Decompiling Stack Strings In Ghidra
Github Zxgio Ghidra Stack Strings A Script To Detect Stack Strings Decompiling stack strings in ghidra (with emulation). in a previous post i wrote a script to transform strings dynamically constructed out of packed long words into the full, readable string. Hacky scripts to fixup stack strings in ghidra's decompiler. saml98 ghidrastackstrings.

Decompiling Stack Strings In Ghidra With Emulation R Reverseengineering In this post, i’ll be discussing how to use the ghidra decompiler to identify strings being constructed on the stack at runtime. this stack string technique is an easy way for a programmer to obscure string data within a program by blending it as opaque operand instructions. Understanding how to effectively analyze assembly code, especially when ghidra's decompilation falls short, is essential. this guide will help you navigate these challenges, providing practical techniques to interpret assembly instructions and trace string operations. This article will provide insight into stack strings, the endianness of values, how to handle (encrypted) stack strings, and the step by step creation of a ghidra script which handles (wide) stack strings, which may or may not be encrypted. Stack string explorer searches through targeted binaries, finding constant strings and reconstructing their different components to recover the full string.
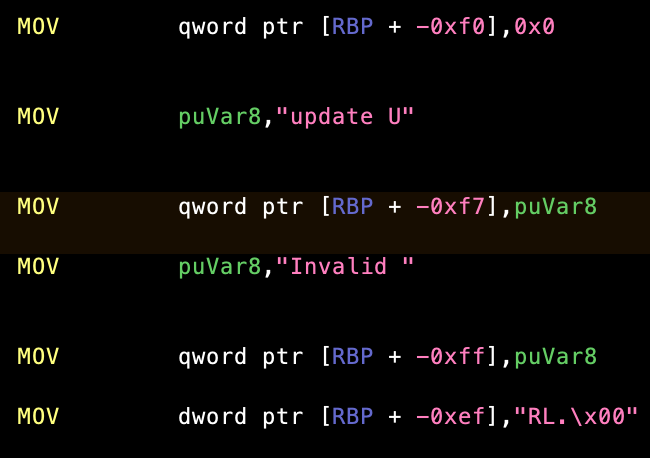
Decompiling Stack Strings In Ghidra This article will provide insight into stack strings, the endianness of values, how to handle (encrypted) stack strings, and the step by step creation of a ghidra script which handles (wide) stack strings, which may or may not be encrypted. Stack string explorer searches through targeted binaries, finding constant strings and reconstructing their different components to recover the full string. This is helpful, but i'm asking if there's a way to set the data types such that there is a char array on the stack. the script (s) you linked only set comments as to what the strings are. These errors are due to one non returning function that ghidra doesn't know about. identify this function and mark it as non returning (right click on the name of the function in the decompiler, select edit function signature, and then check the no return box). Is there some way to make ghidra's decompiler use the complete 404 bytes block allocated by the function as an austack404 thus bypassing ghidra's flawed interpretation logic and actually preserve the original functionality of the asm code?. In a previous post i wrote a script to transform strings dynamically constructed out of packed long words into the full, readable string.
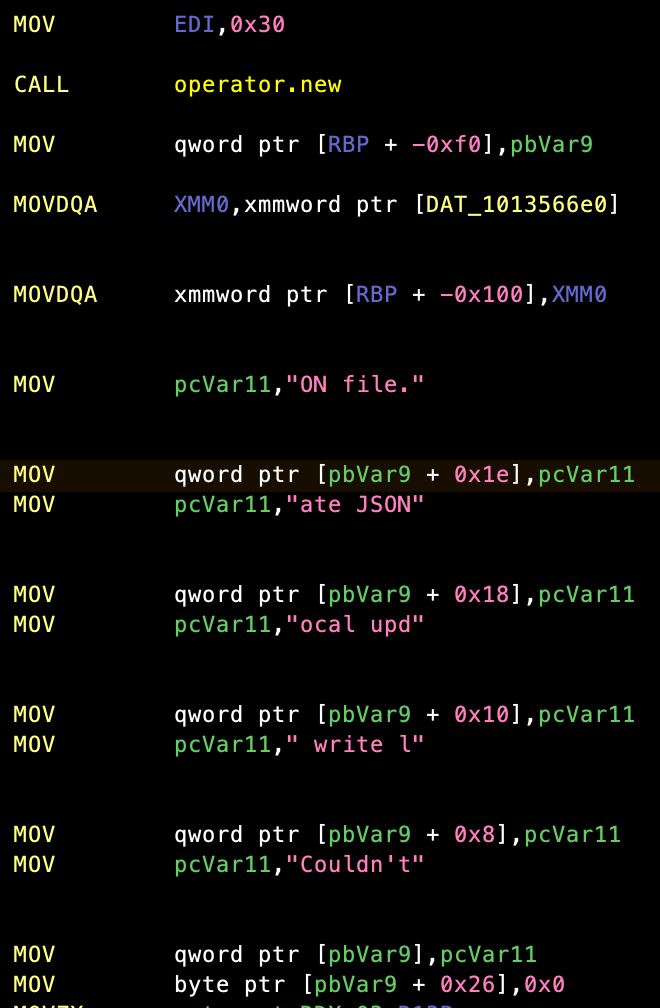
Decompiling Stack Strings In Ghidra This is helpful, but i'm asking if there's a way to set the data types such that there is a char array on the stack. the script (s) you linked only set comments as to what the strings are. These errors are due to one non returning function that ghidra doesn't know about. identify this function and mark it as non returning (right click on the name of the function in the decompiler, select edit function signature, and then check the no return box). Is there some way to make ghidra's decompiler use the complete 404 bytes block allocated by the function as an austack404 thus bypassing ghidra's flawed interpretation logic and actually preserve the original functionality of the asm code?. In a previous post i wrote a script to transform strings dynamically constructed out of packed long words into the full, readable string.
Decompiling Stack Strings In Ghidra Is there some way to make ghidra's decompiler use the complete 404 bytes block allocated by the function as an austack404 thus bypassing ghidra's flawed interpretation logic and actually preserve the original functionality of the asm code?. In a previous post i wrote a script to transform strings dynamically constructed out of packed long words into the full, readable string.
Comments are closed.