Digital Signature Using Rsa Algorithm
Digital Signature Recognition Using Rsa Algorithm Ppt In this article, we will learn about the rsa signature scheme, attacks on the rsa digital signature scheme, and the steps of digital signature process creation. The implementation described above outlines the foundational steps of creating and verifying digital signatures with the rsa algorithm in python. below is an example output of the signing.
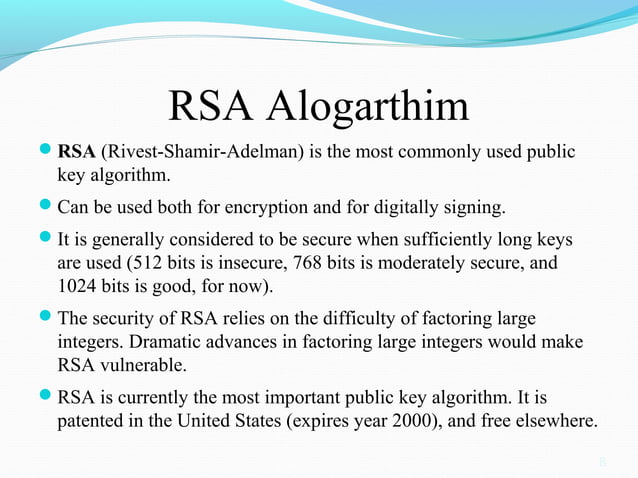
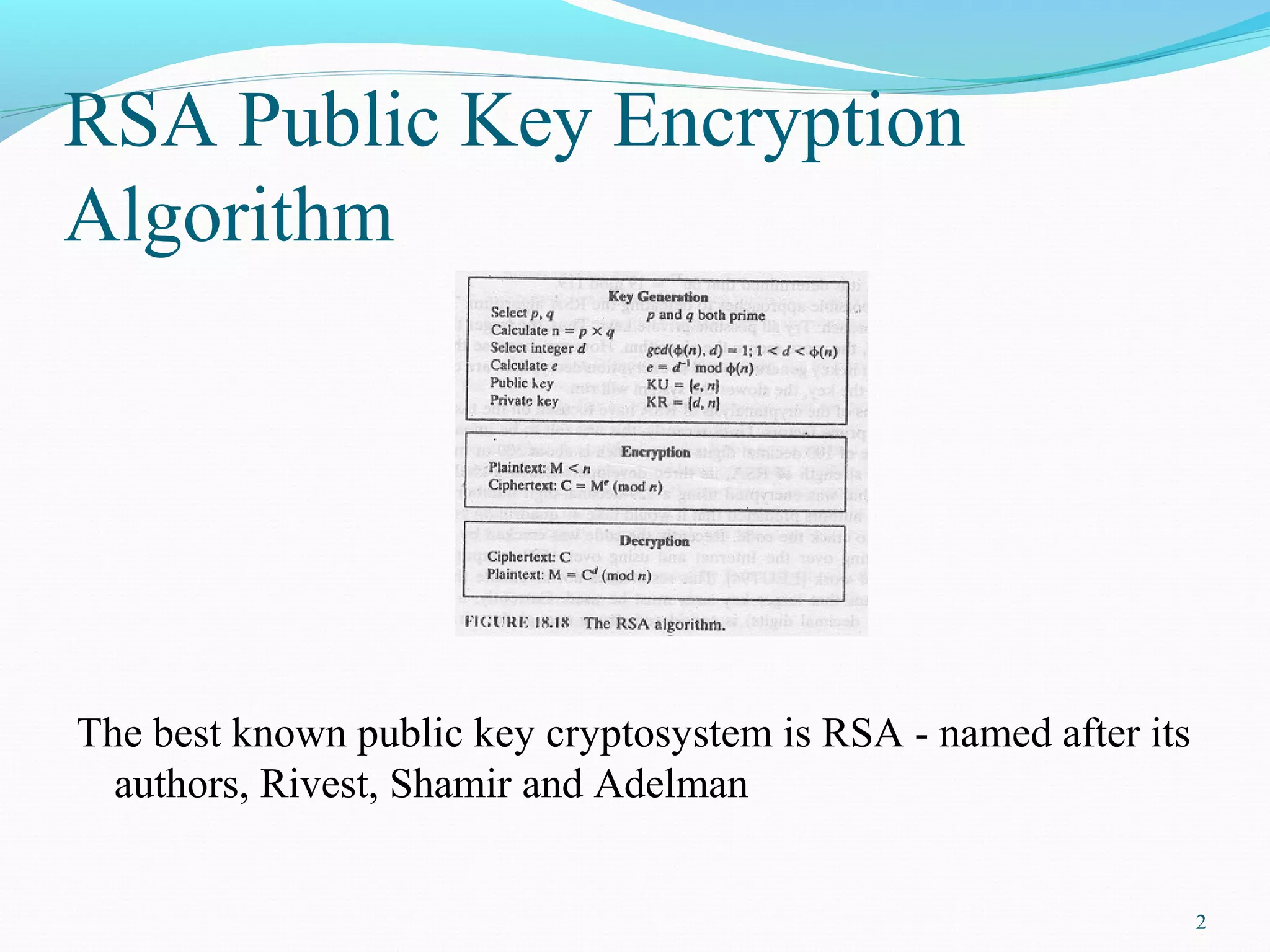
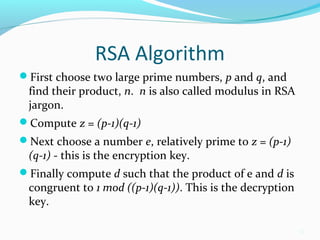
Digital Signature Recognition Using Rsa Algorithm Ppt The aim of this study is to present an improved algorithm modified from rsa for signing and verifying digital signatures. the main goal is to optimize computing resources in modular multiplication and modular square operations. The rsa public key cryptosystem provides a digital signature scheme (sign verify), based on the math of the modular exponentiations and discrete logarithms and the computational difficulty of the rsa problem. Rsa digital signatures rely on the mathematical foundations of modular exponentiation and prime numbers. in this section, we'll explore the key generation process, signing, and verification. The article commences by laying the foundational knowledge of public key cryptographic systems, with a focus on rsa encryption and digital signature technology.
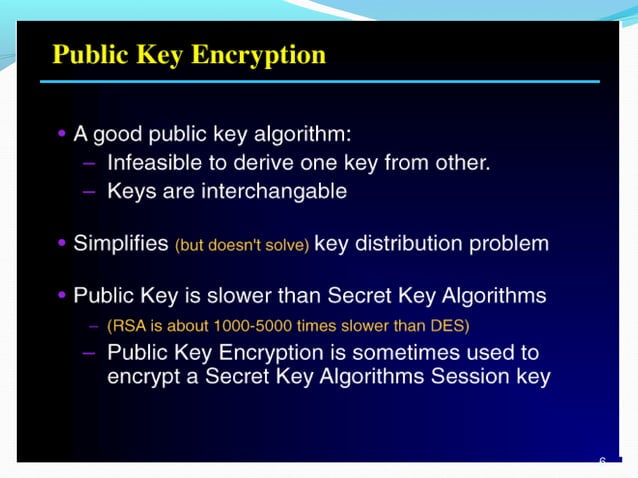
Digital Signature Recognition Using Rsa Algorithm Ppt Rsa digital signatures rely on the mathematical foundations of modular exponentiation and prime numbers. in this section, we'll explore the key generation process, signing, and verification. The article commences by laying the foundational knowledge of public key cryptographic systems, with a focus on rsa encryption and digital signature technology. This article explains rsa encryption for digital signatures, legal compliance, and compares platforms like docusign and esignglobal for secure esigning. The rsa digital signature algorithm is a cryptographic technique used to ensure the authenticity and integrity of a message. its security is underpinned by the mathematical principles of number theory, particularly the difficulty of factoring large composite numbers. Applying encryption in addition to signing a message is quite simple and is described in the next section. if alice wants to sign and encrypt a message, she can follow the diagram on the bottom left, starting at the bottom of the diagram with a plaintext message and traveling clockwise. Digital signatures are used to verify the authenticity of the message sent electronically. a digital signature algorithm uses a public key system. the intended transmitter signs his her message with his her private key and the intended receiver verifies it with the transmitter’s public key.
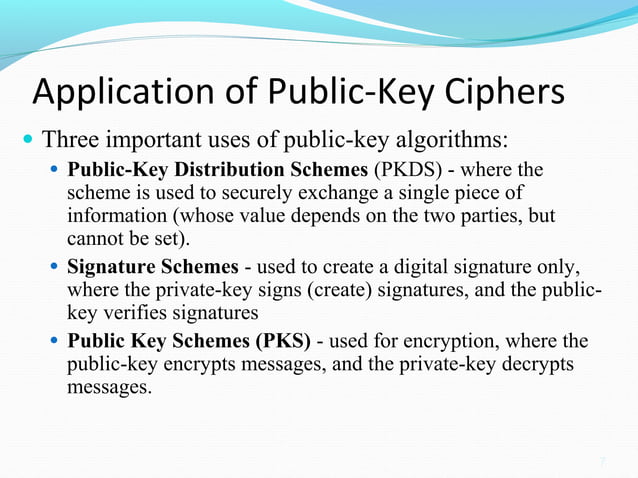
Digital Signature Recognition Using Rsa Algorithm Ppt This article explains rsa encryption for digital signatures, legal compliance, and compares platforms like docusign and esignglobal for secure esigning. The rsa digital signature algorithm is a cryptographic technique used to ensure the authenticity and integrity of a message. its security is underpinned by the mathematical principles of number theory, particularly the difficulty of factoring large composite numbers. Applying encryption in addition to signing a message is quite simple and is described in the next section. if alice wants to sign and encrypt a message, she can follow the diagram on the bottom left, starting at the bottom of the diagram with a plaintext message and traveling clockwise. Digital signatures are used to verify the authenticity of the message sent electronically. a digital signature algorithm uses a public key system. the intended transmitter signs his her message with his her private key and the intended receiver verifies it with the transmitter’s public key.
Digital Signature Recognition Using Rsa Algorithm Ppt Applying encryption in addition to signing a message is quite simple and is described in the next section. if alice wants to sign and encrypt a message, she can follow the diagram on the bottom left, starting at the bottom of the diagram with a plaintext message and traveling clockwise. Digital signatures are used to verify the authenticity of the message sent electronically. a digital signature algorithm uses a public key system. the intended transmitter signs his her message with his her private key and the intended receiver verifies it with the transmitter’s public key.
Digital Signature Recognition Using Rsa Algorithm Ppt
Comments are closed.