Database Hacking Attack Types Defenses Lesson Study

What Is A Cyber Attack Types Effects Prevention A database is a key tool for businesses that can cause serious headaches if breached. in this lesson, you'll learn more about database specific attacks and methods of protecting. Whenever the hackers or the malicious intruders get the access to any of the sensitive data, they can rapidly extract values, impose damage or even create impact on business operations. this can not only lead to financial losses but also the reputation of the industry can get damaged.
Types Of Hacking Attacks Common Techniques Examples And Defenses By This study presents a comprehensive analysis of cyber risks in database management systems, including the classification of threats, vulnerabilities, impacts, and countermeasures. Some lessons, if abused, may result in physical injury. some additional dangers may also exist where there is not enough research on possible effects of emanations from particular technologies. students using these lessons should be supervised yet encouraged to learn, try, and do. Database security refers to the collective measures used to protect a database management system from malicious threats and unauthorized access. in simple terms, it’s making sure that only the right people can get to your data, and that the data stays accurate and available. The main purpose of this paper will be to create an overview of the types of sql attacks and its key defense mechanisms to counter those attacks and protect the user‟s information from injecting sql attacks.
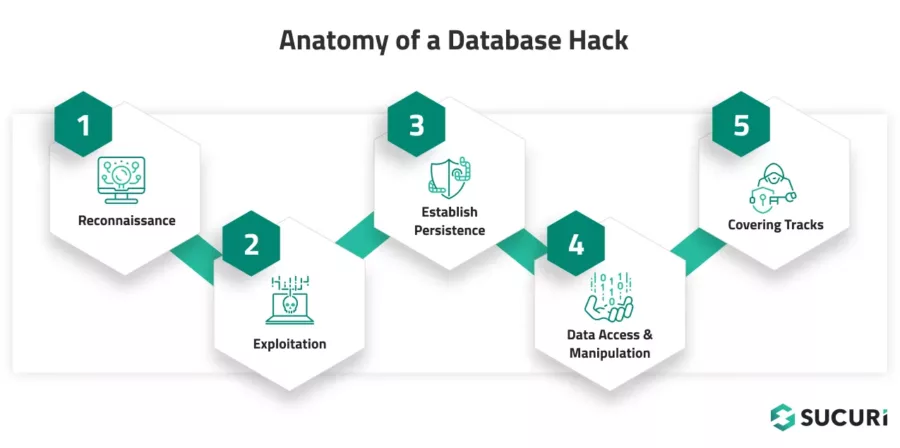
How To Clean Malware From A Hacked Database Sucuri Database security refers to the collective measures used to protect a database management system from malicious threats and unauthorized access. in simple terms, it’s making sure that only the right people can get to your data, and that the data stays accurate and available. The main purpose of this paper will be to create an overview of the types of sql attacks and its key defense mechanisms to counter those attacks and protect the user‟s information from injecting sql attacks. If a database is not properly secured, it can lead to data breaches, financial loss, legal consequences, and reputational damage. let’s dive into some of the most common threats that put. The website provides eight missions that need to be solved where you can apply your knowledge about database security.it also designed to help players of all abilities develop their skills. Oracle, a major database vendor, sponsored a database security study which identified key security threats. in your view, which of the following is the biggest threat. Students will learn how databases work, common vulnerabilities, and tools for database hacking. the course assumes a beginner level knowledge of windows, tcp ip, mysql, ms sql server, and sql statements.
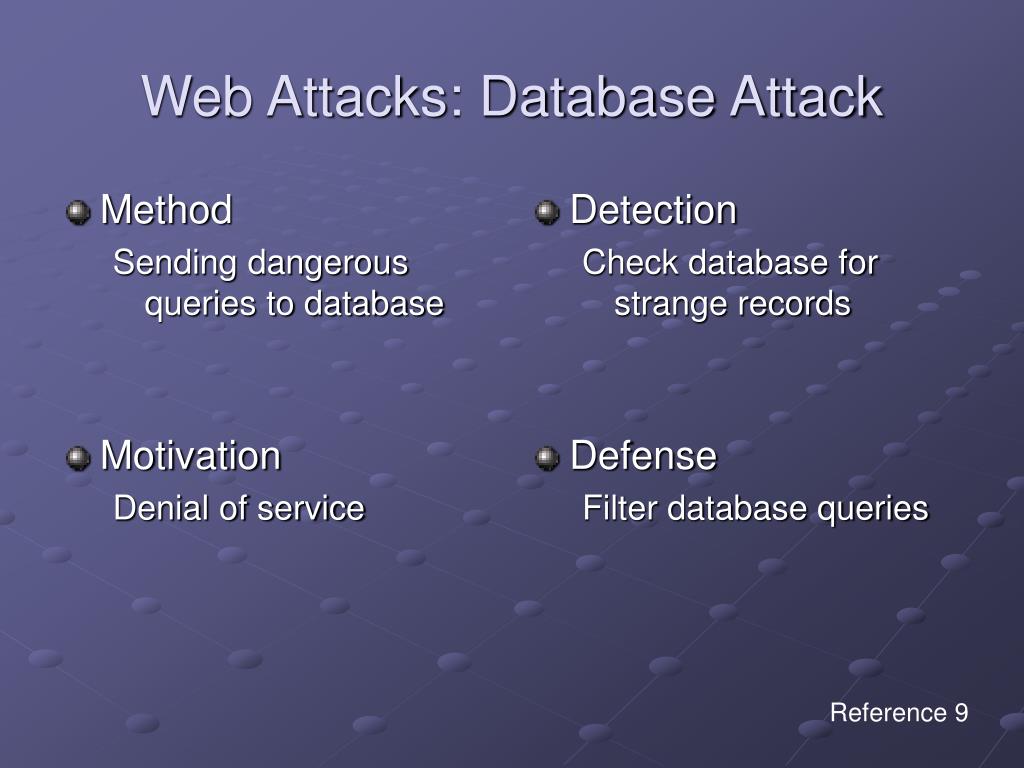
Ppt Attacks And Powerpoint Presentation Free Download Id 5906566 If a database is not properly secured, it can lead to data breaches, financial loss, legal consequences, and reputational damage. let’s dive into some of the most common threats that put. The website provides eight missions that need to be solved where you can apply your knowledge about database security.it also designed to help players of all abilities develop their skills. Oracle, a major database vendor, sponsored a database security study which identified key security threats. in your view, which of the following is the biggest threat. Students will learn how databases work, common vulnerabilities, and tools for database hacking. the course assumes a beginner level knowledge of windows, tcp ip, mysql, ms sql server, and sql statements.
Database Hacking Attack Types Defenses Lesson Study Oracle, a major database vendor, sponsored a database security study which identified key security threats. in your view, which of the following is the biggest threat. Students will learn how databases work, common vulnerabilities, and tools for database hacking. the course assumes a beginner level knowledge of windows, tcp ip, mysql, ms sql server, and sql statements.
Comments are closed.