Deploy With Seqrite Product Documentation

Product Documentation Deploy with seqrite select the deploy with seqrite option, click continue. after electing your organization type as per the guide present on the left, click i agree. the deployment starts. after the successful deployment, a success message appears on the screen. the discovery realm url is displayed. you can download the logs, if required. Seqrite eps is a centralized, robust security platform, often built by quick heal, that gives you a single web based console to manage antivirus, firewall, patch management, and even advanced features like data loss prevention dlp across all your employee devices, from laptops to servers.
Deploy With Seqrite Product Documentation Installation and usage of seqrite endpoint security is subject to user’s unconditional acceptance of the seqrite end user license terms and conditions. to read the license terms, visit seqrite eula and check the end user license agreement for your product. This document outlines the standard operating procedure for seqrite endpoint security 7.4, including its server and client versions. Once you subscribe, seqrite sends you an email containing url and license key to download and install the setup for seqrite endpoint security. after installation, you need to activate eps with help of valid license key. Welcome to the library of digital documents for the seqrite products. you can read the product documents in english and other languages also. select your product first and then the language of choice.

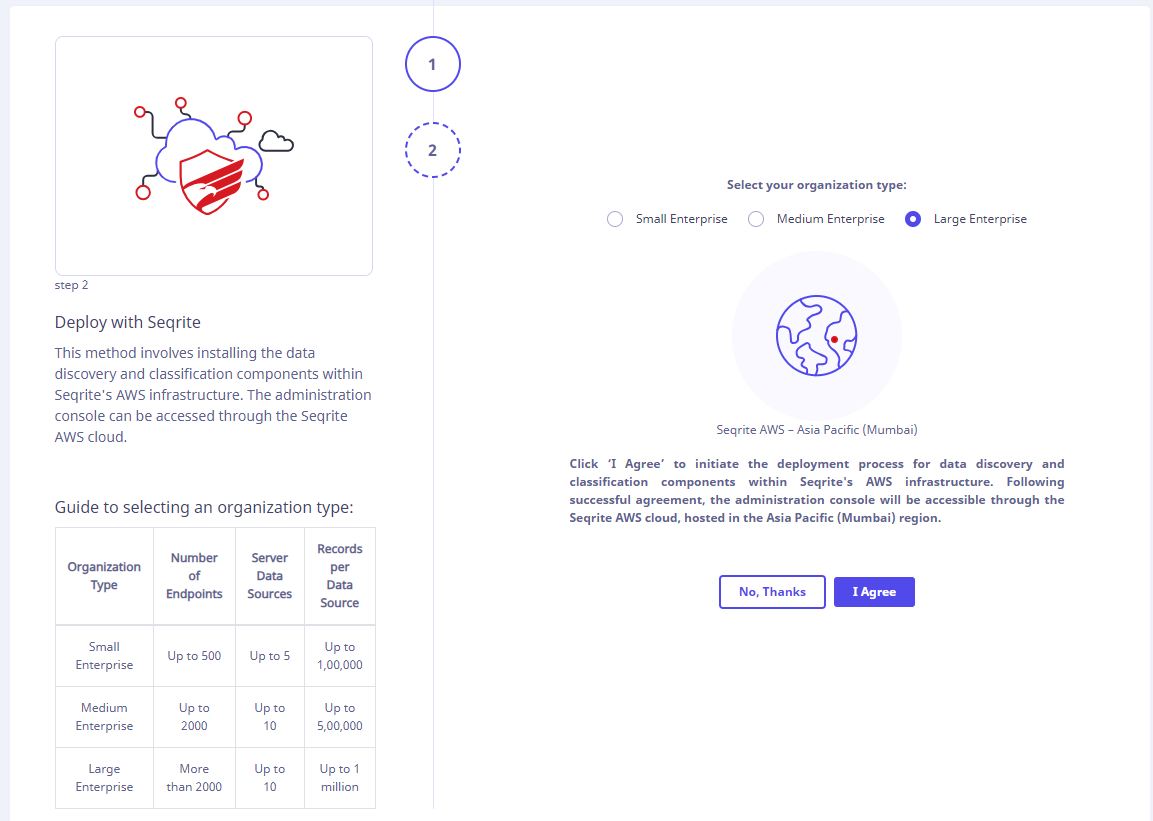
Deploy With Seqrite Product Documentation Once you subscribe, seqrite sends you an email containing url and license key to download and install the setup for seqrite endpoint security. after installation, you need to activate eps with help of valid license key. Welcome to the library of digital documents for the seqrite products. you can read the product documents in english and other languages also. select your product first and then the language of choice. Deployment methods select one of the following methods to deploy the seqrite endpoint protection client as applicable. a brief about each method is mentioned below. After the tenant signs up for seqrite data privacy, the deployment wizard page opens. on the welcome screen, click proceed. this is the first step where the tenant has to select a deployment model as per their organizational need. choose the deployment method based on your organizational requirement. click continue. a new page appears. Here, you can explore our product documentation available in english and multiple other languages. simply select your product and choose your preferred language from the drop down menu. Access seqrite manuals for endpoint protection, xdr, and ztna. find guides for installation, configuration, and usage to optimize your security solutions.

Deploy With Seqrite Product Documentation Deployment methods select one of the following methods to deploy the seqrite endpoint protection client as applicable. a brief about each method is mentioned below. After the tenant signs up for seqrite data privacy, the deployment wizard page opens. on the welcome screen, click proceed. this is the first step where the tenant has to select a deployment model as per their organizational need. choose the deployment method based on your organizational requirement. click continue. a new page appears. Here, you can explore our product documentation available in english and multiple other languages. simply select your product and choose your preferred language from the drop down menu. Access seqrite manuals for endpoint protection, xdr, and ztna. find guides for installation, configuration, and usage to optimize your security solutions.
Comments are closed.