Database Security Omscs Notes
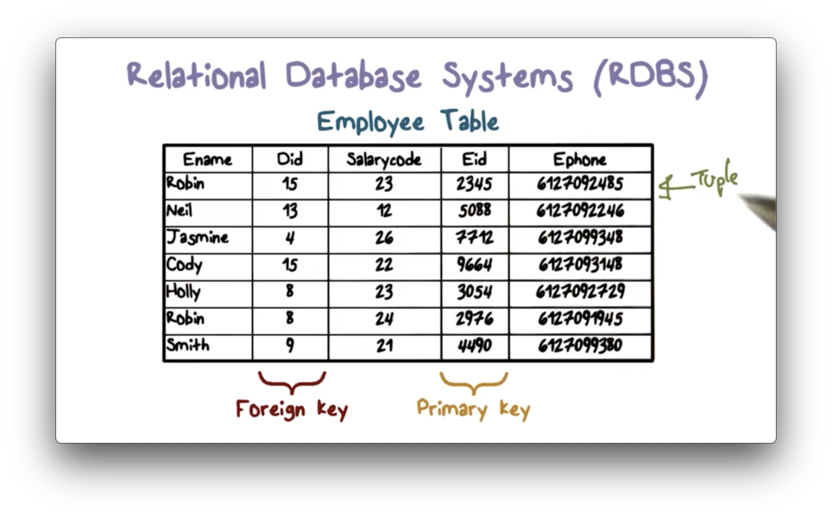
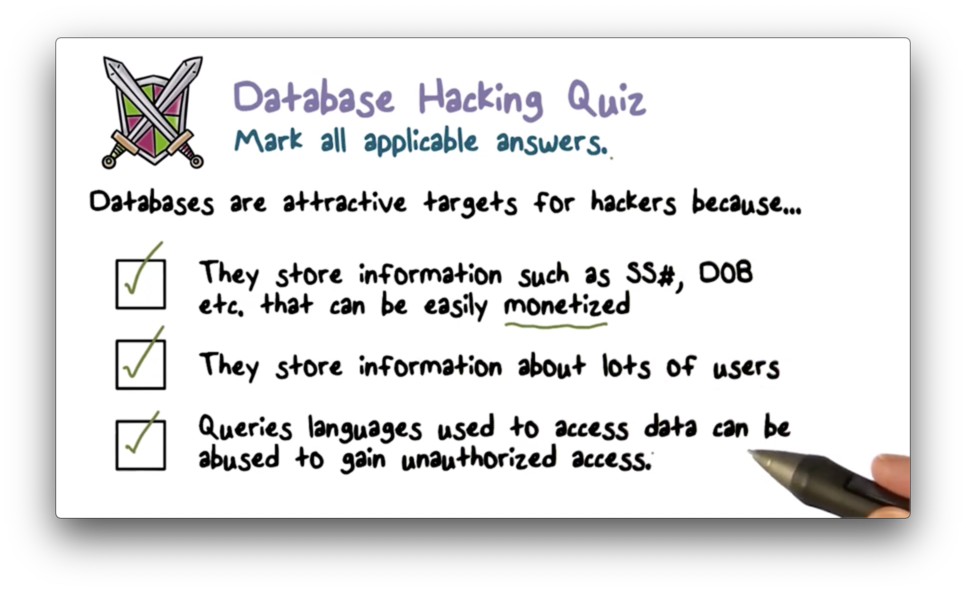
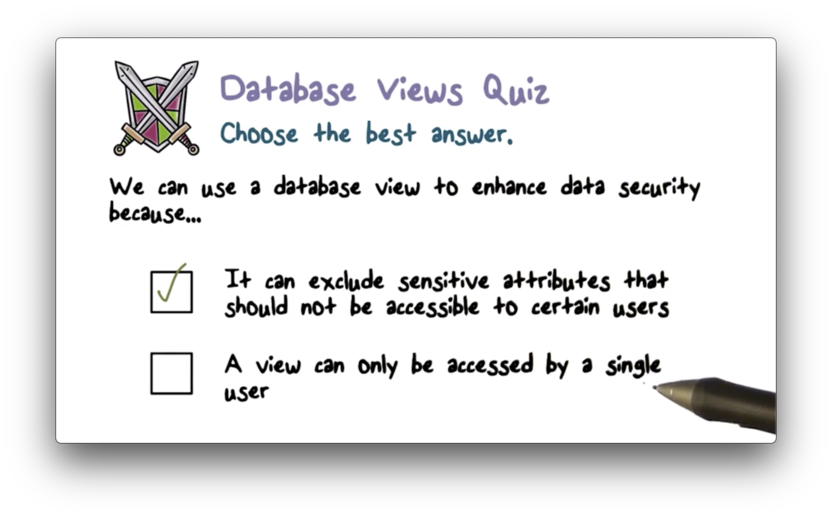
Database Security Omscs Notes Databases store massive amounts of sensitive data. when hackers steal millions of customer records from a company often containing data like social security numbers, addresses, and credit card numbers they usually steal this information from one or more databases. Databases might contain sensitive information like medical records. we use access controls to manage this just like we would for files. the main difference with a database is that the data is structured, there is a schema that defines relationships within the database.
Database Security Omscs Notes The raw markdown notes for omscs notes. contribute to m4ttsch omscs notes notes development by creating an account on github. All notes from the courses i took at georgia tech for my master's program in computer science. Wrapping up my third semester in georgia tech’s omscs program, here's what i learnt from cs 6035 (introduction to information security). Visit the website below to upload omscs lecture pdfs.
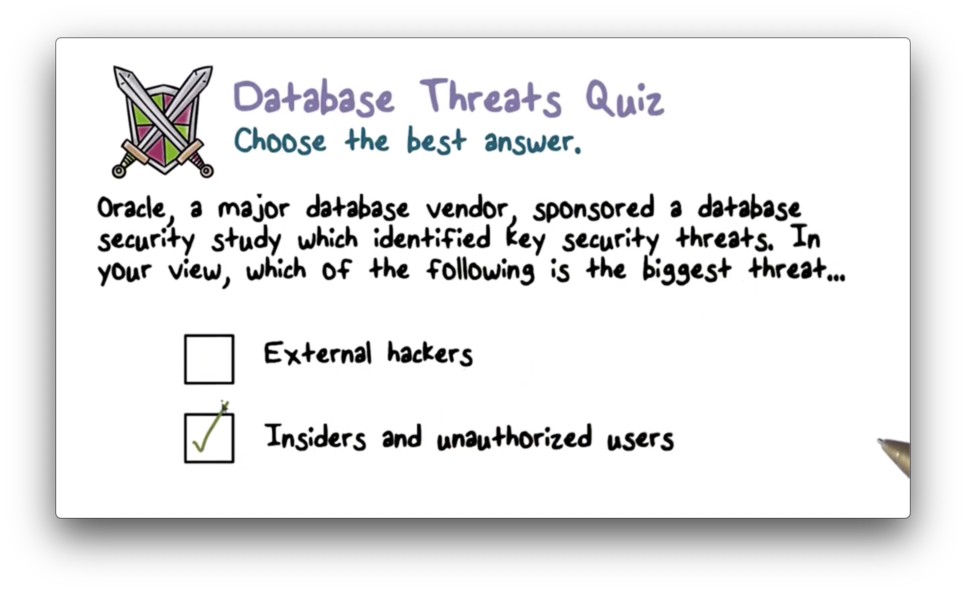
Database Security Omscs Notes Wrapping up my third semester in georgia tech’s omscs program, here's what i learnt from cs 6035 (introduction to information security). Visit the website below to upload omscs lecture pdfs. Select a course below to view the public content for that course. note that students enrolled in omscs should access their course content through canvas, as the for credit versions of these courses may include graded components or recent content updates not available through omscs open courseware. Companies might have labeled data. the blp model can be applied to databases for multi level security. we can read at the same level or at levels we dominate. we can write to the same level, similar to selinux. trusted users can violate these rules. here are some different levels of granularity:. Welcome to lecture notes that are clear, organized, and forever free. i built omscs notes to share my notes with other students in the gatech omscs program. my notes are searchable, navigable, and, most importantly, free. i hope they help you on your journey here. join the party. sign up today. Databases provide centralized control of data, an important feature that enables us to enforce policies across the database, even when that database is distributed.
Database Security Omscs Notes Select a course below to view the public content for that course. note that students enrolled in omscs should access their course content through canvas, as the for credit versions of these courses may include graded components or recent content updates not available through omscs open courseware. Companies might have labeled data. the blp model can be applied to databases for multi level security. we can read at the same level or at levels we dominate. we can write to the same level, similar to selinux. trusted users can violate these rules. here are some different levels of granularity:. Welcome to lecture notes that are clear, organized, and forever free. i built omscs notes to share my notes with other students in the gatech omscs program. my notes are searchable, navigable, and, most importantly, free. i hope they help you on your journey here. join the party. sign up today. Databases provide centralized control of data, an important feature that enables us to enforce policies across the database, even when that database is distributed.
Database Security Omscs Notes Welcome to lecture notes that are clear, organized, and forever free. i built omscs notes to share my notes with other students in the gatech omscs program. my notes are searchable, navigable, and, most importantly, free. i hope they help you on your journey here. join the party. sign up today. Databases provide centralized control of data, an important feature that enables us to enforce policies across the database, even when that database is distributed.
Comments are closed.