Embracing Gitops For Network Security Compliance

Embracing The Most Important Network Cybersecurity Shift In A This research explores the best practices and challenges in achieving security and compliance within gitops frameworks. This is where gitops and policy as code (pac) converge to redefine cloud governance — making security and compliance automated, versioned, and continuously enforced.
Applying Gitops Network Firewall P3 Explore security challenges in gitops and discover best practices for secure deployments, including rbac, policy enforcement, secret management, and monitoring, ensuring robust protection for scalable software delivery pipelines. By positioning gitops as a vital component of your security and compliance strategy, your organization can stay ahead of the curve and ensure robust, secure, and compliant infrastructure management in the dynamic world of the cloud. All the concepts like security policies, infrastructure as code, and container signing are sound, but the real challenge lies in convincing your colleagues to embrace these changes. This repository provides foundational practices to secure gitops environments, covering everything from access control to software provenance verification. explore the complete gitops security champion.

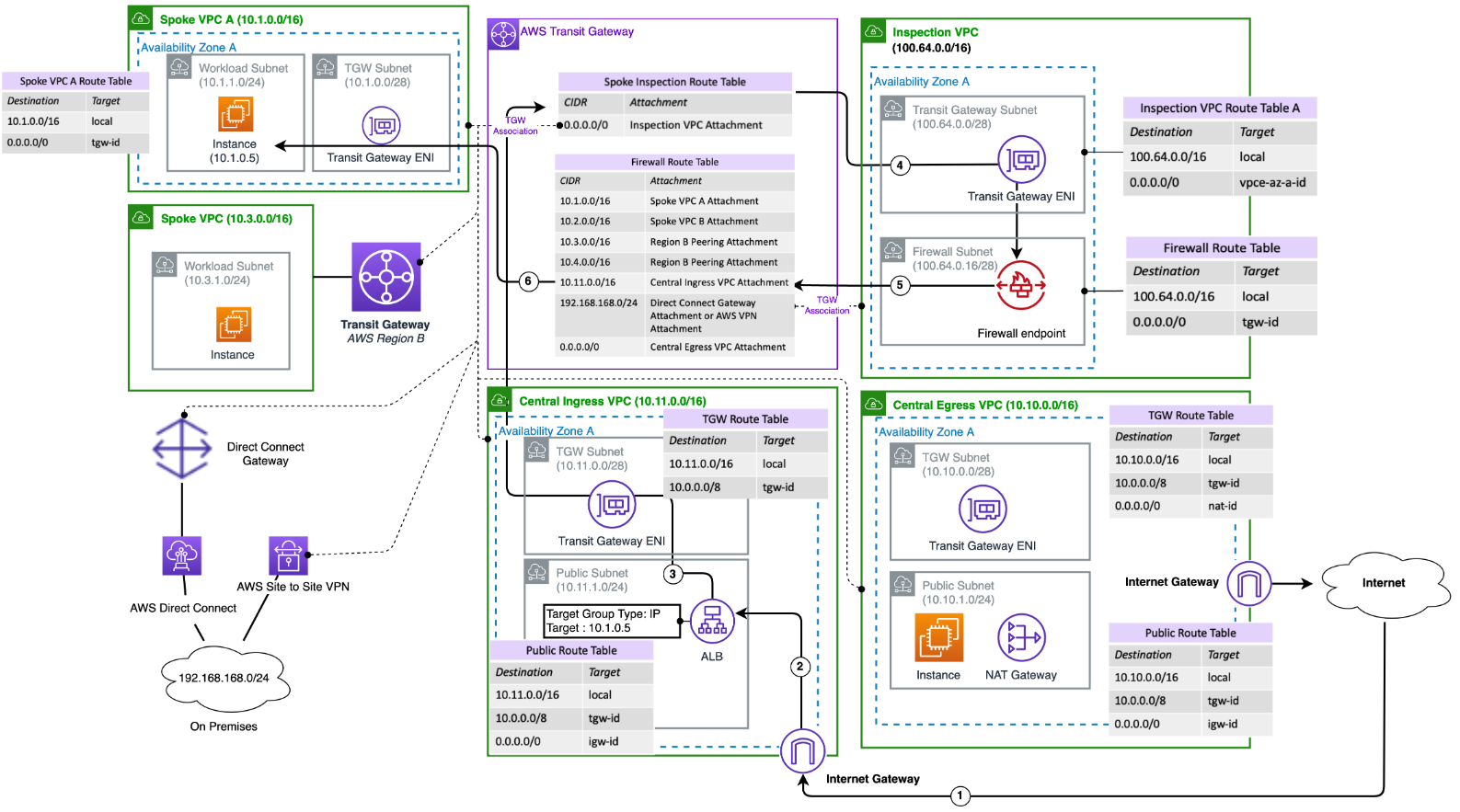
Unleashing The Power Of Gitops A Paradigm Shift In Network Security All the concepts like security policies, infrastructure as code, and container signing are sound, but the real challenge lies in convincing your colleagues to embrace these changes. This repository provides foundational practices to secure gitops environments, covering everything from access control to software provenance verification. explore the complete gitops security champion. Enhance your gitops security with this comprehensive checklist. learn best practices to protect your infrastructure and ensure a secure deployment pipeline. In this video we discuss how to embrace gitops for networking and security in the cloud. we show you the tools involved and demo a pipeline creation from start to finish. In a gitops world, the git repository is the source of truth, but the reconciliation loop is the enforcer. marcus ross highlighted how they use specialized tools to ensure that security policies aren’t just suggestions—they are immutable laws. The journey of scaling gitops in the enterprise is continuous, but with a strategic focus on secrets management, policy as code, and multi cluster strategies, organizations can build secure, resilient, and highly automated delivery platforms.
Comments are closed.