifying the public key to which the document should be encrypted. the encrypted document can only be decrypted by someone with a private key that complements one of the recipients' public keys.
Comments are closed.