Devman Malware Analysis Overview By Any Run
Devman Malware Analysis Overview By Any Run By querying suspicious files or network indicators against a vast database of malware samples analyzed in the sandbox by over 15k socs worldwide, security teams can quickly determine whether observed activity relates to known devman campaigns. Devman is a fast evolving malware family targeting windows environments with a mix of credential theft, remote control capabilities, and persistence techniques typical of modern crimeware.

Devman Malware Analysis Overview By Any Run Any.run offers a comprehensive suite of cybersecurity solutions, including their interactive sandbox and advanced threat intelligence services. trusted by over 15,000 companies worldwide, any.run enables dynamic malware analysis across windows, linux, and android systems. Any.run researchers identified the malware through comprehensive sandbox analysis, revealing its complex inheritance from the conti ransomware framework that forms dragonforce’s foundation. In early april 2025, an actor presenting itself as “devman” has claimed on x1 to gain access and perform a ransomware attack against the french transport company “doumen”. Built upon combined elements from the dragonforce and conti codebases, this hybrid ransomware is currently targeting windows 10 and windows 11 users, introducing a blend of aggression, experimentation, and inexperience that could define the next stage of ransomware evolution.

Devman Malware Analysis Overview By Any Run In early april 2025, an actor presenting itself as “devman” has claimed on x1 to gain access and perform a ransomware attack against the french transport company “doumen”. Built upon combined elements from the dragonforce and conti codebases, this hybrid ransomware is currently targeting windows 10 and windows 11 users, introducing a blend of aggression, experimentation, and inexperience that could define the next stage of ransomware evolution. Attack: a newly identified ransomware variant, devman, has emerged from the dragonforce codebase, introducing distinct traits and operational quirks. it is primarily active in asia and africa and operates a dedicated leak site known as devman's place. This capability seems to be a legacy of conti ransomware, which inspired dragonforce and devman. as part of this legacy, the ransomware use a hard coded mutex to prevent multiple instances from running in parallel. This analysis breaks down the technical anatomy of devman—from its c origins to its modern rust architecture—and provides actionable intelligence for detection and response teams.
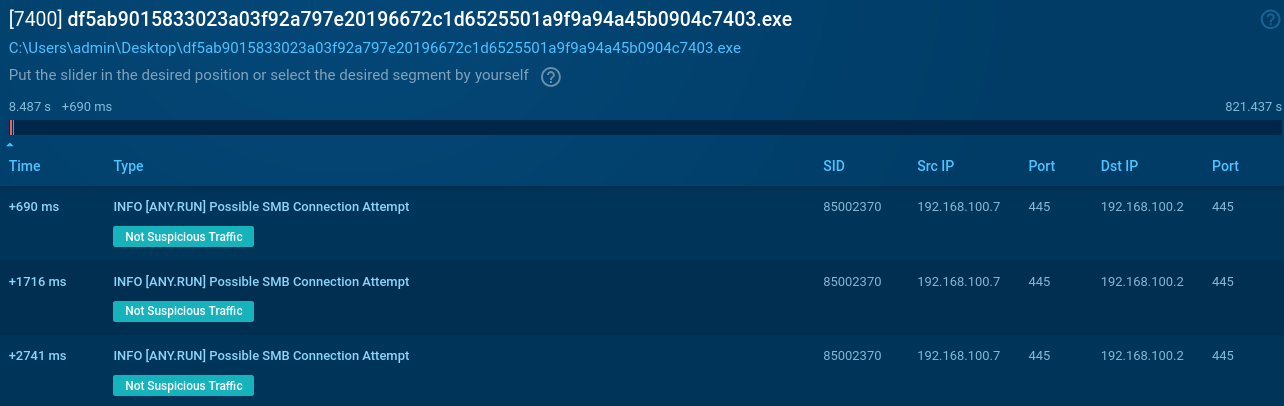
Devman Malware Analysis Overview By Any Run Attack: a newly identified ransomware variant, devman, has emerged from the dragonforce codebase, introducing distinct traits and operational quirks. it is primarily active in asia and africa and operates a dedicated leak site known as devman's place. This capability seems to be a legacy of conti ransomware, which inspired dragonforce and devman. as part of this legacy, the ransomware use a hard coded mutex to prevent multiple instances from running in parallel. This analysis breaks down the technical anatomy of devman—from its c origins to its modern rust architecture—and provides actionable intelligence for detection and response teams.
Comments are closed.