Digital Signature Using Rsa
Github Santoshpanna Digital Signature Using Rsa Implementation Of In this article, we will learn about the rsa signature scheme, attacks on the rsa digital signature scheme, and the steps of digital signature process creation. Digital signatures rsa: sign verify examples let's demonstrate in practice the rsa sign verify algorithm. we shall use the pycryptodome package in python to generate rsa keys.
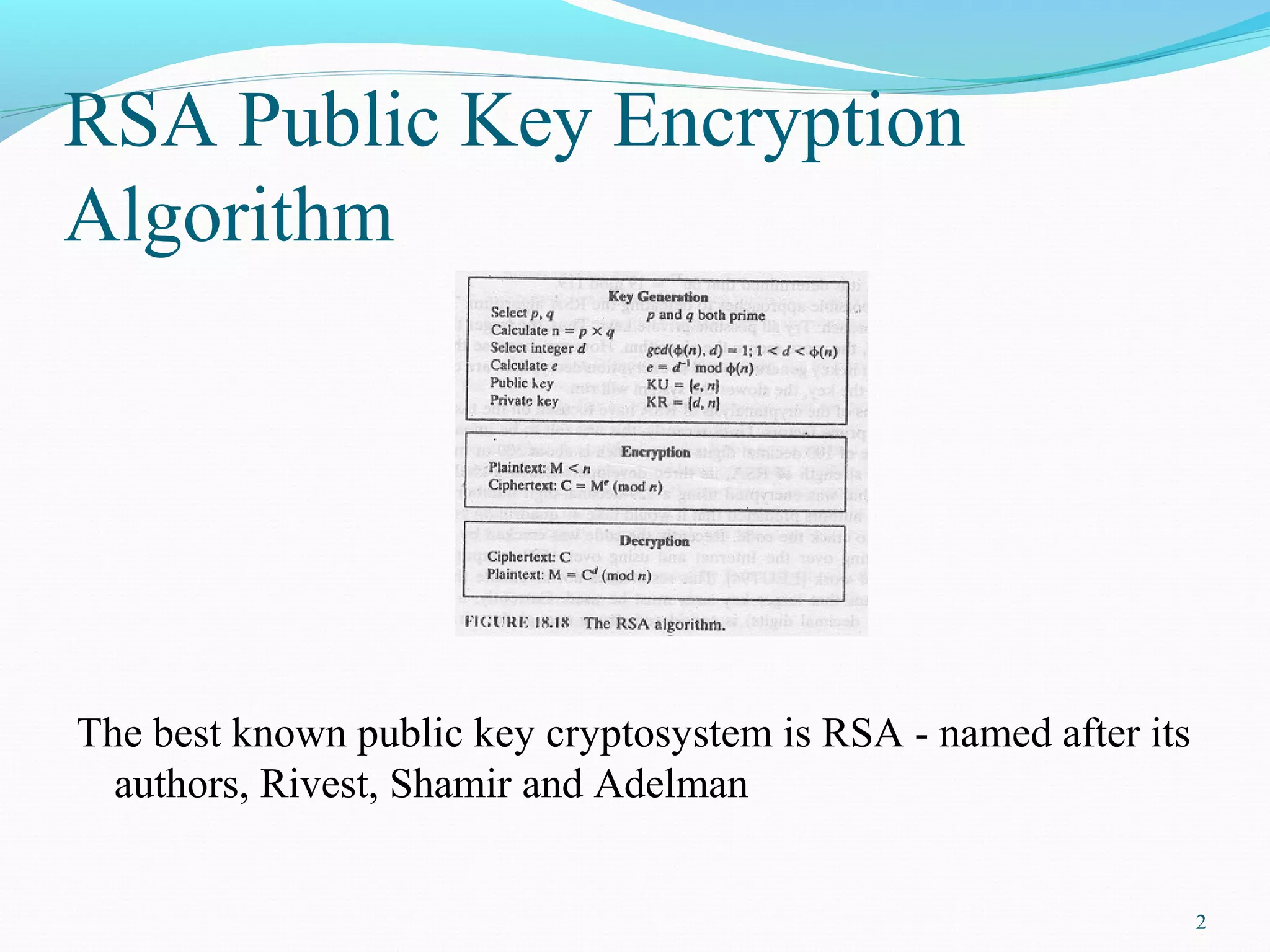
Digital Signature Recognition Using Rsa Algorithm Ppt This article dives deep into rsa algortihm, offering a step by step guide to the implementation specifically for digital signatures in python without relying on external libraries. To demonstrate the pkcs#1 rsa digital signatures, we shall use the following code, based on the pycryptodome python library, which implements rsa sign verify, following the pkcs#1 v1.5 specification:. Rsa digital signatures rely on the mathematical foundations of modular exponentiation and prime numbers. in this section, we'll explore the key generation process, signing, and verification. The use of digital signatures represent rsa's dual nature – the same mathematical foundation serves secrecy and authentication. for us to understand how to flip the key usage, you now understand how to use one of cryptography's most powerful tools.
Digital Signature Recognition Using Rsa Algorithm Ppt Rsa digital signatures rely on the mathematical foundations of modular exponentiation and prime numbers. in this section, we'll explore the key generation process, signing, and verification. The use of digital signatures represent rsa's dual nature – the same mathematical foundation serves secrecy and authentication. for us to understand how to flip the key usage, you now understand how to use one of cryptography's most powerful tools. Learn to create, sign, and verify digital signatures with rsa and openssl. understand how private and public keys ensure message authenticity and integrity in cryptography. This article explains rsa encryption for digital signatures, legal compliance, and compares platforms like docusign and esignglobal for secure esigning. In this chapter, we will discuss the rsa digital signature scheme. the rsa paper1 was tremendously influential because it gave the first constructions of digital signatures and public key encryption. Applying encryption in addition to signing a message is quite simple and is described in the next section. if alice wants to sign and encrypt a message, she can follow the diagram on the bottom left, starting at the bottom of the diagram with a plaintext message and traveling clockwise.
Comments are closed.