Dynamic Analysis Of Android Application Androidpentesting

Android Pentesting Dynamic Analysis While static analysis gives you a snapshot of an application’s code, dynamic analysis — especially through runtime manipulation — lets you observe live behavior, modify code on the fly, and. After injecting the script, the application will open automatically (even on rooted device) and you will be able to intercept the traffic in burpsuite. finally, you can test the application normally as you would test a web application by intercepting the requests and playing around them.
Android Pentesting Dynamic Analysis Dynamic analysis, also known as runtime analysis, examines how an android application behaves on a real or emulated device. it can uncover issues such as insecure data transfer, poor session management, and improper input validation. Want to see what android apps really do behind the scenes? 👀 in this video, i’ll guide you step by step to set up a dynamic analysis lab for android pentesting — perfect for beginners. Static and dynamic analysis: mobsf can perform both static and dynamic analysis of mobile applications, providing a comprehensive view of application security. the tool can analyze the source code of an application, as well as the runtime behaviour, to identify vulnerabilities and potential security threats. This checklist is intended as a starting point for penetration testers and bug bounty hunters to identify common security issues in android applications. it is not a comprehensive guide to all possible security issues and should be used in conjunction with other resources and best practices.

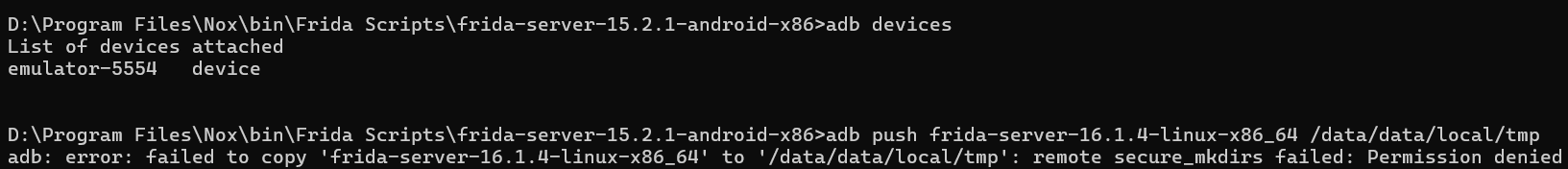
Introduction To Dynamic Analysis Of Android Application Pdf Static and dynamic analysis: mobsf can perform both static and dynamic analysis of mobile applications, providing a comprehensive view of application security. the tool can analyze the source code of an application, as well as the runtime behaviour, to identify vulnerabilities and potential security threats. This checklist is intended as a starting point for penetration testers and bug bounty hunters to identify common security issues in android applications. it is not a comprehensive guide to all possible security issues and should be used in conjunction with other resources and best practices. Several efforts have been made towards improving the effectiveness of applying dynamic analysis to detect android malware. dynamic analysis uses predefined scripts that will be executed while the application is running in an emulator or real device in order to collect several behaviour indicators. After a static analysis of an android package (apk), further insights and possible vulnerabilities can be identified through a dynamic analysis. frida is a toolkit for dynamically analysing android devices or rather their installed apps and running processes. Android pentesting involves a combination of static and dynamic analysis techniques. a properly configured lab with emulators, tools like mobsf, adb, and burp, is essential for testing android applications effectively. Unlike static analysis, dynamic analysis involves running the android app on a physical device or emulator while actively monitoring its behavior. testers look for real time vulnerabilities, including authentication issues, session management flaws, and data leakage.
Comments are closed.