Differential Power Analysis

Differential Power Analysis Pdf Differential power analysis (dpa) is a side channel attack which involves statistically analyzing power consumption measurements from a cryptosystem. the attack exploits biases varying power consumption of microprocessors or other hardware while performing operations using secret keys. This paper examines specific methods for analyzing power consumption measurements to find secret keys from tamper resistant devices. we also discuss approaches for building cryptosystems that can operate securely in existing hardware that leaks information.
Github Toj112 Differential Power Analysis Cpa Learning Keyw ords: di eren tial p o w er analysis, dp a, sp a, cryptanalysis, des 1 bac kground a ttac ks that in v olv em ultiple parts of a securit y system are di cult to predict and mo del. Learn how to perform differential power analysis (dpa) on aes encryption algorithm using matlab and picoscope. this tutorial covers the theory, method, steps, and examples of dpa for beginners. Learn how differential power analysis (dpa) and simple power analysis (spa) work and how to prevent them. dpa and spa are methods of extracting secret keys or data from a device by analyzing its power consumption. This paper examines specific methods for analyzing power consumption measurements to find secret keys from tamper resistant devices. we also discuss approaches for building cryptosystems that can operate securely in existing hardware that leaks information.
Differential Power Analysis Overview Download Scientific Diagram Learn how differential power analysis (dpa) and simple power analysis (spa) work and how to prevent them. dpa and spa are methods of extracting secret keys or data from a device by analyzing its power consumption. This paper examines specific methods for analyzing power consumption measurements to find secret keys from tamper resistant devices. we also discuss approaches for building cryptosystems that can operate securely in existing hardware that leaks information. Power analysis is a form of side channel attack in which operation and key material can be exposed through the measurement of a cryptographic device’s power consumption. Differential power analysis (dpa) is a highly effective side channel attack (sca) that exploits the minute changes in a device's power consumption patterns to extract sensitive information. Differential power analysis is a powerful tool attackers used to extract secret keys and compromise the security of tamper resistant devices. dpa is a side channel attack that is extremely effective low cost and widely known. The differential power analysis (dpa) attack aims at extracting sensitive information that is processed by the operations in a cryptographic primitive. power traces are collected and subsequently processed using statistical methods.
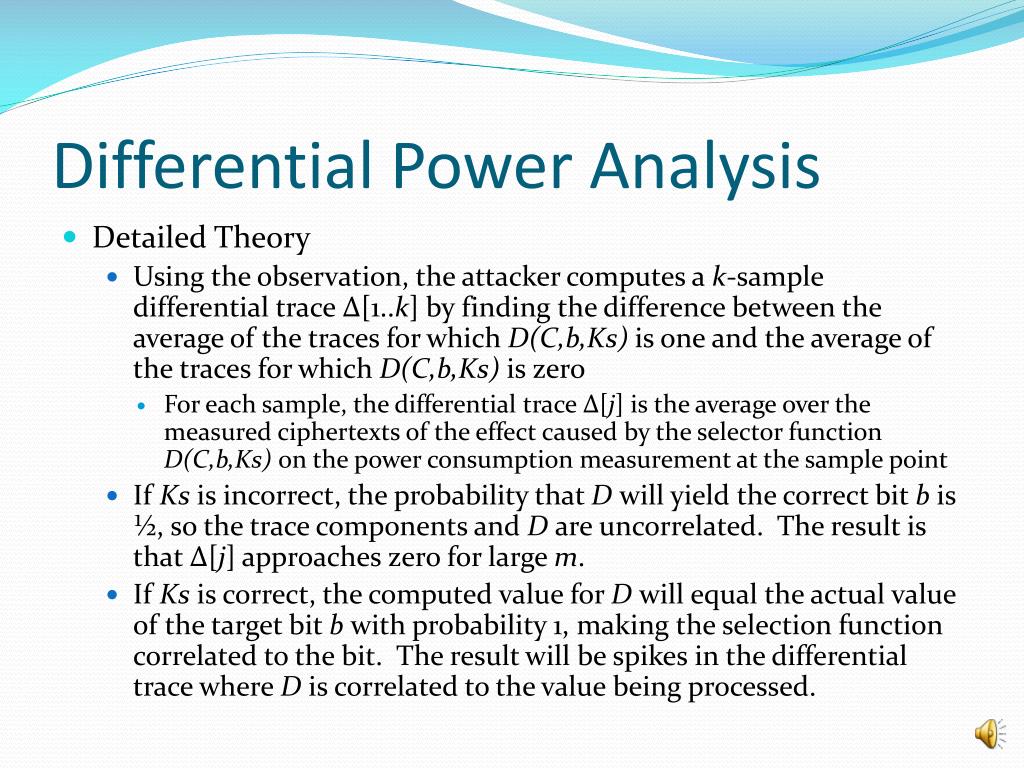
Ppt Differential Power Analysis Powerpoint Presentation Free Power analysis is a form of side channel attack in which operation and key material can be exposed through the measurement of a cryptographic device’s power consumption. Differential power analysis (dpa) is a highly effective side channel attack (sca) that exploits the minute changes in a device's power consumption patterns to extract sensitive information. Differential power analysis is a powerful tool attackers used to extract secret keys and compromise the security of tamper resistant devices. dpa is a side channel attack that is extremely effective low cost and widely known. The differential power analysis (dpa) attack aims at extracting sensitive information that is processed by the operations in a cryptographic primitive. power traces are collected and subsequently processed using statistical methods.

Ppt Differential Power Analysis Powerpoint Presentation Free Differential power analysis is a powerful tool attackers used to extract secret keys and compromise the security of tamper resistant devices. dpa is a side channel attack that is extremely effective low cost and widely known. The differential power analysis (dpa) attack aims at extracting sensitive information that is processed by the operations in a cryptographic primitive. power traces are collected and subsequently processed using statistical methods.

Ppt Differential Power Analysis Powerpoint Presentation Free
Comments are closed.