Dataparc Security Best Practices

Best Practices Data Center Security Pdf Information Security This document outlines best practices based on industry standards and dataparc’s practical experience. please use it as a set of guidelines, keeping in mind that each customer will likely require somewhat individualized configuration. In this article, we will explore 10 data security best practices that every organization and individual should adopt to mitigate risks, prevent breaches, and secure valuable data from ever growing cyber threats.
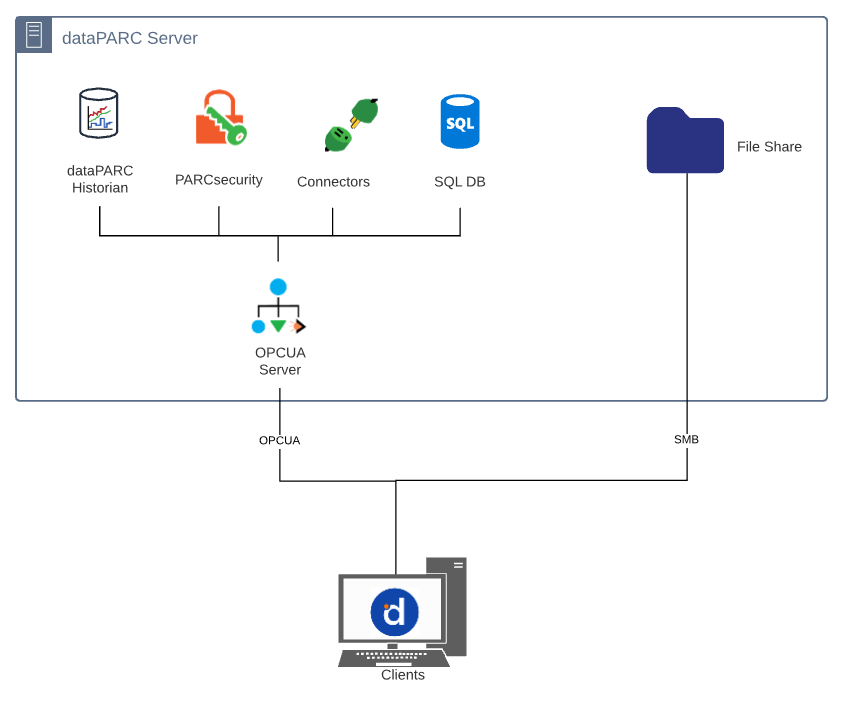
Dataparc Security Best Practices Delivers advanced security and identity access management to the historian configuration interface. dataparc’s security bubble controls access to who can configure or access the data, and encrypts communication between historians, collectors, and clients. Explore essential data center security best practices for 2025 to protect hybrid environments, ensure compliance, and mitigate evolving cyber threats. While many organizations deploy security differently, there are patterns and features that are commonly used by most organizations. here are the most relevant controls to define, deploy and monitor your security posture according to our best practices. Implementing safe cybersecurity best practices is important for individuals as well as organizations of all sizes. using strong passwords, updating your software, thinking before you click on suspicious links, and turning on multi factor authentication are the basics of what we call “cyber hygiene” and will drastically improve your online.
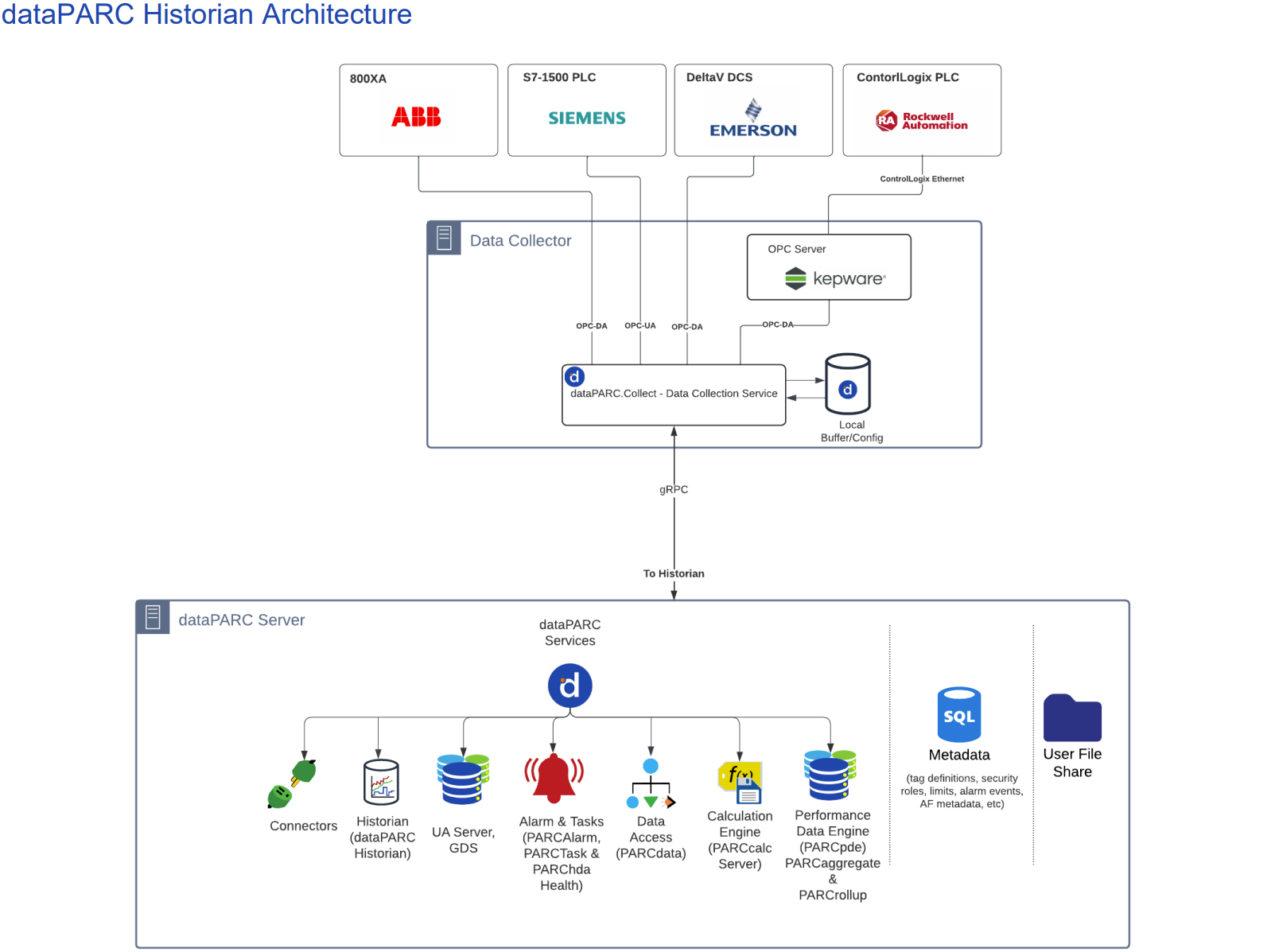
Dataparc Security Best Practices While many organizations deploy security differently, there are patterns and features that are commonly used by most organizations. here are the most relevant controls to define, deploy and monitor your security posture according to our best practices. Implementing safe cybersecurity best practices is important for individuals as well as organizations of all sizes. using strong passwords, updating your software, thinking before you click on suspicious links, and turning on multi factor authentication are the basics of what we call “cyber hygiene” and will drastically improve your online. Use the guidelines in this site to plan, deploy, and maintain your data center best practice security policy. Dataparc security best practices in today’s business environment, security of the entire spectrum of systems from individual data points to networks at large has taken on the utmost importance. dataparc’s overall architectur. 今日のビジネス環境では、個々のデータポイントからネットワーク全体に至るまで、あらゆるシステムのセキュリティが最も重要になっています。 dataparcの全体的なアーキテクチャと特定のツールにより、組織のitおよびotセキュリティプロトコルを損なうことなく、ユーザーが必要なデータや情報への安全なアクセスを容易にします。 このドキュメントでは、業界標準とdataparcの実践経験に基づいたベストプラクティスの概要を説明します。 お客様ごとにある程度個別の構成が必要になる可能性が高いことを念頭に置いて、一連のガイドラインとして使用してください。. This overview provides visibility into our security controls, compliance practices, and the measures we take to safeguard our customers’ operational and production data.

Dataparc Historian Architecture Best Practices Use the guidelines in this site to plan, deploy, and maintain your data center best practice security policy. Dataparc security best practices in today’s business environment, security of the entire spectrum of systems from individual data points to networks at large has taken on the utmost importance. dataparc’s overall architectur. 今日のビジネス環境では、個々のデータポイントからネットワーク全体に至るまで、あらゆるシステムのセキュリティが最も重要になっています。 dataparcの全体的なアーキテクチャと特定のツールにより、組織のitおよびotセキュリティプロトコルを損なうことなく、ユーザーが必要なデータや情報への安全なアクセスを容易にします。 このドキュメントでは、業界標準とdataparcの実践経験に基づいたベストプラクティスの概要を説明します。 お客様ごとにある程度個別の構成が必要になる可能性が高いことを念頭に置いて、一連のガイドラインとして使用してください。. This overview provides visibility into our security controls, compliance practices, and the measures we take to safeguard our customers’ operational and production data.
Comments are closed.